What Is a Phishing Attack & How to Spot Phishing Emails
DON’T FALL VICTIM TO PHISHING SCAMS: Work from Home Cybersecurity Education for Employees Online
Phishing is the easiest way criminals execute ransomware, and that makes it one of the most dangerous cyber threats to businesses today. As phishing evolves to be more believable, you must understand how to spot a phishing email and what’s at stake.
Too much Phish in Your pond? Get Help to Fight Phishing →

What Is a Phishing Attack?
Phishing is an attack where criminals impersonate a legitimate person or company to obtain sensitive information such as passwords, usernames, or financial access. It’s one of the oldest types of cyber attacks there is, dating back to the 1990s, and yet it’s still wildly successful. Phishing is usually done via email but has evolved beyond that to include messages sent through social media, phone calls, or text messages. However, email is still the most common vector for phishing attacks because it is very easy for criminals to do and very easy to fall for.
How Does a Phishing Attack Work?
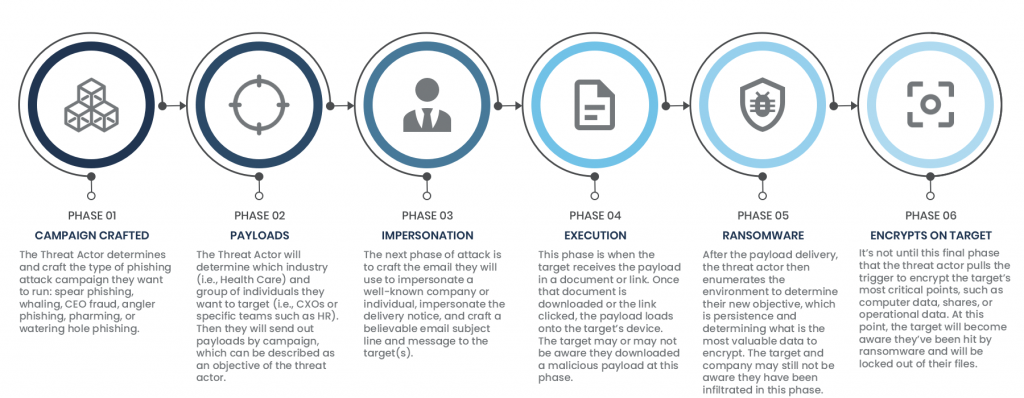
How phishing works may differ based on the end goal and the method used. Corporations can expect to be phished to get access to their valuable data and the best way to do this is through ransomware. Ransomware is a type of malicious software, or malware, that infects the computer it was downloaded on and encrypts its data before spreading to as many computers as it can – often infecting entire networks and servers. Once ransomware infects your computer or network and decides to trigger the encryption of your files, that’s it – you are locked out. The hackers will have access to everything on your computer and they often hold your systems for ransom.
How Does Phishing and Ransomware Work?
Companies that fall victim to phishing and ransomware attacks often must pay exorbitant amounts of money to get access back or risk losing everything, like Garmin who was hit by a $10 million ransom last year. That’s a lot of motivation to go after your inbox.
And while we would all like to believe that we would never fall for phishing emails, it happens every day. In fact, since the start of 2020 it’s hard to go more than a week or two before hearing news that another company has fallen for one of these cyber attacks. Even with all the security training around phishing attacks, 65% of successful phishing attempts happen in companies that conduct anti-phishing training to their employees.
Phishing training isn’t enough anymore. There’s a war going on in our inbox and we are the weakest link in our own defenses. You don’t have to be a security expert to learn how to avoid getting hooked by phishers. This article will explain the different types of phishing, how to spot phishing emails, and give you six tips to avoid getting phished.
Types of Phishing Techniques
Now that you know what phishing is, we’re going to teach you the most common forms of phishing techniques so you will be prepared when one comes your way. There are many types of phishing techniques hackers use but the most common types we see over email are Spear Phishing, Whale Phishing, and CEO fraud.
Spear Phishing
Spear Phishing is when the criminal designs a message to target a specific individual or specific group of people. The phisher can use basic internet Google skills to learn who works at a company and then ‘spoof’ (aka, fake) the “sent from” email address to look like it’s coming from a co-worker. For example, you may be in the sales department and get an email from a phisher claiming to be with your IT department that asks you to download a new software the company is implementing. Spear phishing can be done in small organizations, where everyone knows everyone, and in large enterprises where employees are used to being pinged with requests by people they don’t regularly interact with.
Whale Phishing
Whale phishing, or whaling, is a type of spear phishing that targets CEOs and other high value people within a company. These targets take more time to get information on and often take multiple tries before something resonates with the target. To pull off whaling, attackers must craft believable emails that would prompt the target to click, download, or pay. If you are a CEO, board member, VP, or Director of a company, you need to be hyperaware of the target on your back. Always question the information coming into your inbox.
CEO Fraud
CEO fraud is a type of spear phishing email attack when the phisher impersonates the CEO to target an employee. These are very common because employees are more likely to act when someone in authority tells them to do something – even if it’s not within their standard job duties. For instance, a phisher may decide to disguise themself as a CEO and email a new employee in the accounting department to ask them to wire money.
This spear phishing email example was sent from VerSprite’s Red Team and impersonated a company IT member.
How to Spot a Phishing Email
Even with the types of phishing techniques stacking up, there are a few common tactics hackers use that you can look out for. In most cases, a malicious sender can spoof (aka, fake) their email “from” address to look like it’s from a reputable source. They may send a link or attachment that executes malicious code, or they may send the target to a fake website created to intercept a payment or login credentials.
Internet memes will make you believe that the criminals who send phishing emails are bad at what they do. There is a stereotype around email scams with the narrative that faux emails are corny and easy to spot. (Remember the time when it was commonplace to get emails from a Nigerian Prince?) This isn’t the case anymore. Hackers have evolved their techniques over time – they even have marketing and PR companies to represent them. Their phishing attempts are sophisticated and easily look like emails sent from trusted sources.
It’s honestly just the Hunger Games out there.
The image below is a phishing attempt by one of our Red Team members. This email successfully got the target – our client’s employee in charge of social media – to click on the link that resulted in us obtaining access to their social media account. We learned enough about the company and their employees to be able to make it seem like our email was from another employee of the company. (Learn more about that fun engagement.) If we were a malicious hacker, we could have done serious damage to the company’s reputation.
This phishing email was sent from VerSprite’s Red Team. The victim fell for the ploy, which gave us access to the company’s social media ccount.
How to Avoid Phishing
There is no one way to avoid getting phished. The biggest drivers towards inbox safety come from a combination of efforts from employees and comprehensive security policies and tools by your work. There are ways to be more alert about inbox fraud, though.
Don’t Trust Anything You Get in Your Inbox
Like we showed earlier with our client’s social media manager – it’s very easy to fake who is sending an email to you. The best policy as an employee is not to trust anything that comes into your inbox. Before you take any action on an email, always verify that the sender’s email address is correct.
As a cybersecurity company, we regularly try to trip up our own employees (and, if need be, eat our own words). Be on the lookout for not just emails from outside the company, but also from within. If your coffee-hating boss is giving away free coffee to the entire company – you should question if it’s CEO fraud. If the CEO is offering beaucoup bonuses, like we did in a recent internal phishing test – question that too. Things that seem too good to be true often are.
This phishing email was sent from VerSprite’s Red Team to VerSprite’s own employees. We believe as cybersecurity experts that we must be tested as well.
The bottom line is that whether you’re a cybersecurity expert or a college intern, you need to approach your inbox with a certain amount of skepticism.
Don’t Click on Links
This tip is an oldie but goodie. Although criminals are working on ways to execute malware just by opening an email, 90% of the time you still need to take action within an email to allow malware to hit. This means either clicking on a link, such as a coffee store gift card like in our security awareness skit below or downloading an attachment.
Cyber-criminals use pain points to entice you to click. They may put a sense of urgency to click a link, they may name-drop an executive as being the driver behind their request, or they may offer you something too good to pass up. Even if the sender is promising you a million dollars – don’t click on anything.
If it Looks Phishy – Call the Sender
Hackers are intelligent. They know who your boss is, your friends, family, and even the principal of your kid’s school. Company employees are easy to track down using sites like LinkedIn that name an entire company’s employee roster. Scammers will try to impersonate people to get what they want from you. It’s up to you to know your inbox correspondents deeper than the phishers.
As you get emails, take a moment to assess the email and ask yourself critical thinking questions like, is your normally typo-crazy boss sending you a grammatically perfect email? Did your best friend really misspell your name? Have you ever spoken to the employee emailing you before? Your biggest weapon against email scams is to be inbox skeptical.
VerSprite’s IT administrator, Mike Charette, is famous for reminding our employees, “If you think the email came from someone you know but seems weird, call them on the phone and ask them.” Use an alternative form of communication to verify an email is legitimately from the sender. If a questionable email comes from an internal source – use your company’s internal messaging software, like Slack or Microsoft Teams, to look up the employee and ping them. If the email is from an external vendor, then pick up the phone and give them a call.
Send Unknown Senders to Spam
Criminals know there are certain positions within a company that work regularly with outside vendors. Marketing, sales, purchasing managers, business development, and executives can expect to get communication from outside the company. You are easy targets. It would feel like any other Tuesday to get an email from a sender offering for you to buy their email list or poking your sense of fear that an invoice you don’t remember is past due. But if you don’t know the sender, it’s best to report it to your IT department and then send it to your spam folder.
Use Your Company’s Communication Policy as a Weapon
This is the modern-day version of Mike’s advice earlier to pick up the phone. Since we’ve all agreed to become inbox skeptics, never trust an email just because it looks like it’s coming from within your organization. If you get a phishy email from a co-worker, go back to the book on your company’s communication policy. Does your company encourage you to use email to contact co-workers? If not, use what your company recommends for internal dialogue, maybe Slack or Microsoft Teams, and send the sender a message on that platform to question the validity of the email. Does the request from the sender usually require you to get a manager’s permission? If so, use the corporate method of putting that sender on blast and CC your manger into the conversation. Companies have communication policies for this very reason, it’s not just to track how much time you and your co-workers spend sending each other FriYay GIFs. It’s also there to help you fight phishing.
Report Phishing Emails to IT
The IT department is your company’s unsung heroes. Their whole job is to help you master technology. It’s likely that if you’re seeing a spam email, other people in your office are too. Your IT department can blacklist senders, monitor email use, and send company-wide emails to warn co-workers. They’re also there to fight your battles if you do end up falling victim to a phishing attack. (That being said, try to report if you suspect an email is phishing because some companies use fake phishing attempts to spot who need another round of phishing training. Our clients may or may not be these companies. Just a fair warning.)
What Is the Future of Phishing?
There are many ways to spot phishing, but the fact remains that phishing is probably not going anywhere. As people get more familiar with how to spot phishing emails and new forms of communication emerge, phishers will adapt their ways to keep the scam alive. There’s a reason why phishing is still around after nearly thirty years – people still fall for it, which means the payouts are still worth it to the criminals. So even though you may think you know how to spot a phishing attack today, it’s critical to keep being skeptical and keep updating yourself on phishing trends as they emerge.
If you have questions on how to spot phishing or how to combat it within your company – contact our security sales advisors.
About VerSprite
VerSprite is a global leader in risk-based cybersecurity and PASTA threat modeling. Our offensive security approach goes beyond assessing security controls to examine credible threats to understand the likelihood of real-world abuse cases and measure the magnitude of the business impact if a breach should occur.
VerSprite has proven that by developing a holistic business/IT risk view, security decisions become business decisions. They believe an integrated approach will result in better and more cost-effective security practices and better business outcomes overall. To learn more about our services, visit our service list or contact us to speak to a security advisor today.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /