Network Security & Other Google Cloud Platform Concepts Defined
In previous blog posts, we discussed network security around Azure and AWS cloud solutions. Now it’s time to look at the third big contestant, Google Cloud Platform (GCP). To clarify things, we will define some Google Cloud Platform (GCP) concepts and cover identity and access management, network security, and data loss protection.
Google Cloud Platform (GCP) Resource Manager for Network Security
Some examples of Google Cloud Platform (GCP) resources are projects, Compute Engine instances, and Cloud Storage buckets.
Permissions
Permissions determine what operations are allowed on a resource. In the GCP IAM world, permissions are represented in the form of <service>.<resource>.<verb>, for example, pubsub.subscriptions.consume.
Roles
A role is a collection of permissions. You cannot assign a permission to the user directly; instead you grant them a role.
IAM Policy
You can grant roles to users by creating a GCP IAM policy, which is a collection of statements that define who has what type of access. A policy is attached to a resource and is used to enforce access control whenever that resource is accessed. For more info, see the policy overview.
GCP IAM Role Types in Network Security
There are three types of roles in GCP IAM:
- Primitive roles, which include the owner, editor, and viewer roles that existed before the introduction of GCP IAM. TIP: Don’t use primitive roles in GCP IAM policies, and never grant primitive roles to an organization, primitive roles give an identity a lot of power.
- Predefined roles, which provide granular access for a specific service and are managed by GCP. Read about predefined roles here.
- Custom roles, which provide granular access according to a user-specified list of permissions
Now that we’ve established some concepts, let’s look at the major components of GCP and their network security implications.
Identity Access Management
The first thing that we must think about for cloud security is Identity and Access Management (IAM), especially because GCP, Azure, and AWS implement IAM, but each of them in a different way. Here we are going to try to explain how Google implements IAM on their cloud.
Principle of Least Privilege
It is important to keep in mind that GCP IAM implements the security principle of least privilege. What does this mean? It means giving users only the necessary access to the resources they are using and nothing more. So, if a user needs to be able to access a VM, you give him the appropriate roles for that task (turn it on/off) but you don’t give them access to other tasks like taking a snapshot or editing the VM’s properties.
Members Definition
In GCP IAM, you grant access to members. Members can be of the following types:
- Google account: Any email address that is associated with a Google account can be an identity, including gmail.com or other domains.
- Service account: A service account is associated with an application instead of a user, so if you run code on GCP, you specify on which service account the code should run.
- Google group: A Google group is a named collection of Google accounts and service accounts. Every group has a unique email address that is associated with the group. It’s useful to apply policies to a collection of users.
- G Suite domain: A G Suite domain represents a virtual group of all the Google accounts that have been created in an organization’s G Suite account. Like Google groups, G Suite domains cannot be used to establish identity but enable convenient permission management.
- Cloud Identity domain: A Cloud Identity domain is like a G Suite domain because it represents a virtual group of all Google accounts in an organization. However, Cloud Identity domain users don’t have access to G Suite applications and features. For more information, see About Cloud Identity.
- allAuthenticatedUsers: A special identifier that groups all users that are authenticated on the GCP on your project
- allUsers: This represents anyone who is on the internet, including authenticated and unauthenticated users.
A Network Security Checklist for GCP IAM
- Don’t use default service accounts. They have primitive roles.
- Don’t let your service accounts have more than two active keys. Limiting the number of accounts using it applies the principle of least privilege
- Always use custom roles to monitor all external identities in your organization.
- Add external users to Cloud IAM policies as individual users and don’t add them to groups.
Network Security, a.k.a. Secure Networking
When it comes to network security, each cloud provider offers similar tools to help you protect your network, but some principles apply globally:
VPC for your network
GCP uses VPC (Virtual Private Cloud/Network) and subnets to allow you to organize your resources in the best way possible. You can group your resources to use the same subnet and also isolate them, so nobody else has access outside the resources on that group. This can limit the attack surface for someone who wants to target your company.
Also, you can find Shared VPC, which allows you to connect VPCs that you have isolated in a secured way, by using only internal IPs and not exposing anything to the Internet while maintaining your resource separation.
Firewall
Firewall rules apply to VPC, and these rules are the ones that provide network security for your resources. Some tips for firewall rules are:
- If a VM or database doesn’t need to communicate to the internet (because it’s only used by other VMs on your cloud), create a rule that accepts incoming traffic just from specific resources, limiting outside communication.
- VPC comes with implied rules (they exist but are not shown). The first one is that outgoing traffic from a resource is allowed to everyone (0.0.0.0/0), and the second one is that incoming traffic is denied from everyone.
- If an instance only needs traffic from a specific port, for example, a webserver listening on port 80, only allow traffic on that port, and if you can, specify also the subnet where incoming traffic is allowed.
- You should never have a firewall rule allowing incoming traffic from any IP range on any port. Resources should have clear rules when it comes to incoming traffic.
- Also, outgoing traffic should be limited as well in case you have a breach on your resources, to prevent data from being stolen from your cloud.
Data Loss Prevention and Network Security
Data Loss Prevention (DLP) is a service that GCP provides to users to help them with their sensitive data for improved network security. If your company allows users to upload documents and pictures to your Google Cloud, you can use DLP to see if they are exposing something that they shouldn’t.
DLP provides an API and you can interact with it programmatically using Cloud DLP Client Library using your favorite language.
Inspecting
DLP allows you to inspect different kinds of data, such as text strings, images, and text files.
When you interact with DLP and depending on the parameters you send to it, DLP scans your content and checks if there is sensitive data exposed by applying different techniques and known patterns to identify valuable data. This can also inspect Cloud Storage files and BigQuery tables.
Redaction
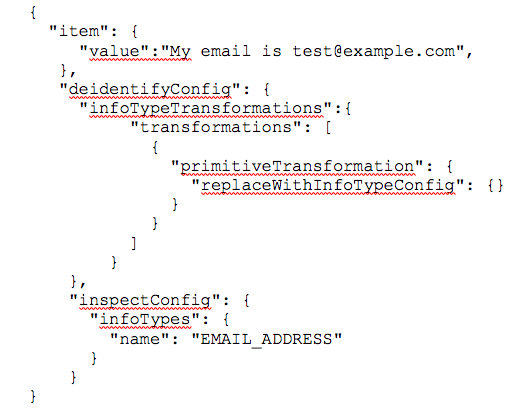
You can also use DLP to not only detect sensitive data but also to hide that data if it is found. You just give DLP the data you have, what is going to be the placeholder that is going to replace the sensitive data, and what type of data you want to hide. For example, to hide an email, you will request this:
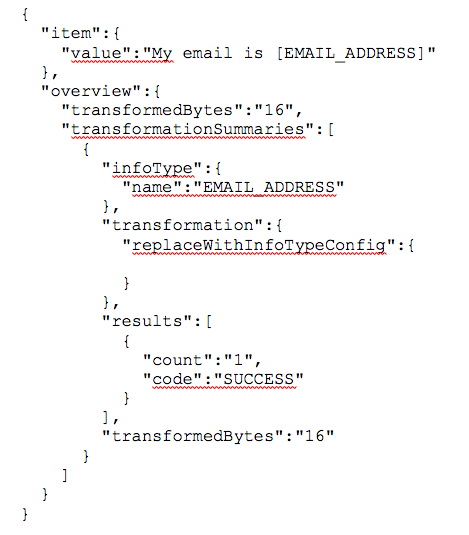
And then, DLP would respond something like this:
Scheduling
You can schedule when Cloud DLP runs jobs by creating job triggers. A job trigger is an event that automates the creation of DLP jobs to scan Google Cloud Platform storage repositories, including Cloud Storage buckets, BigQuery tables, and Cloud Datastore kinds. I hope this has given you a look at some of the important concepts, systems, and features available in the Google Cloud Platform to support running your workloads securely in the cloud.
VerSprite’s Network Security Services
Next time we will finish our look at GCP with a focus on more advanced features such as Cloud Armor, Cloud Security Scanner, and Stackdriver.
To learn more about Google Cloud Platforms, be sure to check out the other blog posts in the series
- The 5 Key Features of Google Stackdriver
- How to Configure Google Cloud Armor
- 5 Techniques to Avoid Unwanted Outcomes with Cloud Security Scanner.
In addition to learn more about cloud security, be sure to check out our posts on Azure and AWS.
Get in touch with VerSprite’s team today to learn about what we can do to improve your network security
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /