How to Create A Strong Password
Hard Passwords to Crack I How to Create Strong Passwords
When 81% of breaches are due to poor passwords – it’s time to get serious about creating a strong password and a good password protection policy that protects your company’s sensitive data. Our cybersecurity experts will show you how to do both. Skip the article to get help now from our team of cybersecurity professionals. →
Password Protection
The keys to your sensitive company data are defended – sometimes solely – by passwords that a middle-school-aged child could crack. And that pretty much sums up the nightmares of half the security leaders reading this article.
You already know how important it is to ensure your passwords are stronger than the brute-force software attacking your password as we speak. The problem comes in when you ask yourself how to create a strong password and how to create a good password policy that’s both simple and easy to implement.
Let’s start by understanding how passwords are hacked so that you know what you’re up against.
How Does a Password Get Hacked?
The simple and most common answer is – through sheer, brute force attack. Hackers these days subscribe to the motto: work smarter, not harder. Once they know your email address, which is easy to do in most organizations, they can easily spin up a program that continuously attempts to log in to your account using randomly generated combinations of and number sequences. A password hacking program from a beginner could crack an 8-character password in six hours or less. Against seasoned professionals like our team at VerSprite…well, that’s a different story. Let’s just say VerSprite’s Red Team has a 100% success rate at infiltrating company credentials.
There are many ways good passwords get compromised, but our VerSprite security experts see four methods used most often.
The Most Common Ways Password Are Compromised:
Password Leak
-
Brute Force Using a Dictionary Attack
-
Password Spraying Attack
-
Spear Phishing
Just like a motivated ex-partner, hackers will do pretty much anything to get into your head. To gain access to your credentials they often use social engineering tactics like phishing, blowing up your cell phone (what the professionals I work with call SMSing), stalking your social media, and diving into those DMs using a fake account. The goal is to learn enough about your life that they can speed up the process or get you to click on a malicious link that can swipe your credentials.
Nothing is sacred in the war on passwords. Hackers will attempt to gain access to your work credentials whether you’re at work or clocked out. You are the job’s weak defense point and attackers know that.
So, let’s arm you with how to create a strong password that leaves a hacker on read.
(For those of you unfamiliar with my social media terminology, just know it’s funny and true.)
Password Protection: How to Create a Strong Password
It may seem like a universal secret, but generating a strong password is easy once you know the best rules and tools. I recommend using these for your work passwords and your personal passwords. My motives in writing this article may primarily be to keep your security leaders sane, but protecting your private accounts and financials is also a good practice. Now, the rules.
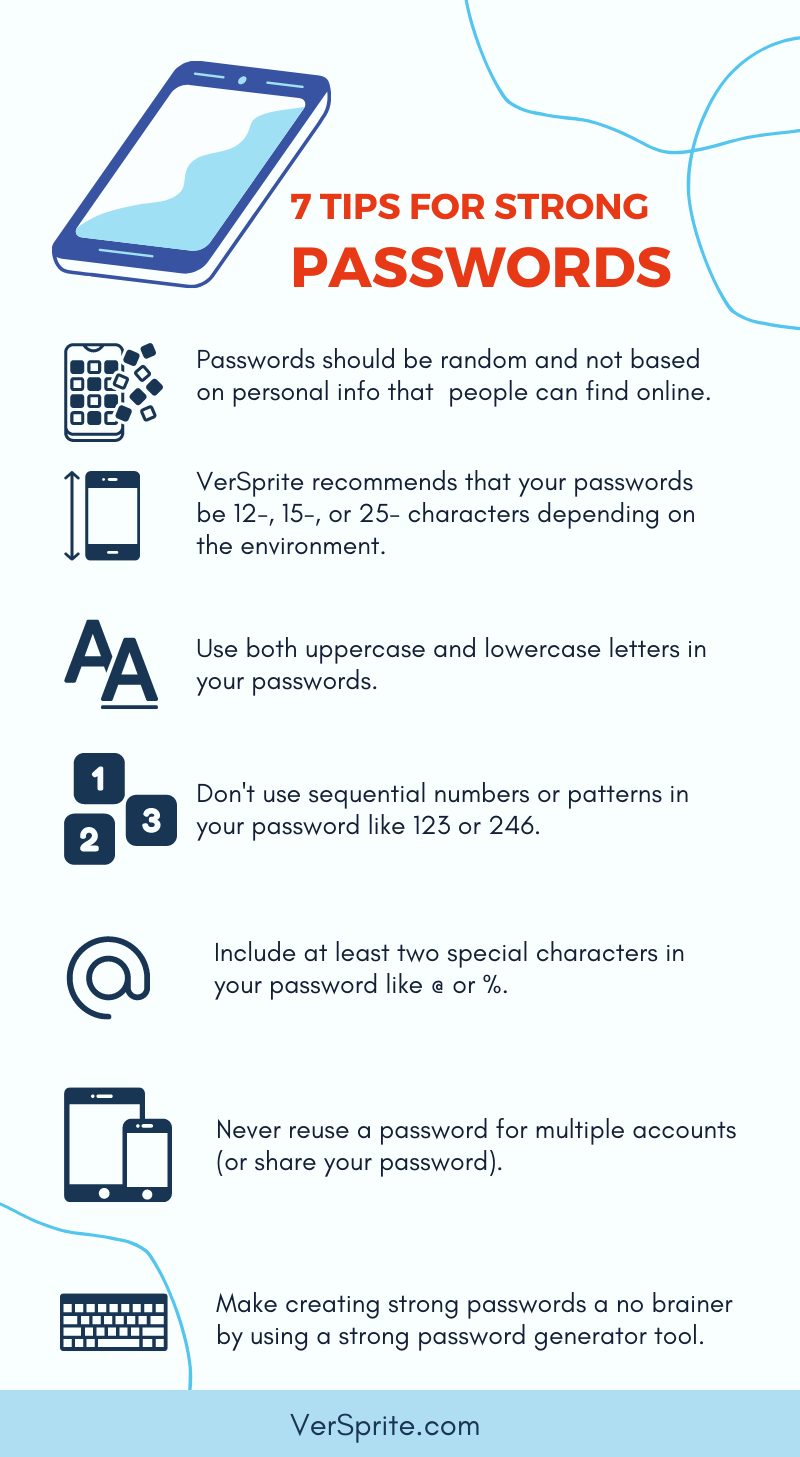
Randomize Your Passwords
Remember, hackers are social media stalking you like a bad ex. They know your dog’s name, your street address, your favorite food and sports team, your child’s teacher’s name, and even your birthday. The biggest mistake most people make is to use words that have a personal meaning to them. That’s how you get things like Rover123 or Sam[insert birthday]. Avoid that by not including any personal words in your password.
Password Length Matters
The National Institute of Standards and Technology (NIST) only recommends an 8-character password. However, our security experts recommend you going beyond that for reasons like we discussed earlier, when a hacker told us it takes six hours or less to crack an 8-character password. Make them work for it. VerSprite recommends 12-, 15-, or 25-character passwords depending on the environment. The more there is to gain from a hacker getting that password, the smarter it is to round up to a higher character count.
CamelCase Your Passwords
This is a funny name for a simple idea. CamelCase passwords mean that they have both lowercase and uppercase letters. It’s easy to forget this rule because we’re trained to only capitalize the first letter of a word or proper noun. No need to go crazy with the capitalization because that just makes the password hard for you to remember. Even adding 1-2 capitalized letters in your password helps. The image below is an example of what an easy-to-remember CamelCase password looks like.
Password Protection: More Do’s and Do Nots
Don’t Use Sequential Numbers or Patterns
Don’t pretend you’re not guilty of using 123 in your password at some point. I know you have – I certainly have – and hackers know you have too. Patterns and sequences make a password easy for you to remember, but also easier to crack. Just recall how SolarWinds got dragged by U.S. lawmakers and security experts for a “solarwinds123” password that got leaked. That’s why the brute force attack hackers use to guess your password are trained to look for sequential numbers and patterns. So, time to retire 123 and start using random numbers.
Include Special Characters
Not every piece of software you use allows special characters (Get with the program, software makers!) but most do. Special characters are things like “!”, “%”, or “@”. Adding these within (not just at the end) of your password is a great password practice. The more dynamic a password, the harder it is to crack.
The Best Password Tip – Use A Strong Password Generator Tool
I recommend using a free password generator to spin up your passwords. Tools like LastPass Password Generator and Norton Password Generator are free to use and adhere to all the rules we just discussed.
Don’t Reuse Passwords
Once you have one strong password, it is tempting to use it for all your accounts. That’s a big security no-no. If a hacker gains access to your password and it’s the same for every business and/or personal account – it’s game over. They won’t stop with the one account. They’ll work their way into your email, cloud storage, LinkedIn account, Manga-of-the-Month club, financial accounts – everything. It’s important to use a unique password for every account you have. If it seems overwhelming to remember a unique password for every account, you’re going to love the next section.
Use a Password Manager to Store Passwords
People have a lot of passwords. A password manager is an application that stores all your strong passwords in one secure vault. And before you admit to allowing your Internet browser to auto-fill your passwords – just stop while you’re ahead.
There are many free and paid password manager options for personal use and company accounts. LastPass, Google Password Manager, and Nordpass are just a few of the more popular password managers on the market. The additional advantage is that many managers have apps and browser extensions that will auto-fill your passwords if you’re signed into the manager. (So, if you do secretly let your browser store passwords, there’s a more secure way to do that.)
If you share a company account with your team members, your manager can share it with all your vaults without giving you access to see the password. I’m still amazed at how this works, but it does.
How Often Should You Change Your Password?
NIST discourages frequently changing your passwords because it makes it hard for you to remember, but software often requires you to change it every 30-90 days based on their security policies. (Those in cybersecurity call this a CYA tactic. If you know, you know.) Complexity is more important than how frequently you update your password. If your software requires you to update, do it. If not, there’s no need to change your password unless there is a data breach, or you suspect your password has been compromised.
Should You Use Multi-Factor Authentication Apps (MFA) or SMS?
Let’s get into how to protect yourself beyond having a strong password. Most software, apps, and social media allow you to opt into multi-factor authentication. Multi-factor Authentication (MFA) is an extra layer of protection where an app or software will not allow someone to sign in using just your username and password. Instead, it will require you to also put in a code that it sends you via text message or through an authentication app on your phone.
Using an authentication app is more secure than using your cell phone number to receive texts. You can use an authentication app like the Google Authenticator app or Microsoft Authenticator App for free. Simply go into your account settings on most programs, apps, and social media accounts to opt-in to MFA. It only takes a few moments to set up MFA, but it can really CYA.
Protect Your Logins So You Don’t Become “That Employee”
Having your own strong password best practices will help you avoid being “that guy/gal” whose credentials are used to allow hackers to gain access to sensitive company data. The key to creating a secure password is to keep it random, never re-use credentials, and use tools like MFA and password managers to help you manage your account logins.
For job-related passwords, your organization should have a password policy that takes some of the burden of creating your standards off your shoulders. Your security leaders, HR team, and security awareness training team can supply those to you if you’ve misplaced them.
Where To Start with Password Protection
I just threw a ton of information onto your screen. If you’re not sure how to implement safe passwords into your personal or professional life, then scroll down to our helpful infographic. You can use VerSprite’s Password Protection infographic below as a checklist the next time you need to create a new account.
Security leaders, HR managers, and fellow marketing nerds in charge of the company’s security awareness training – to test whether your current password policy can go toe-to-toe against a hacker, contact our sales support team to schedule an engagement.
About VerSprite
VerSprite is a global leader in risk-based cybersecurity and PASTA threat modeling. Our offensive security approach goes beyond assessing security controls to examine credible threats to understand the likelihood of real-world abuse cases and measure the magnitude of the business impact if a breach should occur.
VerSprite has proven that by developing a holistic business/IT risk view, security decisions become business decisions. They believe an integrated approach will result in better and more cost-effective security practices and better business outcomes overall. To learn more about our services, visit our service list or contact us to speak to a security advisor today.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /