PCI DSS 4.0: What You Need to Know and What You Need to Do
Is Your Company Ready to Make the Transition to PCI DSS 4.0?
Joaquin Paredes, Director of Offensive Security Practice
The Payment Card Industry Data Security Standard (PCI DSS) standard, established in September of 2006, was developed to introduce a common set of security standards across the industry. As credit card fraud rose, so did the regulations designed to combat it. In its fourth iteration, the PCI DSS 4.0 provides a detailed baseline of technical and operational requirements to protect account data.
The PCI SSC published the fourth update to the Data Security Standard (DSS) early last year. While many regulations stayed the same, the new standard looks to outcome-based requirements as the primary focus. The 12 DSS requirements didn’t change; however, the latest version has set precise standards to guide companies in implementing security controls, specifically penetration testing (pen testing).
The four main goals are:
- Continue to meet the security needs of the payments industry
- Promote security as an ongoing process
- Add flexibility for different methodologies
- Enhance validation methods
The transition period remains active until March 31, 2024. After that time, all organizations must have made the switch. These changes will affect all merchants and service providers that store, transmit, or process payment card information. If you have a more extensive payment ecosystem, it’s time to think about reviewing these updates to prepare for the transition and possible audits. The most significant change to the new standard is that “best practice” suggestions are now requirements. Your organization must comply with PCI DSS 4.0 by March 31, 2025, and you must re-certify your compliance.
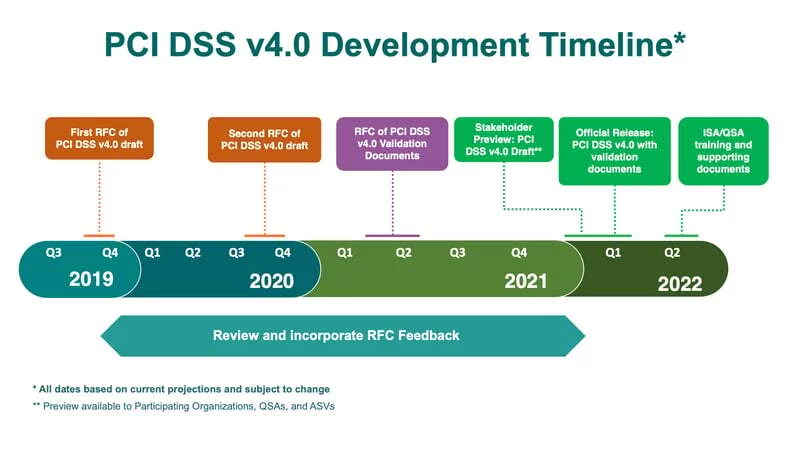
The graphic below will give you the exact timeline:
Penetration Testing Required for PCI DSS Compliance
Penetration testing is still a requirement under PCI DSS 4.0. Not only is it required every 12 months, but the new regulations outline specific approaches to the cardholder data environment (CDE) and any APIs and networks.
The regulations about the scope of the testing have changed—to wit, both inside and outside networks, both trusted and untrusted, must be tested. In addition, pen testing must include external-facing and internal-facing web application components if they touch the CDE. Any security weaknesses must be corrected, and the new rules oblige companies to retest for the same vulnerabilities found in the initial pen tests. This guarantees that the risks have been addressed and the identified vulnerabilities are no longer a threat.
In addition, companies also must retest in the event of any upgrades or changes to the infrastructure or applications. Conducting a penetration testing exercise after major system changes and updates makes good sense; nonetheless, performing penetration tests during the development phase can prevent future issues. It’s now a requirement under the new mandates.
PCI DSS requirement 11.4 states that organizations must define, document, and implement a penetration testing methodology that includes Industry-accepted penetration testing approaches. While the list below is not exhaustive, here are a handful of the requirements that rule 11.4 lays out.
- Coverage for the entirety of the CDE and critical systems.
- Testing of both the inside and outside the network and testing to validate any segmentation and scope reduction controls
- Application-layer penetration testing to identify the vulnerabilities listed in Requirement 6.2.4, such as SQL Injection, XPath Injection, and Cross-Site Scripting.
- Network-layer penetration tests which include all components that support network functions and operating systems.
The new regulations are more specific about who can conduct pen testing. Enterprises can use an internal resource, but the internal resource must have the proper knowledge and skills to execute a penetration test thoroughly and adequately. While an internal source sounds like a way for small businesses to save money, if you don’t have someone qualified to do the testing under these new strictures, you could set yourself up for an audit or, worse, a breach.
The PCI SSC also suggests hiring a provider with specific penetration testing certifications, such as CREST, OSCP, OSCE, CISSP, CEH, and GSNA.
So What’s Next?
The PCI Security Standards Council seems to be moving toward a “zero trust” model, which includes more stringent security measures, more robust authentication standards, and an increase in DESV testing, even for companies that have not been compromised.
The implementation date is March 2025, which is plenty of time to transition. However, there will be a heavier burden for large enterprises, so it makes sense to start work now to ensure that your company is ready. PCI 4.0 requires crucial upgrades regarding user and system access authorization and authentication across an environment. This means that larger companies should begin a review of reporting mechanisms and processes to align their security practices with the new requirements. You can access the Self-Assessment Quiz online and start your analysis.
The consequences of non-compliance aren’t pretty—companies can accrue fines of up to $500,000. That’s not to mention that they could be forced to cease all credit card activity until the issue is resolved. That’s not to mention the hit to your reputation and the loss of customer trust. You must ensure compliance even if your business doesn’t process many credit cards. Level 4 merchants—classified as merchants that process less than 20,000 credit card transactions annually—are at the highest risk for cyberattacks.
If you’re unsure where to begin, it’s a good idea to perform a gap analysis, reviewing the new requirements of version 4.0 and comparing that to where you stand now. There are 64 new requirements, so it’s a good idea to hire a reputable third-party expert to help you along the way. If you miss even one, the stakes are high.
Versprite’s security can guide your business through the complex regulations behind PCI DSS 4.0. Our gap analyses and penetration tests emulate cyber-criminal intent, and we go beyond industry best practices. In addition, we hold most of the certifications required under the new standards. We’ll customize a plan for your business based on attack patterns and threat motives and help you review and implement the best security strategy for your business.
PASTA Threat Modeling: The Process for Attack Simulation and Threat Analysis
VerSprite leverages our PASTA (Process for Attack Simulation and Threat Analysis) methodology to apply a risk-based approach to threat modeling. This methodology integrates business impact, inherent application risk, trust boundaries among application components, correlated threats, and attack patterns that exploit identified weaknesses from the threat modeling exercises.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /