Continuous Application
Threat Modeling Service
Threat Modeling Under Two Hours with Fork for Real-Time Risk Visibility and Attack Simulation
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
What is Fork?
Fork is a SaaS platform that implements the PASTA framework for threat modeling. Our goal is to create a tool that not only serves the needs of security professionals but also evolves with the contributions of the community.
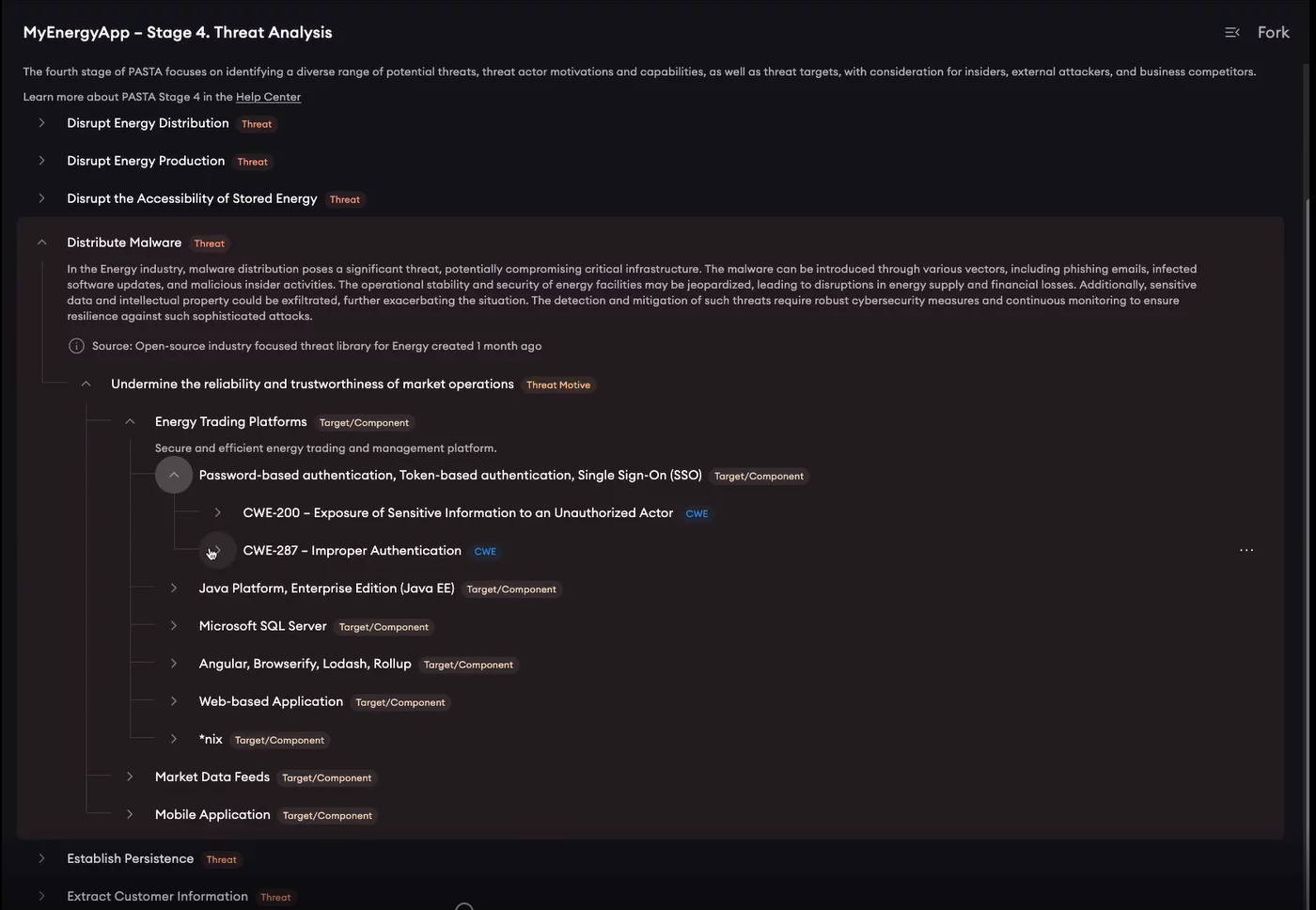
Comprehensive Mapping of Taxonomies
Our ForkTM platform is expanding its scope to encompass mapping all relevant taxonomies. In ForkTM, we strive to provide a holistic approach by integrating both theory and evidence methodologies. Fork’s evidence-based approach complements your threat models and helps identify additional Tactics, Techniques, and Procedures (TTPs) for consideration in the attack tree. These adversarial methods are derived from real-world attacks observed and reported by legitimate sources.
Fork is incorporating threats and adversarial methods derived from multiple categories of observed behavior:
- TTPs used against your Technology Platform(s)
- Software used maliciously against your Industry
- Campaign(s) targeting your Industry
Integrated Insights and Mappings
Our threat libraries are designed as a tree, providing a hierarchical mapping of various security standards, frameworks, and methodologies. Within this tree structure, you can explore different branches such as threats, motives, targets, CWEs (Common Weakness Enumeration), CAPECs (Common Attack Pattern Enumeration and Classification), CVEs (Common Vulnerabilities and Exposures), MITRE ATT&CK post-exploitation patterns along with their corresponding mitigations, and OWASP ASVS (Application Security Verification Standard). This approach allows for an intuitive understanding of how these elements interconnect and relate to one another within your threat models.
Risk Centric Threat Modeling Under Two Hours
Identify risks that are most likely to happen and which create the biggest impact. Harnesses our industry-focused threat libraries and integrate real-time vulnerability data and threat intelligence.
-
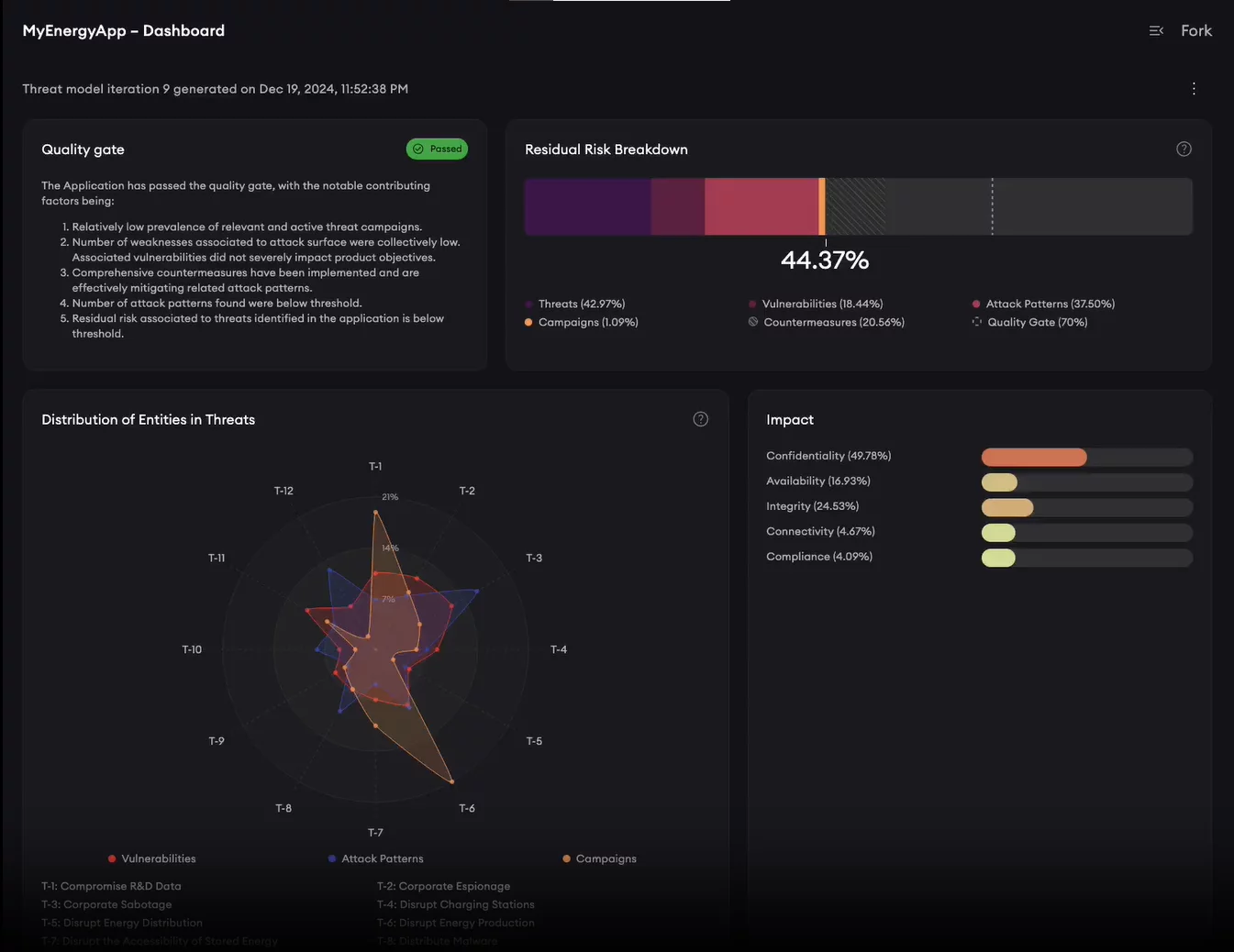
Proprietary Residual Risk Formula
Ensure relevant threats are quantified accurately and mitigated effectively.
-
Quality Gates
Enforce rigorous security standards at every stage of the threat modeling process, ensuring consistent, high-quality assessments.
-
Business Impact Analysis
Gain insight into how fundamental security pillars are affected and understand the potential financial implications of data breaches and downtime to your organization.
A Single Pane of Glass for Security Insights
Unveil a new perspective on your application’s security posture with our unified view. Transform intricate threat data into actionable insights, by merging relevant industry threats with your application’s attack surface, and cyber threat intelligence.
-
Integrated Industry Taxonomies
Our platform automatically correlates threat data with trusted frameworks and standards from MITRE and OWASP including CWE, CVE with EPSS, CAPEC, ATT&CK, D3FEND and ASVS to drive targeted mitigations and actionable insights.
-
On-Demand Security Testing
Substantiate the viability of potential threats by requesting targeted testing of specific weaknesses, vulnerabilities, and attack patterns directly from your threat models.
-
Collaborative Workflows
Empower your security and product teams with integrated workflows that allow you to dismiss items, create custom entries and relationships, all in real-time.
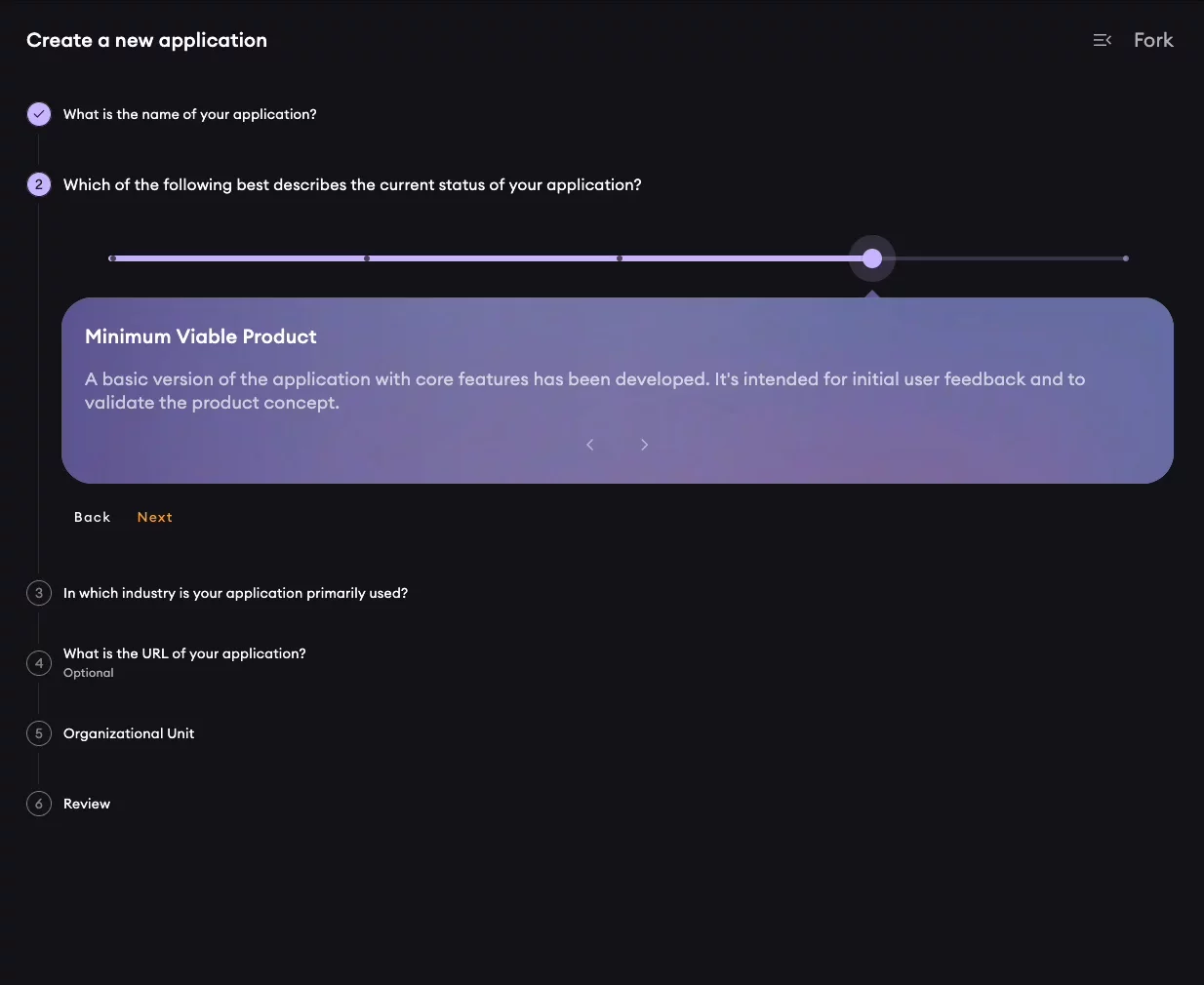
Threat Modeling from Sprint 1
Harnesses the proven benefits of threat modeling, enabling your teams to identify and integrate security-driven design principles directly into your software from day one.
-
Relevant in Every Stage
Adapt your threat models to your application’s current lifecycle stage – from planning and design to maintenance, ensuring every assessment is contextually applicable and practical.
-
Build Once, Evolve Continuously
Develop your threat model at the outset and update it as your application progresses, keeping your security approach focused on the evolving risk landscape.
-
Threat Modeling for Every Role
Built on threat modeling principles that streamline workflows for diverse stakeholders, from product teams and security experts to business operations.
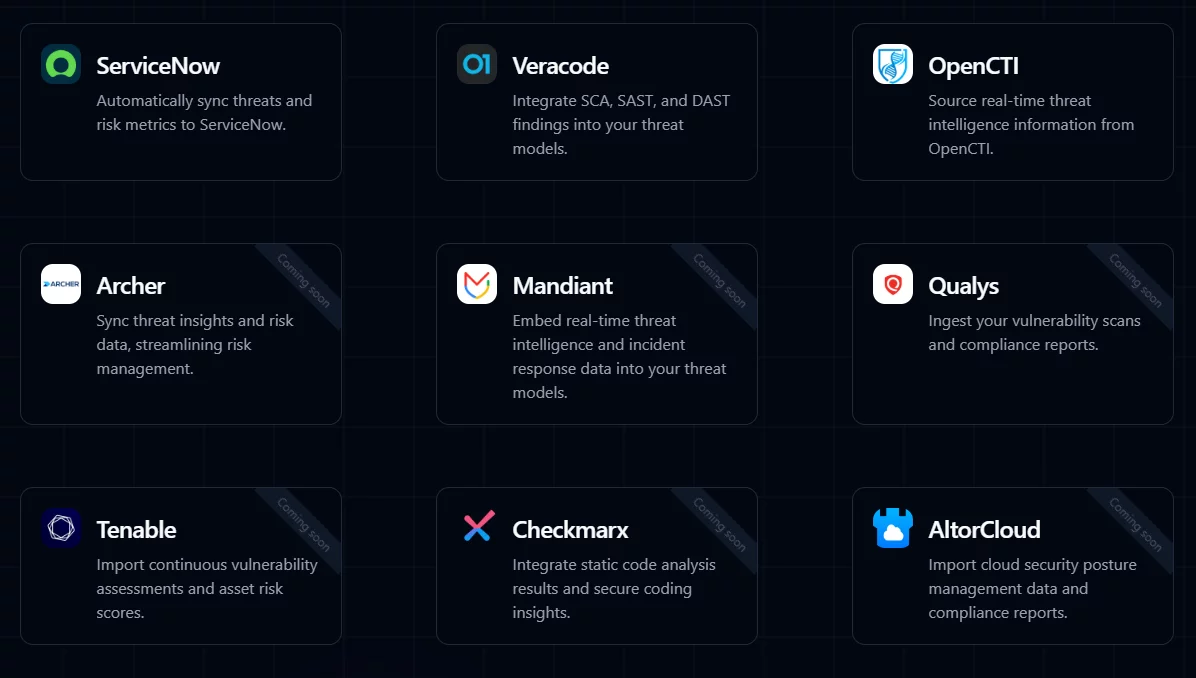
Integrations
Supercharge your threat modeling process by integrating Fork with your existing AppSec tooling.
Leverage the PASTA Methodology
Brought to you by a co-author of the Process for Attack Simulation and Threat Analysis (PASTA) methodology, our platform is a practical implementation of the renowned risk-centric, business-aligned threat modeling framework that raises the bar far beyond traditional approaches.


-
Risk-Centric Focus
Prioritizes threats based on business impact rather than just technical vulnerabilities.
-
Real-World Simulation
Emulates realistic attack scenarios to uncover potential weaknesses.
-
Comprehensive Analysis
Merges technical and business perspectives for a well-rounded threat assessment.
-
Iterative Process
Allows continuous refinement and adaptation as threats evolve
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Simple Pricing, Powerful Security
Get started for free with threat modeling for a single application, or scale up with our Enterprise subscription designed to secure your entire organization.
Fork Community
Essential threat modeling functionalities designed to help you secure your application for free.
- One application threat model
- Single user in the team
- Vulnerability ingestion via SBOM or OVAL
Sign-up FREE
Fork Enterprise
Unlock enterprise-grade threat modeling capabilities for scale.
- Unlimited applications and threat models
- Unlimited team members and organizational units
- Access to all integrations
- Granular access controls and permissions
- SSO with SAML or OIDC
- Audit logs and edit history
Contact Sales
Fork Enterprise PT
Extend your SaaS subscription with our managed service option.
- Everything from Fork Enterprise
- Request on-demand security testing directly from your application threat models
- In-depth exploitability analysis
- Real-time status updates
Contact Sales
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
As modern software development evolves at a rapid pace, so must our approach to threat modeling. Continuous threat modeling is crucial for maintaining an up-to-date understanding of your application’s security posture, especially within dynamic and agile environments. Fork, our SaaS threat modeling platform built on the PASTA (Process for Attack Simulation and Threat Analysis) framework, provides an innovative solution that enables continuous threat modeling to be seamlessly integrated into your software development lifecycle.
Integrating Threat Intelligence for a Live, Evolving Threat Model
A key feature of Fork is its ability to integrate with different providers, allowing it to ingest data from various sources such as Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), Software Composition Analysis (SCA), and manual penetration test findings. This ensures that your threat model is not a static, one-time exercise but an evolving, live model that adapts to the changing threat landscape.
These integrations allow Fork to continuously pull in the latest threat intelligence and vulnerability data, ensuring your threat model is always up-to-date. Additionally, Fork can push this data to issue-tracking platforms, enabling your development teams to address security issues in real-time and keep track of ongoing security efforts. This live threat model provides your organization with an accurate and current view of potential risks, enhancing your ability to respond to emerging threats.
Automating the Mapping to Industry Standard Taxonomies
With Fork, you can regularly sync all your integrated sources and automatically map them to existing industry-standard taxonomies directly within your threat library. This feature ensures that your threat data is organized and structured in a way that is both comprehensive and understandable. By adhering to recognized taxonomies, Fork allows your security and development teams to communicate more effectively and align with industry best practices.
When changes occur in your threat model, whether through new findings or shifts in the risk landscape, Fork will send out in-app and email notifications. These alerts inform you whenever the status of residual risk moves above or below your predefined quality gates. This ensures that you are always aware of your application’s current security posture and can respond quickly to any changes.
Tracking Historical Data for Continuous Improvement
One of Fork’s standout features is its ability to store historical data and present it in an easy-to-understand chart format. This allows you to track how your application’s security posture has changed over time, providing invaluable insights into the most significant contributing factors to your risk profile. By analyzing these trends, your team can identify areas for improvement and make informed decisions about where to focus security efforts. This ongoing visibility helps ensure that your threat modeling efforts are not just a one-time activity but an integral part of your application’s lifecycle.
Supporting Both Application and Component-Based Threat Modeling
Fork is designed to support threat modeling for entire applications, enabling you to consider the existing attack surface and associated vulnerability data. In addition, it is equipped to handle component-based threat modeling, which allows Agile and Scrum teams to perform recurring threat modeling sessions for individual components or features as they are being planned. This capability helps teams identify and address potential threats earlier in the development cycle, fostering a proactive security mindset.
By incorporating threat modeling at the component level, teams can ensure that security is considered from the outset, reducing the risk of costly architectural changes and technical debt later in the development process. This approach saves developer hours and allows software engineers to focus on building features rather than constantly reacting to security issues.
Fork enables continuous threat modeling by integrating with threat intelligence sources, automating the mapping to industry-standard taxonomies, providing real-time notifications, and tracking historical data to offer an up-to-date and evolving view of your security posture. With its support for both application and component-based threat modeling, Fork further enhances your organization’s ability to be agile, adaptable, and always prepared to address the latest threats, ensuring that security remains an integral and ongoing part of your software development process.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Resources
We’re Not a Vendor
We’re Your Security Partner
- Risk-centric security
- True extension of your team
- Executive-level experience