VerSprite’s PASTA Threat Modeling Service
PASTA Threat Modeling to Simulate Attacks and Prioritize Business Risk
DOWNLOAD
PASTA Threat Modeling
eBook Risk-Based Threat Modeling
The Process for Attack Simulation and Threat Analysis (PASTA) provides businesses a strategic process for mitigating cybercrime risks by looking first and foremost at cyber threat mitigation as a business problem. The process provides the tactical steps that can be followed to provide effective countermeasures for mitigating existing vulnerabilities by analyzing the attacks that can exploit these vulnerabilities and mapping these attacks to threat scenarios that specifically focus on the application as a business-asset target.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Why the PASTA Threat Modeling Framework Has Been Adopted Worldwide
The Process for Attack Simulation and Threat Analysis (PASTA) provides businesses a strategic process for mitigating cybercrime risks by looking first and foremost at cyber threat mitigation as a business problem. The purpose of PASTA is to provide an in-depth process for simulating attacks to your applications. By analyzing cyber threats that originate from the simulated attacks, organizations can address posed threats and mitigate potential cyber risk.
The process provides the tactical steps that can be followed to provide effective countermeasures for mitigating existing vulnerabilities by analyzing the attacks that can exploit these vulnerabilities and mapping these attacks to threat scenarios that specifically focus on the application as a business-asset target.
The foundation of VerSprite’s penetration testing methodology is based on emulating realistic attacks by a malicious actor through the use of Process for Attack Simulation and Threat Analysis (PASTA).
PASTA consists of a seven-stage process for simulating attacks and analyzing threats to the organization and application in scope with the objective of minimizing risk and associated impact to the business. This risk-based threat modeling approach goes beyond traditional threat modeling by enabling a company to make security decisions driven by business objectives.
This posture to both application and network security that VerSprite takes by assessing the operational impact and the threats to the business before evaluating the security of the applications, services, and infrastructure in scope helps not only to understand the vulnerabilities, but remediate them in a business rationalized manner.
Thus, each penetration test exercise begins by modeling the threat to understand attacker motivation and possible targets. Then we identify likely attacks that can cross technologies, people, and processes, and assess the strength of the countermeasures to resist attacks. This allows for decisions on mitigation of vulnerabilities to be made based on the operational risk to the business.
As a result of this very first phase for every engagement, VerSprite will have acquired at least the following information to then walk through the corresponding methodology, selected based on the type of engagement:
-
Business objectives for the application/service/infrastructure in scope
-
Business use cases that are the most critical/sensitive
-
Abuse cases that are the most critical/sensitive for the business
-
Possible Threat Actors targeting the application/service/infrastructure in scope
-
Principal Threat Motives
-
Type of targeted information and assets in scope
This approach allows VerSprite to understand security from both a business and attacker perspective in order to model and simulate realistic attacks during the engagement, pressure test the security posture being targeted, and provide key insights and recommendations that align security with business.
VerSprite’s methodology during client engagements is commensurate to the type of security effort that is provided and the objectives for the exercise. As seasoned security professionals, the team recognizes the effectiveness of industry frameworks and standards that exist across an array of security disciplines but at the same time understands that there are no one-size-fits all solutions.
As a result, VerSprite successfully employs the use of both in-house developed, as well as renowned and well-regarded methodologies as part of the consulting engagements in order to align the client deliverables and security services to an industry acceptable level of security management.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Industries We Serve
VerSprite delivers PASTA Threat Modeling across industries where security failures translate directly to financial loss, safety risk, or regulatory exposure.
Financial Services & FinTech
-
Apply the PASTA methodology to model threats across banking applications, payment platforms, and financial APIs
-
Identify threat actors, fraud scenarios, and abuse cases impacting transactions and digital assets
-
Analyze attack surfaces, trust boundaries, and third-party integrations across financial ecosystems
-
Deliver risk-prioritized mitigation strategies aligned to regulatory requirements and business impact
Healthcare & Life Sciences
-
Use PASTA to model threats to applications handling ePHI, clinical workflows, and research systems
-
Identify ransomware, insider threat, and supply chain abuse scenarios impacting patient care
-
Analyze trust boundaries across EHR systems, connected medical devices, and external partners
-
Provide risk-driven security requirements aligned to HIPAA and operational resilience goals
SaaS & Technology Providers
-
Decompose cloud-native architectures and microservices using PASTA’s structured, risk-based approach
-
Model threats targeting authentication flows, APIs, tenant isolation, and CI/CD pipelines
-
Identify systemic risks introduced through third-party services and open-source dependencies
-
Deliver prioritized security controls to strengthen product security and customer trust
Retail & E-Commerce
-
Apply PASTA to model threats targeting checkout processes, payment systems, and customer account management
-
Identify fraud, credential abuse, and supply chain compromise scenarios
-
Analyze integrations with payment processors, logistics providers, and marketing platforms
-
Provide risk-ranked mitigation strategies to protect revenue, availability, and brand reputation
Manufacturing & Critical Infrastructure
-
Use PASTA to model threats across IT/OT convergence and production-supporting applications
-
Identify attack paths that could disrupt operational processes or impact safety
-
Analyze trust relationships across vendors, contractors, and remote access channels
-
Deliver risk-prioritized security improvements to enhance operational resilience
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
PASTA Threat Modeling for Cybersecurity: OWASP All Chapters 2020 Presentation
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
PASTA Threat Modeling 7 Steps
(Process for Attack Simulation & Threat Analysis):
1. Define Business Context of Application
This considers the inherent application risk profile and address other business impact considerations early in the SDLC or for given Sprint under Scrum activities.
2. Technology Enumeration
You can’t protect what you don’t know is the philosophy behind this stage. It’s intended to decompose the technology stack that supports the application components that realize the business objectives identified from Stage 1.
3. Application Decomposition
Focuses on understanding the data flows amongst application components and services in the application threat model.
4. Threat Analysis
Reviews threat assertions from data within the environment as well as industry threat intelligence that is relevant to service, data, and deployment model.
5. Weakness / Vulnerability Identification
Identifies the vulnerabilities and weaknesses within the application design and code and correlates to see if it supports the threat assertions from the prior stage.
6. Attack Simulation
This stage focuses on emulating attacks that could exploit identified weaknesses/vulnerabilities from the prior stage. It helps to also determine the threat viability via attack patterns.
7. Residual Risk Analysis
This stage centers around remediating vulnerabilities or weaknesses in code or design that can facilitate threats and underlying attack patterns. It may warrant some risk acceptance by broader application owners or development manager
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Process for Attack Simulation & Threat Analysis Risk-Centric Threat Modeling Methodology
VerSprite leverages our PASTA (Process for Attack Simulation & Threat Analysis) methodology to apply a risk-based approach to threat modeling. This methodology integrates business impact, inherent application risk, trust boundaries amongst application components, correlated threats, and attack patterns that exploit identified weaknesses from the threat modeling exercises. Prior to PASTA, most application threat models were not even considering actual threats.
As the name implies, a key goal for threat modeling is to do just that – model threats. Threat categorization mnemonics (like STRIDE) are helpful for beginners, but product managers and their superiors are eager to know which threats are topical to their business, product, and platform. Furthermore, limiting threats to a handful of categories may not include the actual threats adversarial groups are planning.
PASTA provides a risk-centric threat modeling approach that is evidence-based. VerSprite’s security experts correlate real threats to your attack surface of application components and identify risk by first understanding the context of what the software or application is intended to do for the business or its clients. We also conduct exploitation tests that support threat motives within the model to validate whether they are probabilistic. Correlating viability with sustained impact allows this methodology to resonate as a highly effective risk-focused threat modeling approach.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Applying PASTA Threat Modeling to Penetration Testing
The use of VerSprite’s PASTA Threat Modeling methodology will guide the ensuing penetration test exercise, which can be performed in different ways depending on the approach to take and how much information is to be shared during the testing. The best way to see this is as follows:
Blackbox Application Penetration Testing
Takes a DAST (Dynamic Application Security Testing) approach and assumes no prior information is provided about the target. With this type of approach, VerSprite attempts to simulate an attack by a threat that would have little to no insight into the environment or application architecture.
Whitebox Application Penetration Testing
This takes a SAST (Static Application Security Testing) approach where the source code of the application is provided for its review. Depending on the size of the application, this can be time consuming, but if performed along with an application threat model, this could be the way to go if you are looking to find as many issues as possible and understand if secure development best practices are being followed. If a test environment is available during the exercise, every finding can be validated dynamically to provide a better Proof of Concept that shows the real impact of exploiting the vulnerability
Greybox Application Penetration Testing
This takes a DAST approach, and credentials are provided to perform authenticated testing. Additional documentation can be shared around the environment and architecture of the application to help in understanding its inner working and how the different components work together. If the source code of the application is also provided in order to support the testing, the Application Pentest takes a mixed approach between dynamic and static analysis instead. This Greybox approach allows for combining the convenience of DAST with the depth of analysis provided by SAST, which not only saves time during dynamic testing but also enables the possibility of going deeper in the review of critical functions to the business.
Modeling your application for threats helps to preemptively address security within your software development lifecycle. There’s more to threat modeling than mapping a handful of threat categories to your application and building a data flow diagram. Learn how we can tailor the PASTA approach to fit your development timelines and maximize the output of application threat models.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Key Characteristics of Risk-Centric PASTA Threat Modeling
1. It is a Methodology
If you’re looking for a process to follow, PASTA is designed for that. With seven phases with underlying activities in each phase, this approach is intended to guide new and experienced threat modelers across risk-centric application threat modeling activities.
2. Risk-Focused
PASTA not only looks at the variables of threat, vulnerability, countermeasures, and impact. Most importantly, it considers the probability of each variable and other supporting qualities like threat motives, current threat evidence, and countermeasure effectiveness.
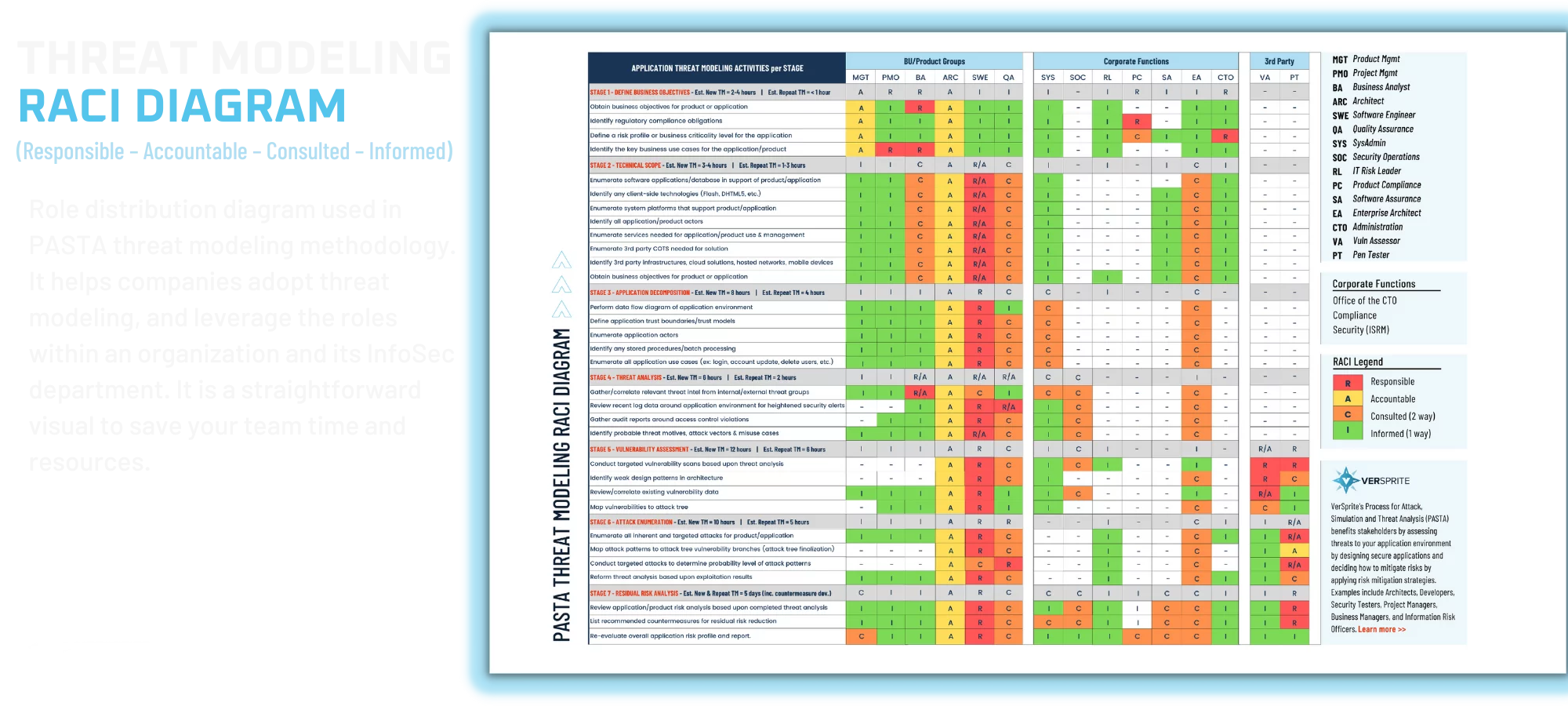
3. Collaborative
Most threat modeling exercises simply include an audience of developers. This is a limited approach since developers depend on design, underlying infrastructure, managed corporate services (e.g. SSO, IAM, PKI, etc.), and the configuration of open frameworks. For this reason, architects, DevOps team members, systems engineers, business analysts, and SOC team members are also good candidates for collaborative threat modeling discussions under PASTA.
4. Prescriptive
In the end, PASTA is focused on providing prescriptive guidance on the exploitable vulnerabilities that are of greater priority. The last phase, residual risk analysis, focuses on addressing security countermeasures to non-accepted application risks and providing remediation alternatives, all depending on the team’s risk impact considerations, threat likelihood, and cost of countermeasure implementation.
5. Evidence-based
Concrete evidence around quantitative business impact values, threat information driven threat assertions, and attack trees with probability values on each branch help to denote threat likelihood.
6. Maturity Modeling Integration
Whether you have never done threat modeling before or are a team of security champions, the activities defined within each phase of PASTA can correlate to both BSIMM and OpenSAMM maturity models for secure software development programs. Inquire more on how you can track maturity over time with PASTA and these maturity models.
7. Preemptive Compliance
PASTA considers technical requirements for applications as part of its first stage since non-compliance can affect product assurance towards varying regulatory requirements.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Contact VerSprite
Regardless of the type of engagement, VerSprite takes a complete manual approach for testing; automated testing is only an option for breadth of coverage or when necessary to complement certain tests. This guarantees a more in depth understanding of the target which ends up providing better quality results in terms of findings plus no false positives and real POCs for each of the issues found.
Let Us Build a Tailored Engagement for You
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
PASTA Threat Modeling FAQs
What is PASTA threat modeling?
PASTA (Process for Attack Simulation and Threat Analysis) is a risk-centric threat modeling methodology designed to identify, analyze, and mitigate application and organizational threats. It focuses on simulating real-world attacks and aligning security risks with business impact.
What are the 7 stages of the PASTA methodology?
The PASTA methodology consists of seven stages:
- Define business objectives
- Define the technical scope
- Decompose the application
- Analyze threats
- Identify vulnerabilities
- Simulate attacks
- Analyze risk and impact
How is PASTA different from other threat modeling frameworks?
Unlike frameworks such as STRIDE, which focus on categorizing threats, PASTA is risk-driven and attacker-centric. It emphasizes real-world attack simulation and prioritizes threats based on business impact, making it more actionable for enterprise security programs.
Why should organizations use PASTA threat modeling?
PASTA helps organizations align security efforts with business objectives by identifying the most critical risks. It improves decision-making, enhances risk visibility, and supports proactive security strategies across the development lifecycle.
What is included in a PASTA threat modeling engagement?
A PASTA engagement typically includes:
- Business and technical scope definition
- Application architecture and data flow analysis
- Threat and vulnerability identification
- Attack simulation scenarios
- Risk prioritization and remediation planning
How does PASTA support DevSecOps?
PASTA integrates into DevSecOps by providing a structured framework for identifying and prioritizing risks early in the development lifecycle. This enables continuous security validation and informed decision-making within CI/CD pipelines.
What types of threats can PASTA identify?
PASTA can identify:
- Business logic vulnerabilities
- Authentication and authorization weaknesses
- API and integration risks
- Advanced attack paths and chained exploits
- Insider and external threat scenarios
Is PASTA suitable for enterprise environments?
Yes. PASTA is designed for complex enterprise environments where understanding business impact and attack paths is critical. It scales across applications, infrastructure, and organizational risk models.
Who should be involved in a PASTA threat modeling exercise?
PASTA requires collaboration between security teams, developers, architects, product owners, and business stakeholders to ensure risks are evaluated from both technical and business perspectives.
What makes VerSprite’s PASTA threat modeling approach different?
VerSprite enhances the PASTA methodology with a research-driven, attacker-focused approach that incorporates real-world threat intelligence, proprietary techniques, and business-contextual risk analysis to deliver actionable security insights.
What is the difference between PASTA and STRIDE?
PASTA and STRIDE are both threat modeling frameworks, but they serve different purposes. STRIDE focuses on categorizing threats (such as spoofing, tampering, and denial of service), while PASTA is a risk-centric methodology that simulates real-world attacks and prioritizes threats based on business impact. PASTA is more suitable for organizations that need deeper, attacker-driven risk analysis.
When should organizations use PASTA threat modeling?
Organizations should use PASTA threat modeling during application design, major architecture changes, digital transformation initiatives, or when handling sensitive data. It is especially valuable for enterprises that need to align security decisions with business risk and regulatory requirements.
Who created the PASTA threat modeling methodology?
The PASTA threat modeling methodology was developed by Tony UcedaVelez and Marco Morana. It was designed to provide a structured, risk-based approach to analyzing application and organizational threats through attacker simulation.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Resources
We’re Not a Vendor
We’re Your Security Partner
- Risk-centric security
- True extension of your team
- Executive-level experience