Is Using Public WiFi Safe?
How to protect against hackers and man-in-the-middle attacks while on open WiFi networks
With the increase of remote work, organizations must teach their employees how to stay safe on open public WiFi networks, which is a prize target for man-in-the-middle cyber attacks. Get our tips on how to protect against hackers while on open WiFi networks. Get Tailored Security Awareness Training →
Public WiFi has never been more of a threat to business as it is today. In the past, organizations were able to control the security of the networks their employees logged into but the mass migration to remote work has left us in a situation whereby we can work from anywhere – from any WiFi.
It can be tempting to work at a coffee shop or use your hotel’s free internet, but those same public hotspots are targets for cybercriminals looking to steal your data. So, before you log in at Starbucks, it’s important to understand what makes public WiFi networks so dangerous and how to defend your data.
What are the Risks of Using Unsecured WiFi Networks?
The biggest threat of using a free WiFi is the ability for a hacker to position themselves between you and the connection point. This is called a man-in-the-middle attack (MiTM). If a hacker is on the same unsecured WiFi as you and you start entering data, such as credentials or financial information – they have ability to access this data. Our own Director of OffSec likes to use a specific man-in-the-middle attack called EvilTwin when targeting clients’ employees that use open WiFi networks. Remember that everyone, including the owner of the network, can see everything you do!
Hackers can also use this type of connection to distribute malware to your machine, which is called malware injection. So, ensuring the antivirus tools are up to date on devices you use to connect is important.
How Can You Stay Safe on Public WiFi?
As unrealistic as it sounds, the most effective way for you to stay safe on public WiFi is not to use it. We know that’s not always going to be possible, so if you wake up tomorrow and find yourself in a situation where you must access company data while on a public WiFi, or you just really need a Grande Chai Latte to get you through your morning meetings – we get it. Here are some tips you can use to stay safe.
Don’t Connect to Unknown Open WiFi Networks
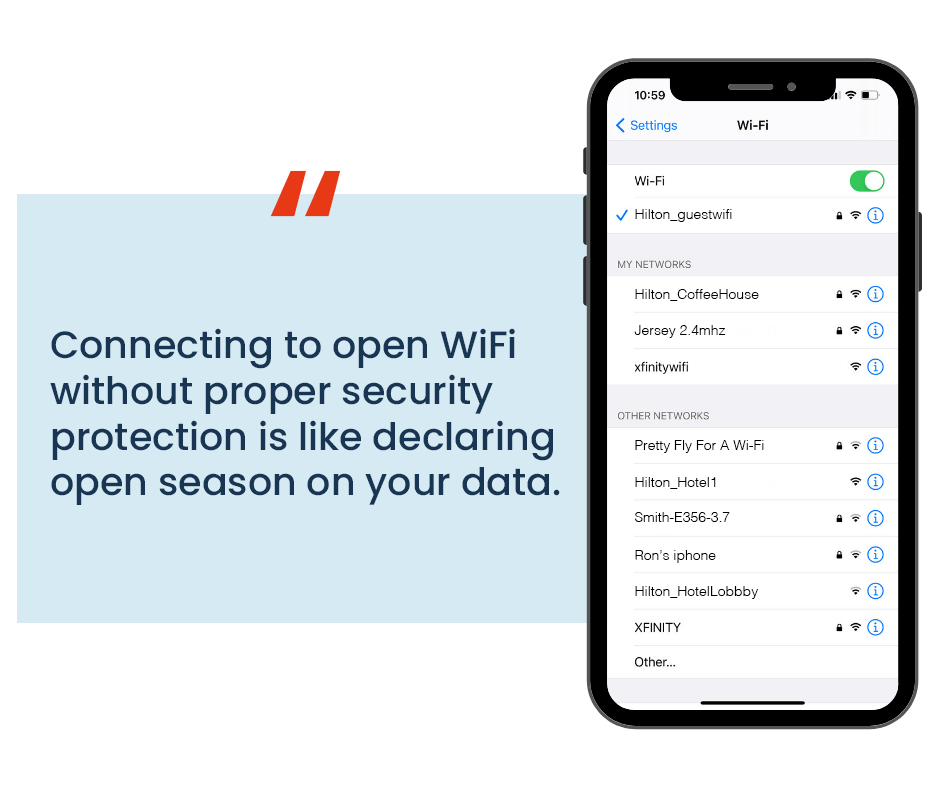
When you open your WiFi connection on your computer, tablet, or cell phone you will see a list of available networks to connect to. Instead of randomly picking the one with the most bars or the one that doesn’t require a password, take a moment to assess the available networks. You may be tempted to use an available network that doesn’t require a password, but don’t fall for the scam. Many of these networks are malicious hotspots that hackers use to suck in unsuspecting internet surfers, giving them full access to see into your browsing. Avoid those for more reputable networks like a nearby business, coffee shop, school, or your own personal hotspot if you have one. You may also need to use your elementary spelling bee skills to find the networks that don’t have extra numbers or misspelled words. That is often a giveaway for a malicious network.
Take the image below as an example. This hypothetical individual had many options to choose from, including password protected networks and open ones. Upon further detective skills, they could determine that Hilton_guestwifi was their hotel’s legitimate WiFi for guests.
- It didn’t have spelling errors (like Hilton_HotelLobbb)
- Not as obviously, it required a password which most hotel hotspots do now
Use a VPN
Always connect to a VPN when possible. Virtual Private Networks (VPNs) create a secure connection between your device and the internet by using an encrypted and secure connection to the VPN server. Although they’re mostly known for helping you watch your favorite TV shows from different countries, VPNs are a great way to secure your browsing. They help prevent man-in-the-middle attacks and network snooping.
Keep Your Anti-Virus Software Up to Date
We all get those annoying messages about updating software or the newest Windows patch, but they have a purpose. Using anti-virus software (also known as AV software) alone won’t completely protect you from attack but they do provide an additional layer of protection to help keep you safe. As new threats are detected and patches made, companies roll these out to your software in the form of “Updates”. It’s important to update so you can protect yourself from new risks. By not updating, you continue to be at risk for threats.
Turn off File Sharing
Having file sharing ability, like Apple’s AirDrop feature, can be useful to collaborate with co-workers and to share files between your devices. However, it is also an easy vector for cybercriminals to find a way into your device. We recommend you always have file sharing turned off when not in use and to select the option that makes your device undiscoverable to others. This is especially true while you’re in public areas where there are more people around that could discover and manipulate your devices.
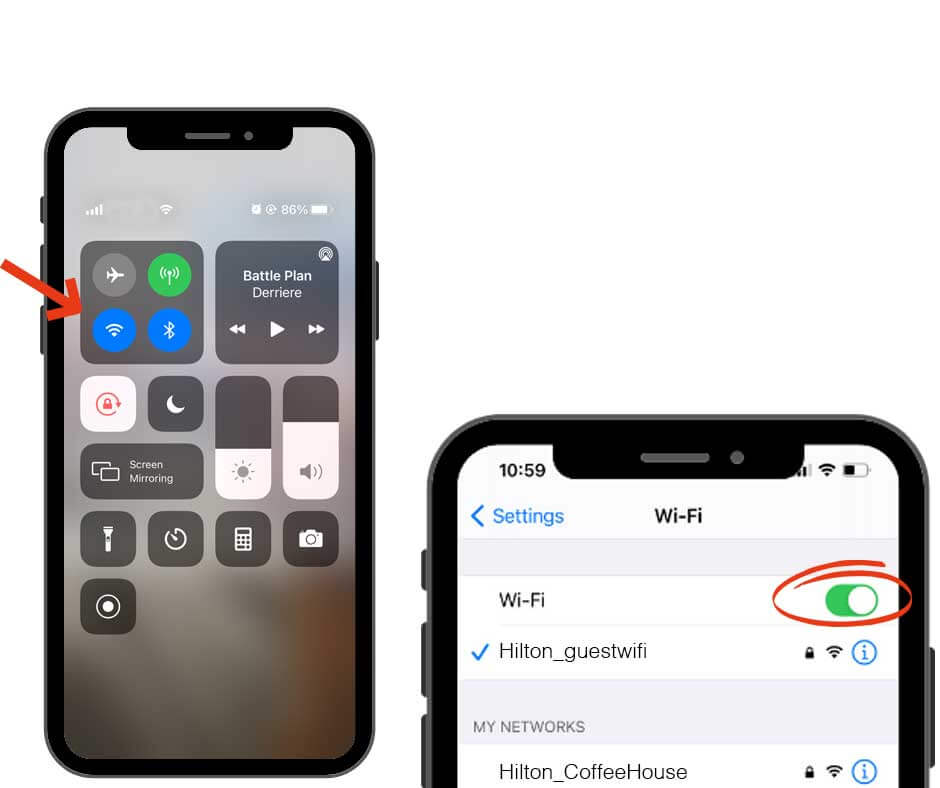
Turn Off WiFi When Not Actively in Use
Have you ever been driving and noticed your phone connect to a nearby WiFi network? It can seem like a helpful feature to ensure you always have connection, but it can also be a vector to invade your device. If you select to not automatically connect to a network, this will prevent your device from connecting while you are unaware of it.
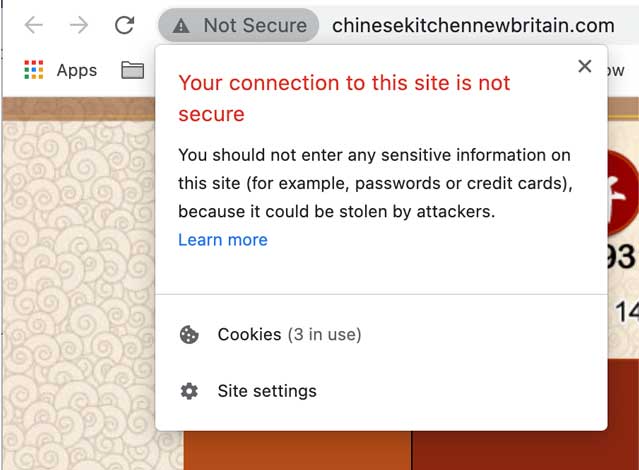
Ensure Websites You Access Use HTTPS
Every website you visit will either be an HTTP or an HTTPS. The HTTP is simply the protocol used to take a website and make it available to anyone on the internet. HTTPS does the same thing with the additional layer of security. It helps protect your website browsing and purchasing by encrypting data you give to a website and using TLS to verify the other end of the transaction. HTTPS helps prevent man-in-the-middle attacks, although it is not 100% secure, you should never visit HTTP.
Reboot Your Device After Disconnecting from WiFi
Rebooting your device after disconnecting from an unsecure WiFi allows your phone or computer to reset everything for you and scan itself. If when you restart your AV software there are malicious files on your device, it is more likely to catch it on reboot. Most importantly, if there are any rogue processes on your device that are detected, your AV software should shut them down.
Public WiFi Also Draws in Physical Threats to Your Devices
When cybercriminals search for easy targets, they aren’t just trying to virtually infiltrate devices. Have you ever been in a coffee shop and, when the barista calls your name, rushed to grab your drink? That split second when your device is unattended, and potentially unlocked, could be all someone needs to slip in. Did you leave your first and last name as your hotspot name? This also gives attackers personal information they can use against you. And all they had to do was roll into Starbucks. Attackers know hotspots draw in more unsuspecting internet users, and they take full advantage of this. Beyond protecting yourself from virtual attacks, always remember the laziest way to get into your devices is to physically be in possession of it.
So, Is It Dangerous to Use Public WiFi?
Yes and no. Connecting to open WiFi without proper security protection is like declaring open season on your data. It can allow anyone else on that network access to your personal files. However, if you take the proper precautions then you can absolutely use a reputable public hotspot with peace of mind. Remember, public WiFi is not secure by default; you need to be defensive and take measures to use it in a secure way. You hold the largest key in keeping your browsing secure while on unsecure networks.
For more information on how you can browse securely or learn how to protect your organization in the age of BYOD, reach out to our security analystsfor a consultation.
About VerSprite
VerSprite is a global leader in risk-based cybersecurity and PASTA threat modeling. Our offensive security approach goes beyond assessing security controls to examine credible threats to understand the likelihood of real-world abuse cases and measure the magnitude of the business impact if a breach should occur.
VerSprite has proven that by developing a holistic business/IT risk view, security decisions become business decisions. They believe an integrated approach will result in better and more cost-effective security practices and better business outcomes overall. To learn more about our services, visit our service list or contact us to speak to a security advisor today.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /