What is Smishing and Vishing in Cyber Security? Understand Phone-Based Cyber Attacks
Smishing and Vishing Attacks Have Increased 328%, Here’s How to Combat Text Messaging Scams
What Does Smishing and Vishing Mean? How Phishing Via Text Message Works
Phishing attacks (smishing and vishing in cyber security) have been around since the 1990s and as devices have become more mobile, cybercriminals have evolved their techniques to target these mobile devices. One of the reasons phishing emails are so popular among criminals is that there is virtually no barrier to spinning up as many fake email addresses as they want. Just like email phishing, there is little to no barrier to getting a fake phone number nowadays.
Smishing and vishing in cyber security are types of phishing attacks that use text messaging (SMS) and voice calls to manipulate victims into giving over sensitive data to cybercriminals. While all phishing attacks have seen an increase since 2020, Verizon research shows 85% of phishing attacks are now evolving beyond just email to include many variations of phone-based cyber attacks, the most common being smishing and vishing.
Phone-based attackers don’t just target mobile devices to gain your personal information. With the rise of a remote workforce due to COVID-19, many cybercriminals have started targeting company employees on their cell phones to obtain access to company information. It is just as easy to impersonate a text message from a bank as it is from the CEO of a company.
Our cell phones are the new battlefield for cyber attacks.
In this article, we will teach you what smishing and vishing in cybersecurity are, how phone-based cyber attacks work, and how to protect yourself from being a victim.
What is Smishing in Cyber Security?
Smishing, also called SMS phishing, uses social engineering tactics carried out over text messaging. In 2020, those of us in the cybersecurity community saw smishing attacks spike 328% in one year alone. A criminal can us a phone number to send text messages that appear to be from trusted senders, like a bank, a co-worker, or a popular online retailer. The goal is to get you to give the cybercriminal sensitive information.
Most smishing text messages use one of two methods to carry out their scams:
- Malware
You may receive a smishing text designed to trick you to click a URL that will download malware to your phone. The malware might be disguised as a legitimate app to get you to type in sensitive information, such as a discount shopping app that promises 15-25% off popular online retail stores.
- Malicious Website
An SMS phishing message may contain a URL that takes you to a malicious website designed to look like a legitimate site. It’s meant to trick you into typing in your sensitive personal information that feeds straight into the cybercriminal’s hands.
Victims of smishing cyber attacks often don’t know they have fallen for a text messaging scam until much later, when an attacker uses the information collected.
How Does Smishing Work?
Smishing attackers use social engineering tactics to manipulate their victims. Impersonation, fraud, and fear are key drivers behind any SMS phishing attack.
There are three main manipulation tactics SMS phishing uses:
- Emotional Triggers:
Often smishing will target a victim’s emotions by pressing on their sense of fear or urgency, hoping that it will bypass the person’s critical thinking and force them to act. This may be done by calling out a false transaction on their account to make the victim think their card is stolen to trick them to clicking a link to approve or dispute it. Or it may be as simple as creating a time limit to an offer and saying there are limited items available. An example of this is if the text messages offers something too good to be true, like a PS5 game console available at a 15% discount at the link provided.
- Name Recognition:
Cybercriminals often target specific individuals, especially if they are targeting someone to gain access to an organization’s sensitive data. Through simple social media searching, criminals can know who is in your life so they can disguise themselves as that person – they use trusted names you’ll recognize in their fraud. The video below this section is one example of using CEO Fraud to scam an office worker.
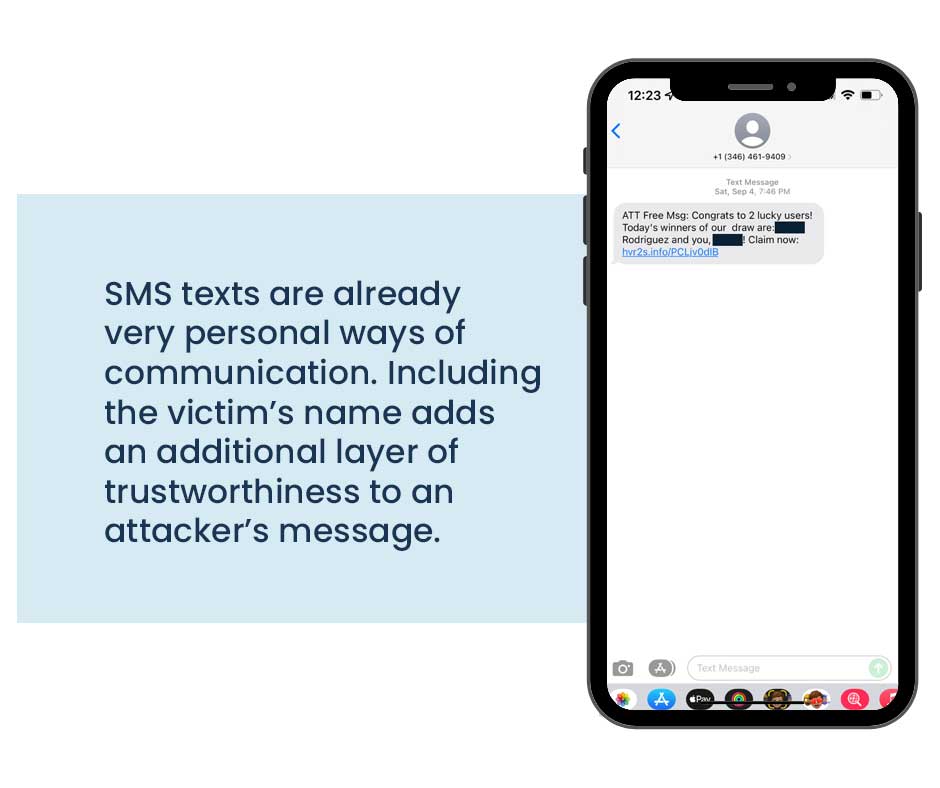
- Personalization:
Ask anyone in marketing and they can tell you that personalizing content makes it more likely for people to feel a connection to the sender and it lowers the target’s skepticism. SMS texts are already very personal ways of communication, and by adding the victim’s name – something easily obtained – it adds an additional layer of trust to the message.
Similar to our explanation of how email phishing works, the first stage of any SMS phishing campaign is about choosing the target. Targets may be chosen for various reasons, including their affiliation to a bank, to their employer, from lists publicly available on the dark web, or simply by chance. Unlike email addresses, which must be known before an attacker can disseminate the malware to the victim, phone numbers can be strung together at random. This, coupled with Gartner’s observations that that phone users read 98% of text messages and respond to 45% of them makes text message attacks so alluring to cybercriminals. The odds are in their favor.
Once the attacker chooses the number they’re going to target, they will design a campaign to match the reason why people were chosen. The attacker will disguise themselves to be affiliated with the institution they hope to gain access to, such as a bank, to gain access to your financial information. They may also disguise themselves as an employee at the company you work for.
Smishing attackers can use a method called spoofing to disguise their real phone number as another number. Spoofing has become easier to do with the rise in providers of email-to-text services that can be used to hide phone numbers to look like legitimate senders. The phisher may also purchase a “burner phone” (an inexpensive, disposable prepaid phone) for an additional layer of protection.
The attacker then creates a way to obtain the information they want, either by malware dissemination or through a malicious website, and designs the message they want to send. Once it has sent, they sit back and wait to collect the data they were looking for or try additional messaging until one resonates with the target.
What is Vishing in Cyber Security?
Vishing stands for voice phishing, and it is a type of phishing attack conducted over the phone. In this case, vishing attackers fake their caller ID to appear to be calling from an 800-number or from a local area code to the victim. Some attackers may use their real voice to appear more trustworthy, or they may disguise their voice by using a recorded voice system. This is a popular attack method to use because VoIP users are not required to provide proof to obtain caller ID data, which means they can easily disguise themselves as anyone. (VoIP stands for Voice Over Internet Protocol phones.)
Vishing attacks have similar motives to smishing including, obtaining financial information and personal information, like billing addresses and social security numbers. However, between a long history of telemarketer fatigue and the cultural shift to uses SMS messaging over calling, people are less likely to pick up the phone or call an unknown number back. This has opened the door for more smishing attacks, but vishing is still very much a danger to phone users.
How Does Vishing Work?
Vishing attackers also use social engineering tactics to manipulate their victims into providing personal information. Because speaking to someone on the phone feels personal and trustworthy, maybe more so than a text message, victims are more likely to feel safe providing their sensitive personal information to the caller.
While the manipulation tactics used to obtain information are similar to smishing, vishing attackers uses two distinct methods to carry out their scams:
- Person-to-Person Communication
Many attackers use pre-recorded scripts to make their original call because they’re sending out several calls at once. When a person does get on the line with a human, the attacker relies on the familiarity and trustworthiness many people still have when talking to someone person-to-person. Attackers may disguise themselves as a collection’s agency for an overdue bill, a financial institution looking to verify a phishy charge on an account, or (the internet’s personal favorite) someone looking to renew your car’s warranty. The attacker will ask for personal information to pretend to use to verify the target is the owner of the account, then try to get financial information.
- Voicemail Hooks
When leaving a voicemail, attackers may leave callback phone numbers to increase the guise that the call came from a legitimate organization. Once the victim calls them back, attackers can use an automated answering service or, for larger organized crime syndicates, may employ a real call center to obtain the personal information and/or financial information of the victim.
Voice scams are harder to do when the objective is to target a company’s employees, but it does happen and they are successful. Since the shift to remote work, voice phishers target employees by disguising themselves as IT department members and, in large organizations, as supervisors of departments the targeted employee may not regularly interact with.
Recently, a major vishing scam was uncovered where attackers sent fake order receipts for Microsoft Defender subscriptions that included a phone number for targets to call if they wanted to process a return. Victims who called the number spoke to attackers who requested they install AnyDesk so the attacker connect to the victim’s computer to initiate a Remote Desktop Protocol (RDP) attack. In another vishing attack, the vishers used deepfake technology to synthesize the voice of a company executive to defraud the company. The synthesized voice demanded the employee pay an overdue invoice, which was followed up by a fake email from the executive. The employee transferred funds to the victim that were not recovered.
Prevent Smishing and Vishing
There is no way to guarantee that you won’t be the target of a smishing or vishing attack. The most effective way to combat these cyber attacks are to use common sense and trust no one. Smishing and vishing in cyber security attackers are skilled at creating emotional responses from people so always make sure you pause to consider what the caller or text message is asking you to do.
If you’re being contacted by a supposed co-worker, use your own verification tactics to confirm if the employee is true.
- Look them up in the company directory or messaging software
- Ask your manager if they can help verify the caller
- Get a full name and phone number that your HR department could verify
- Report the interaction to your IT or security team before divulging any information or clicking links
When being contacted on your personal phone, you are the first and sometimes only defense against the attacker.
Update Your Security Awareness Training
Understanding how cybercriminals target you through your phone is important but it’s also important to remember that you aren’t just being targeted as an individual. Employees are a company’s weakest link because there are so many ways to fall for scams, and it only takes one to be successful. You might be more vigilant on your work-issued computer because you’re trained to look out for phishing emails or suspicious websites while working but you may be less cautious on your personal phone.
It’s important to have the same level of security awareness training to employees for their personal devices as with their company devices. There is no distinction to cybercriminals whether they use social engineering on your company email address or your personal cell phone. Many smishing and vishing in cyber security attacks go unreported because they happen on personal time and on personal devices. But even if you recognize that a text or call as phishy, it doesn’t mean everyone in your company will. If you see something, say something.
Phishing has been around since the 1990s and it continues to evolve to stay effective. We must evolve our security awareness, training, and vigilance to keep up with these attacks. The more aware we are the more we can hope to be successful at thwarting the cybercriminals.
For more information on how you can browse securely or learn how to protect your organization in the age of BYOD, reach out to our security analysts for a consultation.
VerSprite for Help with Smishing and Vishing in Cyber Security
VerSprite is a global leader in risk-based cybersecurity and PASTA threat modeling. Our offensive security approach goes beyond assessing security controls to examine credible threats to understand the likelihood of real-world abuse cases and measure the magnitude of the business impact if a breach should occur.
VerSprite has proven that by developing a holistic business/IT risk view, security decisions become business decisions. They believe an integrated approach will result in better and more cost-effective security practices and better business outcomes overall. To learn more about our services, visit our service list or contact us to speak to a smishing and vishing in cyber security advisor today.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /