Zero Trust – a Trendy Buzzword or a Future of Cybersecurity?
Zero Trust security is the hot trend and a buzzword in the cybersecurity world right now. But what is behind the buzz? In general, it is a cybersecurity concept that is based on a principal of eliminating implicit trust to assets or users and verifying all access. Current cyber threat landscape and trends make this concept very appealing for organizations. However, how exactly does Zero Trust work? Is it the new way to pro-actively secure your organization, or is it a costly investment with a potential to overwhelm already complex enterprise network operations?
In this article, we break down what Zero Trust actually is and the reality of its implementation into the highly-complex, hybrid enterprises in the work-from-anywhere era.
Zero Trust term was first coined in 1994 by Stephen Paul Marsh, computer science professor at University of Sterling, and popularized by a Forrester Researcher John Kindevag in the early 2000s. They challenged the concept of trust relating to the cybersecurity and computer field. Zero Trust was presented as an approach that always assumes breach and continuously verifies each access, regardless of whether the request comes from the inside or outside the network, while asserting least privilege. Zero Trust Security assumes there is no traditional network edge and everything is hostile by default. No application, access request, user, employee, or link should be trusted.
National Institute of Standards and Technology (NIST) defines Zero Trust as a collection of concepts and ideas designed to minimize uncertainty in enforcing accurate, least privilege per-request access decisions in information systems and services in the face of a network viewed as compromised. An enterprise’s cybersecurity plan that utilizes zero trust concepts and encompasses component relationships, workflow planning, and access policies is defined as Zero Trust Architecture (ZTA). Therefore, a zero-trust enterprise is the network infrastructure (physical and virtual) and operational policies that are in place for an enterprise as a product of a zero trust architecture plan.
A few years after the Zero Trust concept was first introduced, Google announced that they had implemented Zero Trust security in their network, which sparked a growing interest in adoption within the tech community. In 2019, Gartner, a global research and advisory firm, listed Zero Trust security access as a core component of secure access service edge (SASE) solutions. Since 2021 all US Federal agencies must adhere to NIST 800-207 Zero Trust policies.
As a result, Zero Trust is being widely marketed and adopted by private enterprises. Frameworks are developed around the concept, incorporating AI and automation. While the philosophy of the Zero Trust concept – never trust, always verify – makes for a very attractive selling point promising uncompromisable cybersecurity defense, the implementation and adoption process is complex, continuous, and it is not a stand-alone, one-fits-all solution. It is not an AI powered band-aid, implementation of which can make an organization an impenetrable cyber-fortress. Rather, it is a strategic process that gradually raises an organization’s cybersecurity maturity level by implementing core security principals and transforming the security culture to meet the demands of evolving networks, cyber trends, and the change in work environments.
What are the main principles of a Zero Trust Model?
NIST offers the following 7 guidelines for Zero Trust architecture design and deployment:
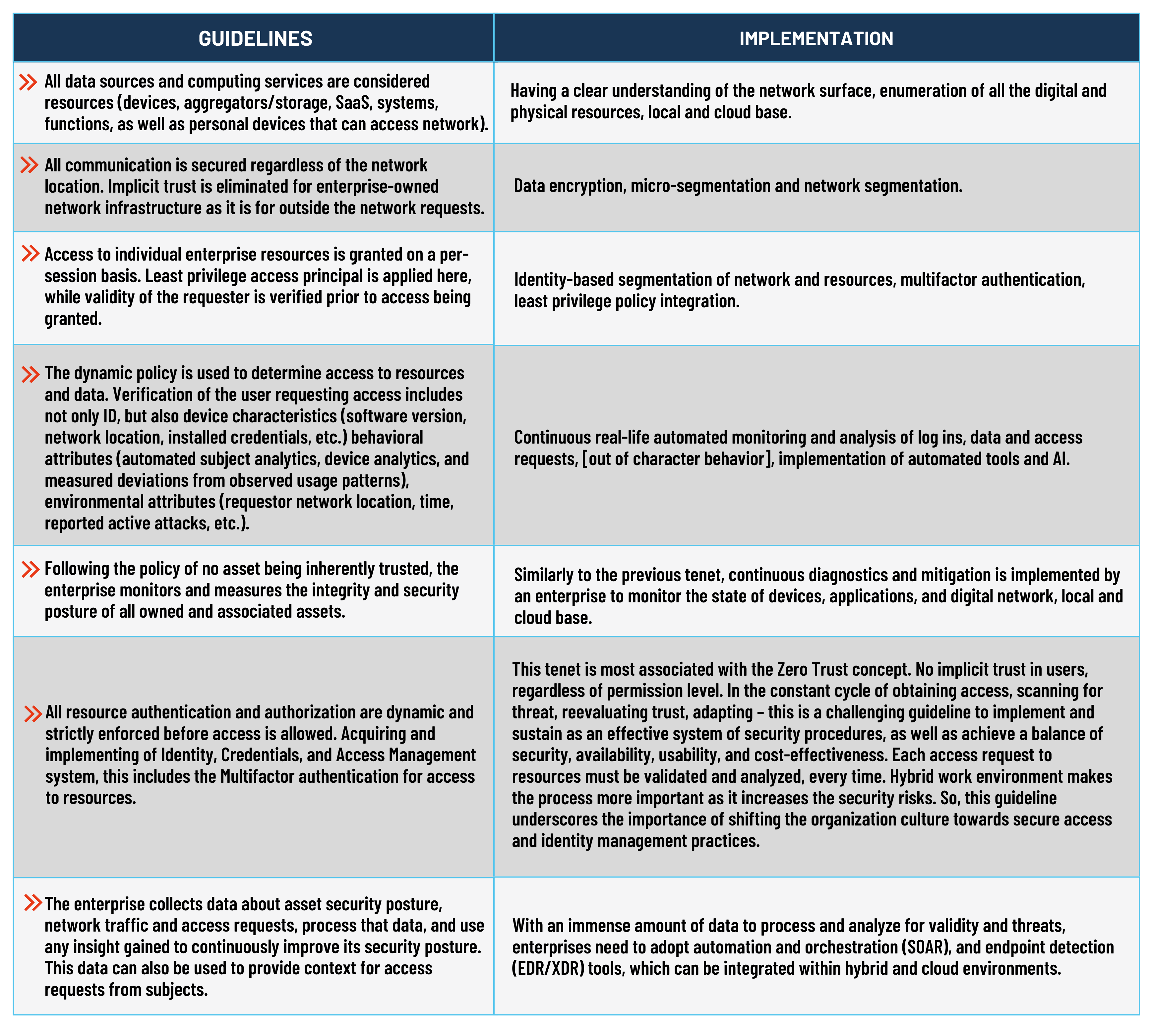
So, as we can see, Zero Trust goes beyond the common simple definition of never trust, always verify, least privilege implementation, and assuming breach. Zero Trust is a complex concept of maturing cybersecurity, aimed at not only securing, but changing the culture of enterprise operations. The castle and the moat approaches do not work anymore because we have remote users and workers, cloud environments, SaaS applications. Organizations need to shift their security policies and approaches to ensure business continuity. However, Zero Trust is not a simple tool, its implementation can be complicated by the organization’s policies that are in place, cybersecurity culture and budget, as well as hybrid environments and legacy networks and technology. There is no single approach or architecture that can be applied to any organization without consideration of its workflow, networks, and industry specific threats. Zero Trust takes a holistic view of the organization and potential risks.
The shift towards a better and more modern cybersecurity is a multi-layer process which includes, along with threat modeling and threat monitoring, Zero Trust Architecture – an enterprise’s cybersecurity plan that utilizes zero trust concepts and encompasses component relationships, workflow planning, and access policies. The complex approach should start with threat modeling and assessing of the scope of an enterprise network, implementing the concepts of Zero Trust, and an employment of monitoring tools or service.
Let’s break down what those processes mean. Zero Trust, as established, runs on principles of continuous monitoring and validation, least privilege, device access control, micro-segmentation, MFA, and identity-based segmentation. Per NISTs guidance, Zero Trust Architecture is derived from these principles and, in general, includes the following components:
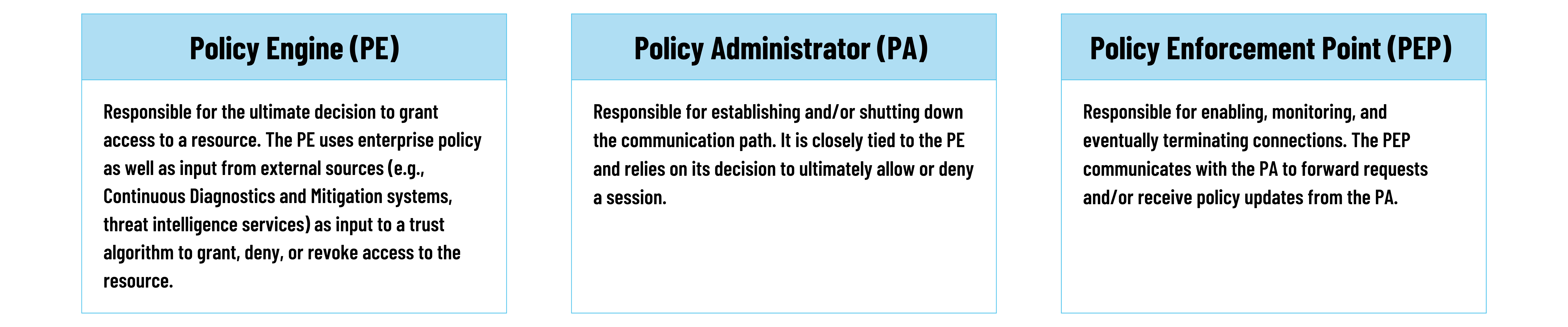
These Zero Trust Architecture components help to establish the implementation strategy of Zero Trust concepts within an organization. They guide the process to maturing complex enterprise cybersecurity:
- Threat and Network Assessments – determining attack surface, identify assets, credentials and privilege distribution, assessing infrastructure, reviewing policies and protocols etc. Threat modeling can be a great tool for an organization to kick start the Zero Trust journey.
- Establishing Zero Trust Security Measures, such as MFAs, least privilege principle, network and identity segmentation.
- Continuous Network Monitoring – employing automation and SOC tools (or virtual SOC) to analyze logs, requests, and activity in real-time without interruption.
Migration to Zero Trust and more mature cybersecurity is a long-term process and a commitment for a company. Building a successful plan for the transition takes cooperation of all partners within an organization, starting with employees to security team, and the C-Suite level executives. Zero Trust can be a major undertaking for enterprises and require budget and operational changes. However, the strategy brings both value and security. It removes the complexity of networks, improves safety and user experience, as well as allowing for a cybersecurity structure that adjusts to current cyber trends.
Shift Towards a Better & More Modern Cybersecurity
VerSprite provides enterprises with results to support their security efforts, meet business objectives, and provide stakeholders and decision-makers with solutions and guidance to scale the business.
Subscribe for Our Updates
Please enter your email address and receive the latest updates.