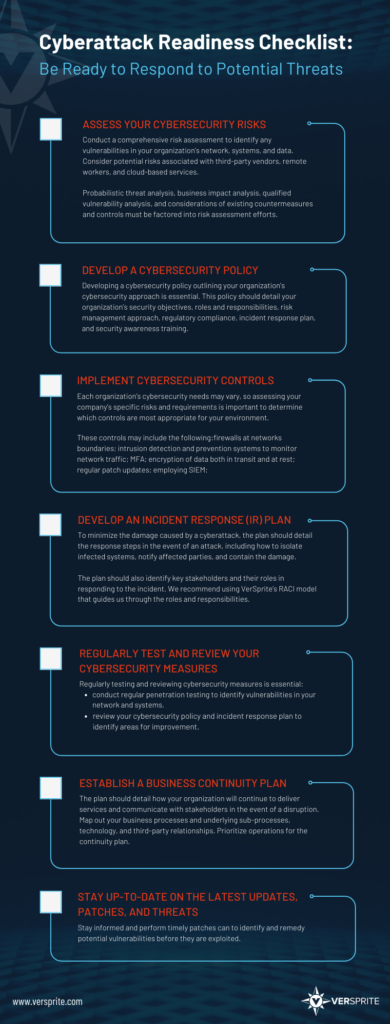
Cyberattack Readiness Checklist
Cyber and Risk Consulting – How To Prepare Your Business For Cyberattacks
Being prepared is winning half the battle with cybercriminals. By having in place this robust cyberattack readiness checklist, you will ensure your organization is ready to respond to potential threats:
- ASSESS YOUR CYBERSECURITY RISKS
The first step in creating a cyberattack readiness checklist is to assess your cybersecurity risks. Conduct a comprehensive risk assessment to identify any vulnerabilities in your organization’s network, systems, and data. This assessment should also consider potential risks associated with third-party vendors, remote workers, and cloud-based services.
Understanding risk hinges on identifying and qualifying the variables in the risk equation. For this reason, probabilistic threat analysis, business impact analysis, qualified vulnerability analysis, and considerations of existing countermeasures and controls must be factored into risk assessment efforts.
- DEVELOP A CYBERSECURITY POLICY
Once you’ve identified your cybersecurity risks, developing a cybersecurity policy outlining your organization’s cybersecurity approach is essential. This policy should detail your organization’s security objectives, roles and responsibilities, risk management approach, regulatory compliance, incident response plan, and security awareness training. Developing an organizational threat model, such as VerSprite’s PASTA methodology-based model, will help secure the organization’s assets while considering its business objectives.
- IMPLEMENT CYBERSECURITY CONTROLS
Implementing cybersecurity controls is crucial to mitigating the risk of cyberattacks. Remember, each organization’s cybersecurity needs may vary, so assessing your company’s specific risks and requirements is important to determine which controls are most appropriate for your environment.
These controls may include the following:
- Deploying firewalls at networks boundaries;
- Setting up Intrusion Detection and Prevention Systems to monitor network traffic;
- Multi-factor Authentication (MFA) is a must-implement layer of security for any business;
- Encryption of data both in transit and at rest to protect against unauthorized access;
- Regular patch updates for software, applications, operating systems, and firmware;
- Employing SIEM (Security Information and Event Management) tools to collect, analyze, and correlate security event logs;
- Implementing access control and privileged account management;
Procedures must be set to regularly update and patch all software and hardware to prevent vulnerabilities from being exploited.
- CONDUCT REGULAR SECURITY AWARENESS TRAINING
Security awareness training is critical to ensuring that all employees understand their roles and responsibilities regarding cybersecurity. Regular training can help employees recognize potential threats, understand how to respond to incidents and learn best practices for maintaining a secure environment.
- DEVELOP AN INCIDENT RESPONSE (IR) PLAN
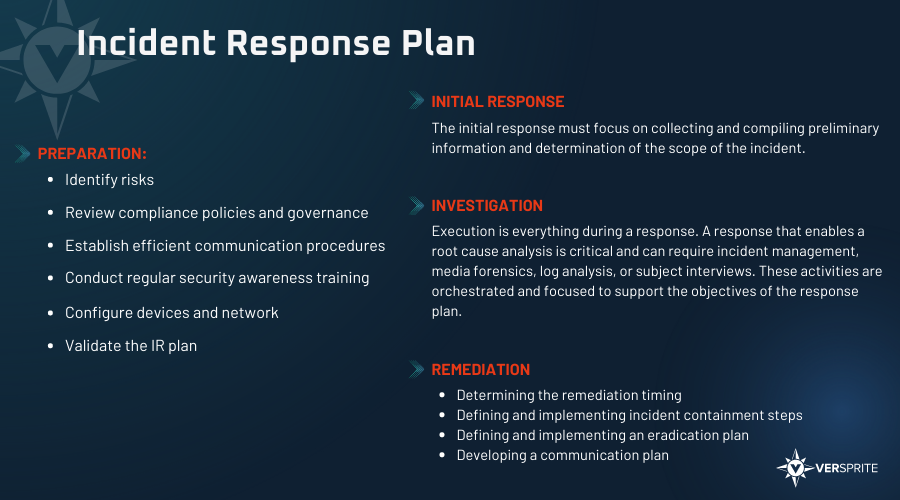
Developing an incident response plan is essential to minimize the damage caused by a cyberattack. This plan should detail the response steps in the event of an attack, including how to isolate infected systems, notify affected parties, and contain the damage.
The plan should also identify key stakeholders and their roles in responding to the incident. We recommend using the VerSprite’s RACI model that guides through the roles and responsibilities.
VerSprite recommends including the following stages in your organization’s IR plan:
*VerSprite can assist your organization with an actionable IR plan and guide you through the steps, contact us today.
- REGULARLY TEST AND REVIEW YOUR CYBERSECURITY MEASURES
Regularly testing and reviewing your cybersecurity measures is essential to ensure they are effective. Conducting regular penetration testing can help identify vulnerabilities in your network and systems, allowing you to take corrective action. Reviewing your cybersecurity policy and incident response plan can also help you identify areas for improvement and make necessary updates.
- ESTABLISH A BUSINESS CONTINUITY PLAN
In the event of a cyberattack, it’s essential to have a business continuity plan in place to ensure that your organization can continue to operate. This plan should detail how your organization will continue to deliver services and communicate with stakeholders in the event of a disruption.
An in-depth understanding of the business processes is essential to sustaining disruptions caused by a cyber-attack. Map out your business processes and underlying sub-processes, technology, and third-party relationships that help support your business’s more mission-critical areas. This will help prioritize operations for the continuity plan.
- STAY UP-TO-DATE ON THE LATEST UPDATES, PATCHES, AND THREATS
Maintaining a robust cybersecurity posture is essential to staying current on the latest threats and updates. Cyber threats constantly evolve, and staying informed and performing timely patches can help you identify and remedy potential vulnerabilities before they are exploited.
A cyberattack readiness checklist is essential for organizations looking to protect their digital assets from cybercriminals. By following these steps, organizations can identify potential vulnerabilities, implement cybersecurity controls, develop an incident response plan, and stay up-to-date on the latest threats.
Ensuring your company’s cyber-safety might seem like an onerous, complicated task. Our team is here to simplify and guide you through each step. Contact us today to see how we can help you.
Downloadable Resource:
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /