Ransomware Readiness – When Failing is Good
One of the oldest cybercrimes – ransomware – is seeing a rapid growth in the past couple of years. Tensed geopolitical landscape and troubled economies worldwide are making ransomware even more attractive for the cybercriminals. It is a crime that pays well. According to the FBI report, ransomware attacks costed organizations almost $50 million in 2021 alone. It is a 66% increase from the prior year.
Why should organizations be concerned?
Ransomware is getting more sophisticated and threat actors are expanding into new industries, leaving virtually no company safe. Some of the prime targets for threat actors are becoming global supply chains, managed service providers (MSPs), retail, banking and finance, healthcare, and utilities. Ransomware can have a long-lasting effect on companies. It can damage brand reputation, lead to a high remediation cost and a loss of revenue and assets, as well as create a potential for future access and sensitive information release.
To better prepare for a ransomware attack and protect its assets, an organization must adopt proactive security mindset to stay ahead of cybercriminals.
What can help improve resilience against ransomware?
Standard ransomware preparedness includes:
- Maintaining a secure data backup and having data recovery included into the Disaster Recovery plan.
- Making sure that Incident Response playbook is up-to-date and includes emerging ransomware trends.
- Having an Organizational Threat Model (OTM) based on threat-centric adversarial exercises.
Despite the ransomware (and cybercrime, in general) growing in numbers and sophistication, we are still seeing that the defense against ransomware remains largely reactive.
Let’s look at it this way. You can build a beautiful new boat, equip it with the latest technology and navigation, hire the best team. But it’s not until the boat sails that all the systems can truly be checked and any leaks can be detected. You wouldn’t take the boat first time on the deep-sea sailing trip. If anything was missed, it can well cost you the boat. An organization’s security framework is no different. Yet, many company set up security activities, tools, and processes, most of which are compliance-driven, and operate without an evaluation of how well the system actually works or if there are any gaps in security. It leaves an organization vulnerable to cyberattacks.
It is common for companies to focus attention on compliance and policies, strengthening their security posture through standardized frameworks and tools. While it does make your company stronger, the standardized frameworks can create a false sense of security and resilience, as one component can be missing from the equation – the weak points and security gaps, which cybercriminals look to exploit.
Proactive Mindset Solution: Red Team Engagement
To effectively protect your organization against cyber threats, you must conduct proactive engagements that challenge physical and network security. In this blog, we take a look at red team threat modeling assessment as one of the most effective ways to mitigate risks. By performing a red team engagement, organizations can test the effectiveness of their technology, processes, awareness training, and security framework overall.
A thorough red team engagement will discover the vulnerabilities and weak points across all the attack surfaces. And while hiring a team to break through the defenses a company worked hard to implement might seem counterproductive, a failed red teaming exercise gives an opportunity to improve the security posture by discovering where it is at its weakest.
Red teaming goes beyond assessments and penetration testing. Its scope is unlimited across all legal and ethical vectors. It allows for not only uncovering of the vulnerabilities, but determining their risk-level affecting organization’s assets, employees, and technology.
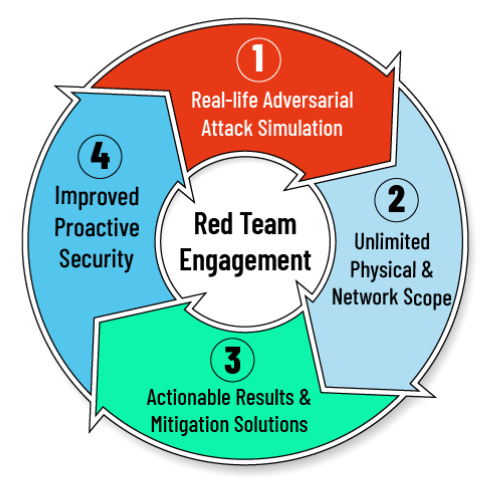
Red team simulates real-life attackers’ motivations and attack patterns to push the boundaries beyond what is thought to be possible. It is the closest you can get to truly knowing your organization’s security stance. So, we argue in favor of red teams because their goal to assess the true, relevant risks aligned with the business objectives of the company being targeting. Performed annually, red teaming ensures an organization’s security posture remains at its strongest.
One of the VerSprite’s clients, Director of Risk Management at a Leading Global Insurance Group, commented this on why his organization was integrating red teaming into their security procedures, “It has been a really useful test and as you say some great stuff has come out of this, be it from yourselves on the technical side or internally as your teams’ actions stressed our internal processes and procedures. This exercise created quite a lot of excitement and others can now see really benefit from starting to embed such testing into our standard processes.”
The results a red team engagement provides are actionable. The detailed report shows not only discovered vulnerabilities and weaknesses in the security, but also offers mitigation strategies to help protect the organization from ransomware, as well as other cybercrimes.
VerSprite’s Red Team assessment provides a detailed overview of the results of all performed attacks and exercises. Each security issue is qualified, documented, and mitigation is advised on the case-by-case basis.
Integrated into the cybersecurity procedures, Red Team engagement becomes an ultimate tool in protecting your organization’s assets, developing an effective threat model, and giving your stakeholders a peace of mind to focus on scaling the business.
For more information on how your organization can better prepare against ransomware, contact our team of experts.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /