Turn Data *Mis*Management into Data Security
Data Security Steps To Take Now To Ensure Data Management Oversight Doesn’t Make Your Organization An Easy Target for Cybercriminals
by Marian Reed, Vice President, GRC
Avoid one of the leading causes of security breaches with data security. Cybersecurity efforts, such as improving security frameworks and processes and safeguarding assets, ultimately aim to protect one crucial aspect: data. The way an organization manages its data can determine its success or failure in the face of cyber threats.

What is the Role of Data?
Data is the most valuable asset for most organizations. It is the backbone of all modern businesses and processes. Whether it is a single-person LLC, small business, or multinational enterprise, data is everywhere, and it is only expanding. Data refers to various information that an organization collects, stores, and uses to make decisions, improve operations, provide services to its clients, and gain a competitive advantage. What does it include? Anything from customer information, financial data, research, employee information, company documentation, security information, regulated data such as Protected Health Information (PHI), etc. Organizations are constantly at risk of being targeted by cybercriminals. The target is always data, whether the motive is financial gain or stealing sensitive information.
Knowing The Right Data to Use is Key: PASTA Threat Modeling
Organizations Face Data Security and Management Challenges
- Insufficient data security measures: Because security controls are frequently implemented to check the box against a set of security frameworks or regulations, it leaves organizations vulnerable to data breaches. Many companies need an understanding of the genuine threats, which is the key to developing and implementing the proper security controls.
- Compliance complacency: Ensuring compliance with the regulatory requirements of an industry helps govern sensitive data. However, it does not protect the entire network of an organization. Regulations typically focus on a specific set or type of data. They often amount to checklists that miss a critical component – what threats are we protecting against? Compliance must be regularly audited in combination with organizational threat modeling to be effective. Read more about it now.
- Security awareness programs: These must be updated and held regularly. Employees continue to be a company’s weakest link despite their attempts at education. These programs need to incorporate scenarios that are real to the employees.
- Insider threats: Disgruntled employees with malicious intent, third-party vendors with poor security protocols, or unaware employees with unrestricted access can all lead to a costly data breach.
- Lack of visibility: An often-overlooked problem, organizations’ lack of visibility into their entire network of data – its flow, usage, and storage – is one of the leading causes of breaches. Most companies manage multiple platforms, devices, IoTs, and software and operate in a hybrid environment of local and cloud services. It becomes challenging to comprehensively understand the current state of a network or system, where and how information is handled and stored, and the level of access.
Why is Data Security Important?
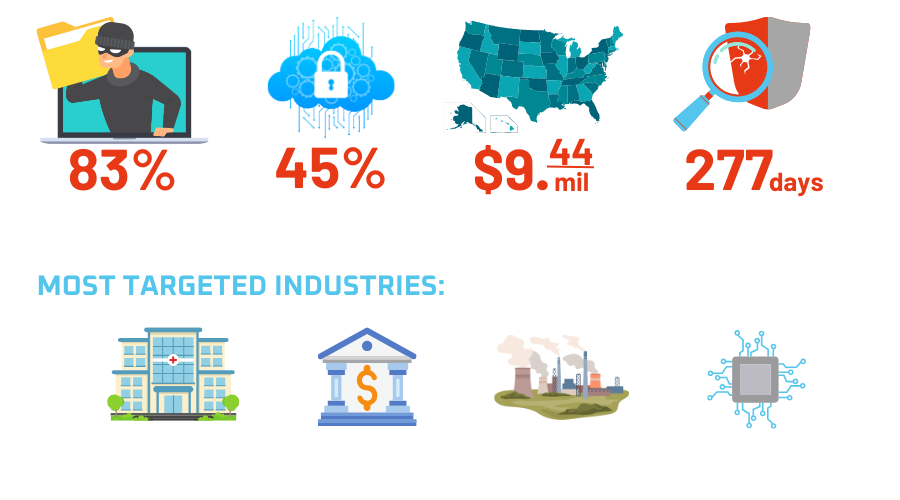
Safeguarding data throughout its entire lifecycle is crucial for all organizations. Protecting sensitive information from unauthorized access and breaches, which can cause financial losses, operational downtime, and damage to reputation, is a crucial driver for all security programs. As cyberattacks are becoming more prevalent and sophisticated, making data security a priority is more important than ever. Per the IBM report, in 2022 alone, the average cost of a data breach rose to $4.35 million globally. The increasing number and severity of data breaches highlight the importance of robust data security measures to prevent access, use, disclosure, disruption, modification, or destruction of sensitive information.
Is it possible to completely prevent data breaches? A quick answer is no. Cyberattacks are a matter of when not if. However, any organization can strengthen its cyber-resilience with an efficient data governance program. Developing security governance that protects your assets and works for your business continuity is crucial.
“A goal without a plan is just a wish.” Antoine de Saint-Exupery
An efficient data management plan should follow more than just industry regulations. It must include risk management, security policies, and a data security strategy.
In addition, policies are very fluid and are updated each year. So, it is essential to ensure that policies align with governance and a reputable framework. However, organizations must first build policies considering more contextual variables that pertain to the enterprise versus simply copying down what a group-produced framework says about a business it never knew. Another great reason to have your cybersecurity program in check, if you are in healthcare, is HIPAA Safe Harbor, enacted in 2021, which advises DHHS to consider an organization’s cybersecurity program when determining fines after a breach has occurred. Those with a better program may experience fewer penalties.
Data Security and Management Plan
Key points to keep in mind when developing a data management program for an organization:
- Scope: Clearly define and prioritize the data that needs to be protected, including code, customer information, PII, PHI, intellectual property, and contract data, based on risk and business impact.
- Discovery: Conduct a thorough data discovery to identify where the company’s data resides, its flow, and access points. You can use tools like those offered by SaaS data management providers to help.
- Remediation: Determine the scope and spread of data, and address any issues identified during the data discovery process by aligning them with the organization’s governance program, which outlines guidelines for data usage, storage, and archiving.
Data Management Programs Should Be Based On Clearly Defined Data Security And Business Objectives and Include The Following:
- Access controls include setting up user roles, access levels, and restrictions based on job functions and need-to-know.
- Data encryption practices: Upon determining which data needs to be encrypted based on its sensitivity, choose an encryption algorithm that fits the security requirements and is appropriate for the data type and volume. Make sure to encrypt data both in transit and when stored. Ensure segmented access to the data and regularly monitor and assess the encryption infrastructure.
- Disaster recovery planning: A disaster recovery plan is a process that outlines how an organization will respond to and recover from a potential attack and disruption to its critical data and systems. It incorporates risk assessments, impact analysis, recovery strategies, documentation, and training.
- Compliance: reviewing and adhering to relevant data protection regulations and industry standards (HIPAA, PCI DSS, GDPR).
- Regular auditing and monitoring: Performing systematic data audits aids in identifying potential security risks and deviations from the established policies and procedures.
- Security awareness training: A successful data security awareness program has the following components: clearly defined objectives and target audience; relevant and engaging training material tailored to the specific objectives and structure of the organization’s networks; encourages active participation and behavior change; regular evaluation of the program, and assessments of effectiveness employing red teaming exercises.
- Development of an organizational threat model: The organizational threat modelhelps to protect data throughout its lifecycle. Threat modeling allows the implementation of security controls and protocols, identifying the scope of data, segmentation, and role distribution, among other functions. Learn more about threat modeling and PASTA methodology.
Get Started with Data Security and Management from VerSprite
Developing a data management program or data governance is essential for any organization to protect sensitive information and comply with regulations. Organizations can effectively safeguard their data and minimize risks by clearly defining the scope of data to be protected, conducting a thorough data discovery process, and aligning any issues identified with the organization’s governance program. Implementing these strategies will ensure that your organization handles data securely. Your company will be able to operate with confidence, knowing that they are protecting its sensitive information.
Contact us today for more information on data protection and assistance with improving your organization’s security posture.
PASTA Threat Modeling: The Process for Attack Simulation and Threat Analysis
VerSprite leverages our PASTA (Process for Attack Simulation and Threat Analysis) methodology to apply a risk-based approach to threat modeling. This methodology integrates business impact, inherent application risk, trust boundaries among application components, correlated threats, and attack patterns that exploit identified weaknesses from the threat modeling exercises.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /