Threat Modeling as a Service (TMaaS)
Cyber Threat Modeling as a Service for Scalable, Risk-Based Security and Attack Simulation
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
What Is Threat Modeling?
Threat modeling is a systematic approach to identifying potential security threats, vulnerabilities, and attack vectors in a system’s architecture. This process involves analyzing the system from an adversary’s perspective to anticipate potential security issues before they materialize in production environments.
Effective threat modeling addresses four fundamental questions:
- What are we building? (System architecture and boundaries)
- What can go wrong? (Threat identification)
- What are we doing about it? (Mitigation strategies)
- Have we addressed the issues adequately? (Validation)
What Is Threat Modeling as a Service?
Threat Modeling as a Service (TMaaS) represents the evolution of traditional threat modeling into a scalable, on-demand service model. Rather than organizations maintaining dedicated threat modeling capabilities internally, TMaaS providers deliver specialized expertise, methodologies, and tooling through a structured service offering.
Core Components of TMaaS
1. Specialized Security Professionals
TMaaS providers maintain teams of security professionals with:
- Deep understanding of attack methodologies
- Experience across diverse technology stacks
- Knowledge of industry-specific threat landscapes
- Familiarity with regulatory compliance requirements
- Proficiency in multiple threat modeling methodologies (PASTA)
2. Scalable Processes
TMaaS implementations typically involve:
- PASTA Framework
- Consistent documentation templates
- Repeatable threat identification workflows
- Integration with development lifecycles
- Mechanisms for knowledge transfer
3. Purpose-Built Technology
Most TMaaS offerings leverage:
- Automated threat modeling platforms
- Threat intelligence integration
- Vulnerability databases
- Visualization tools
- Documentation generators
- Collaboration platforms
Benefits of TMaaS
Operational Advantages
- Scalability: Ability to handle fluctuating demand without permanent staffing
- Consistency: Standardized approaches to threat assessment across projects
- Efficiency: Reduced time-to-delivery compared to building in-house capability
- Focus: Development teams can concentrate on core business functionality
Security Improvements
- Specialized Perspective: External security experts bring diverse experience
- Reduced Bias: Third-party assessment minimizes institutional blind spots
- Current Threat Intelligence: Exposure to broader attack trends and methodologies
- Comprehensive Coverage: Systematic approach reduces gaps in security analysis
Business Value
- Cost-Effectiveness: Lower TCO compared to maintaining dedicated expertise
- Risk Reduction: Proactive identification of security issues before deployment
- Accelerated Time-to-Market: Security assurance without development delays
- Compliance Support: Documentation and evidence generation for regulatory requirements
When to Consider TMaaS
Organizations should evaluate TMaaS when:
- Security expertise is limited or stretched thin
- Development velocity outpaces security assessment capability
- Projects have varying or specialized security requirements
- Regulatory compliance mandates formal threat analysis
- Security maturity is developing but not yet comprehensive
Implementation Approaches
Integration Models
- Point-in-Time Assessment: One-off threat modeling for specific projects
- Continuous Service: Ongoing partnership with regular assessment cycles
- Hybrid Capability: External expertise supporting internal security teams
- Knowledge Transfer: Service that builds organizational capability over time
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
PASTA as a cyber threat modeling framework is adopted and used by worldwide organizations.
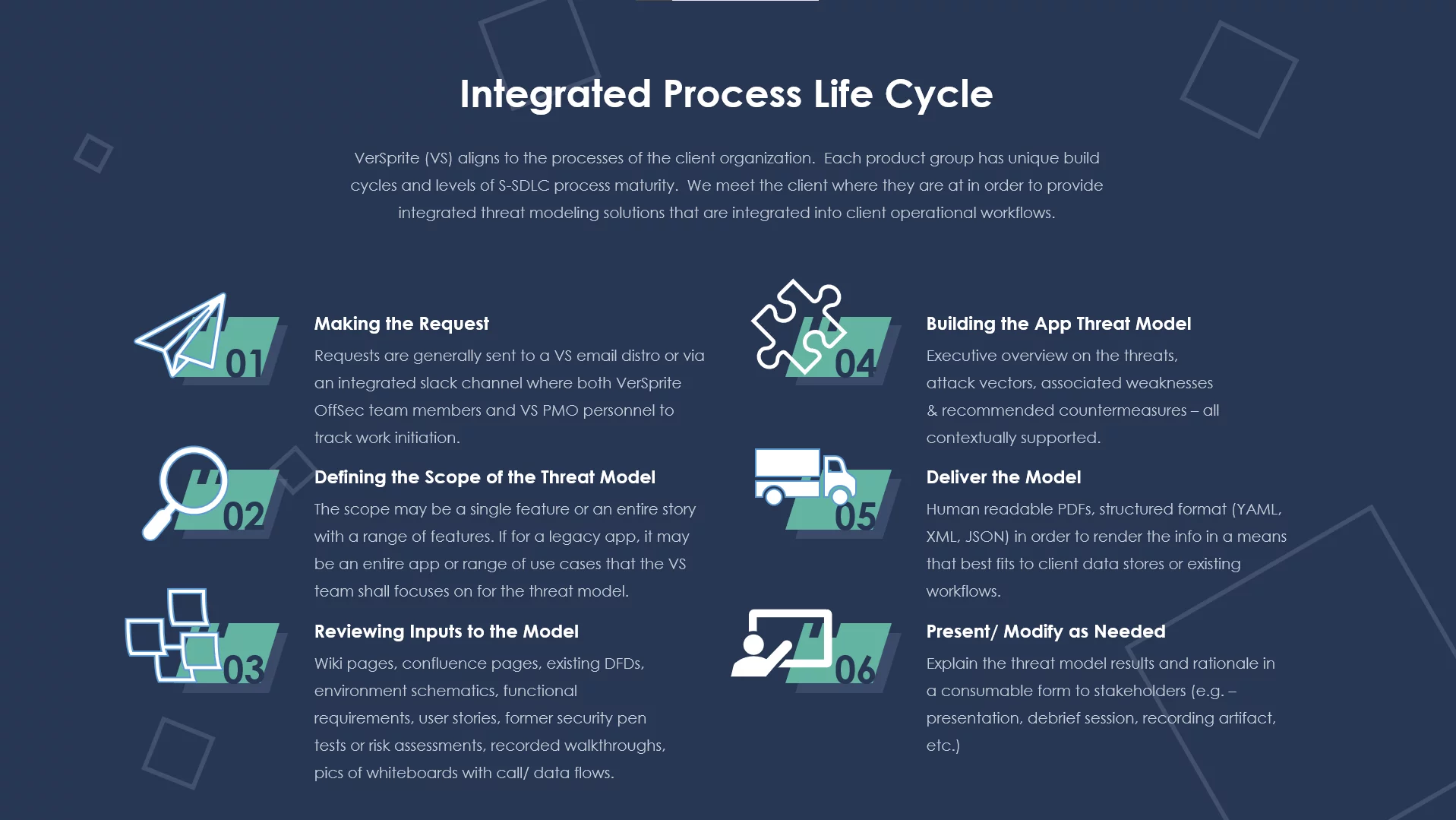
At VerSprite, we specialize in providing Threat Modeling as a Service (TMaaS), equipping businesses with comprehensive solutions to pinpoint and counteract potential security threats. Our proficiency in cybersecurity underscores the need for a proactive stance in protecting your organization’s critical assets.
Apply a Risk-Based Approach to Threat Modeling
Modeling your application for threats helps to preemptively address security within your software development lifecycle. There’s more to threat modeling than mapping a handful of threat categories to your application and building a data flow diagram. Learn how we can tailor the PASTA approach to fit your development timelines and maximize the output of each application threat model →
Our PASTA Threat Modeling for Every Stage approach enables you to identify possible vulnerabilities at each phase of your software development lifecycle. Our team collaborates with you to devise a custom threat model that aligns with your business goals.
VerSprite leverages our PASTA (Process for Attack Simulation and Threat Analysis) methodology to apply a risk-based approach to threat modeling. This methodology integrates business impact, inherent application risk, trust boundaries amongst application components, correlated threats, and attack patterns that exploit identified weaknesses from the threat modeling exercises. Prior to the PASTA threat model, most application threat models were not even considering actual threats.
As the name implies, a key goal for threat modeling is to do just that – model threats. Threat categorization mnemonics (like STRIDE) are helpful for beginners, but product managers and their superiors are eager to know which threats are topical to their business, product, and platform. Furthermore, limiting threats to a handful of categories may not include the actual threats adversarial groups are planning.
PASTA provides a risk centric threat modeling approach that is evidence-based. VerSprite’s security experts correlate real threats to your attack surface of application components and identify risk by first understanding the context of what the software or application is intended to do for the business or its clients. We also conduct exploitation tests that support threat motives within the model to validate whether they are probabilistic. Correlating viability with sustained impact allows this methodology to resonate as a highly effective risk-focused threat modeling approach.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Threat modeling is a crucial process in guaranteeing the security of software applications.
By implementing threat modeling as a service, businesses can reap many benefits that enhance the overall security of their systems.
Early Detection of Issues in the SDLC:
Cyber threat modeling as a service empowers organizations to find potential security issues early in the Software Development Life Cycle (SDLC). Incorporating threat modeling into the development process enables vulnerabilities to be detected and addressed before they escalate into costly and time-consuming problems.
Uncovering Design Flaws:
Through cyber threat modeling, businesses can discover design flaws that may leave their applications vulnerable to security breaches. By analyzing the system’s architecture and pinpointing potential weaknesses, organizations can make informed decisions to enhance the overall security posture of their software.
Evaluating New Forms of Attack:
As cyber threats evolve, it’s vital for businesses to stay ahead. Threat modeling as a service allows organizations to assess and evaluate new attack forms that may target their systems. By understanding potential attack vectors, businesses can proactively implement measures to protect their applications and data.
The PASTA Threat Model eBook Risk-Based Threat Modeling
The Process for Attack Simulation and Threat Analysis (PASTA) provides businesses a strategic process for mitigating cybercrime risks by looking first and foremost at cyber threat mitigation as a business problem. The process provides the tactical steps that can be followed to provide effective countermeasures for mitigating existing vulnerabilities by analyzing the attacks that can exploit these vulnerabilities and mapping these attacks to threat scenarios that specifically focus on the application as a business-asset target.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
At VerSprite, we provide comprehensive threat modeling as a service that is customized to the unique needs of your organization. Our team of seasoned security professionals collaborates with you to ensure your software applications are robust and secure. By capitalizing on our ability, you can mitigate risks, safeguard sensitive data, and maintain the trust of your customers.
Optimizing Testing Budget with Cyber Threat Modeling
When it comes to securing your organization’s software applications, one of the most effective strategies is threat modeling. By strategically finding and mitigating potential threats early in the development process, you can conserve valuable time, resources, and funds. At VerSprite,
we provide comprehensive Cyber Threat Modeling as a service. that can help your organization optimize its testing budget.
Targeted testing and code review form integral parts of our TMaaS offering. Our skilled team of security experts conducts a thorough analysis of your software applications to show vulnerabilities and weaknesses. By concentrating on specific areas of concern, we ensure your testing efforts are efficient and effective, saving you both time and money.
Along with targeted testing, our TMaaS solution also aids in finding gaps in the requirements process. By partnering with your development team, we review your project’s requirements to ensure they are comprehensive and adequately address potential security risks. This proactive approach can help you avoid expensive rework and delays in the future.
Another significant advantage of our TMaaS solution is the cost savings through early remediation. By identifying and addressing security issues early in the development lifecycle, you can avoid the higher costs associated with fixing vulnerabilities in later stages. Our team provides actionable recommendations and guidance to help you promptly remediate any identified threats.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
PASTA Threat Model Methodology
The 7 Stages of PASTA
(Process for Attack Simulation and Threat Analysis)
1. Define Business Context of Application
This considers the inherent application risk profile and address other business impact considerations early in the SDLC or for given Sprint under Scrum activities.
2. Technology Enumeration
You can’t protect what you don’t know is the philosophy behind this stage. It’s intended to decompose the technology stack that supports the application components that realize the business objectives identified from Stage 1.
3. Application Decomposition
Focuses on understanding the data flows amongst application components and services in the application threat model.
4.Threat Analysis
Reviews threat assertions from data within the environment as well as industry threat intelligence that is relevant to service, data, and deployment model.
5. Weakness / Vulnerability Identification
Identifies the vulnerabilities and weaknesses within the application design and code and correlates to see if it supports the threat assertions from the prior stage.
6. Attack Simulation
This stage focuses on emulating attacks that could exploit identified weaknesses/vulnerabilities from the prior stage. It helps to also determine the threat viability via attack patterns.
7. Residual Risk Analysis
This stage centers around remediating vulnerabilities or weaknesses in code or design that can facilitate threats and underlying attack patterns. It may warrant some risk acceptance by broader application owners or development managers.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Cyber Threat Modeling for Every Stage
At VerSprite, we offer a comprehensive Threat Modeling as a Service solution designed to integrate seamlessly into any stage of the development process. Whether you’re in the early planning phase or nearing the end of your software development lifecycle, our solution is flexible enough to adapt to your changing needs.
One of the key benefits of our Threat Modeling as a Service is its capacity to ensure software security at all levels. Our team of seasoned security professionals employs industry best practices to identify potential threats, vulnerabilities, and risks throughout the software development lifecycle. By conducting thorough threat modeling exercises, we assist you in prioritizing your security efforts and making informed decisions to mitigate potential risks.
This is not a one-size-fits-all solution. We understand that each organization has unique requirements and constraints. That’s why our solution can be customized to align with your specific business goals and compliance requirements. Whether you’re developing web applications, mobile apps, or complex enterprise systems, our flexible approach allows us to tailor our services to your needs.


- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
Whether you’re in the preliminary stages of development or managing an existing system, our services are tailored to meet your specific needs.
Allow us to tailor a PASTA threat model for your application so you can effectively apply the risk-centric methodology within the regiment of their software security assurance process.
Contact VerSprite today to get started.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
We’re Not a Vendor
We’re Your Security Partner
- Risk-centric security
- True extension of your team
- Executive-level experience