A Red Teaming Engagement Can Prevent Cybersecurity Attacks
Can Physical Security Weaknesses Enable Physical and Cyber Attacks?
Physical security weaknesses can enable physical and cyberattacks; a red teaming engagement can help prevent them.
Any random passerby on the street has physical access to the car you left parked in the parking lot, but that should not mean you should expect any of them to start it and drive away effortlessly. Any modern vehicle will put up defenses that increase the costs for nearly all attackers to keep your car where you left it. We expect physical security of our phones as well, assuming we encrypt the phone and secure it with strong passphrase and biometrics.
What happens once a threat actor has physical access to an information system or any other item of interest? Your first thought may be that all is lost. That the game is over. This mindset is wrong.
Any random passerby on the street has physical access to the car you left parked in the parking lot, but that should not mean you should expect any of them to start it and drive away effortlessly. Any modern vehicle will put up defenses that increase the costs for nearly all attackers to keep your car where you left it. We expect physical security of our phones as well, assuming we encrypt the phone and secure it with strong passphrases and biometrics. Physical security attacks are easier than you think. Learn about how a red teaming engagement can protect your organization’s security.
Why Physical Security Attacks are Easy
Any modern organization should have physical security sufficient to quickly discourage nearly every possible attack and enable efficient detection of active attacks. However, as is quite often the case, during red teaming engagements and assessments, we find that physical security stops at the front door:
- Workstations are not encrypted.
- Network ports are not locked down.
- Flash drives containing sensitive data are placed in unlocked drawers.
- Printouts of customer and client data are piled on desks.
- Electronic equipment and confidential documents are placed behind doors with insecure locking mechanisms.
- The primary backup server is in the same building and even the same room as the original data.
Security requires a layered approach, known in the industry as “defense in depth.” Stakeholders should place proper emphasis on secure software development practices, hardening system configurations, and tightening firewall rules. However, the physical security of the very things we are trying to protect often goes overlooked. Next-generation-machine-learning-in-a-box with bright blinky lights means little if the doors protecting networking equipment or a room full of blank checks and customer data can be opened with a smile at reception and a hotel key card. Most organizations have some level of physical security in place. Still, you will never know how effective your securities are until they have been stress-tested to see if the elements that make it up – like locks, cameras, and policies – can handle the scrutiny of a simulated physical attack.
We will recap real-life red teaming engagement findings, and we helped organizations avoid security attacks.
This Real-Life Red Teaming Engagement Example Proves Organizations are Not Prepared
Is your organization prepared to respond to a physical attack incident? Our experience says, no. Incident response plans may be developed out of theory in a meeting room but never stressed. In a real-life stress test conducted by VerSprite, a client hired us for a red teaming engagement. In the day following an after-hours break-in that we oversaw, a security team member spotted us on their cameras and performed an investigation into what we may have done within their offices. As it turns out, their incident response procedures had serious gaps we exploited to allow a rogue device we planted to go undetected for the duration of the engagement after our break-in was discovered.
Exposing Gaps in Post-Breach Investigations
Unfortunately for us, and fortunately for our client, someone happened to review the CCTV footage.
To pass compliance, the client had to have a certain number of CCTV cameras in specific locations. One CCTV camera was facing the network closet where they stored laptops and networking gear, but they were not required to have a camera in the closet, so there was no camera inside.
The CCTV footage of our physical breach was reviewed, and the client’s security personnel noticed we spent a lot of time rifling through drawers, capturing photos, and gaining access to the network closet by sliding a hotel key card between the strike plate and latch. The individuals reviewing the CCTV footage, unaware of the red teaming engagement exercises, understandably thought it was odd that we spent so much in that room. What they found on camera was that we walked out with one of the company’s laptops.
In a post-breach debrief with the client, we found out they thought the only thing we took was a laptop. They searched the network closet to see if we did anything else and could not find anything. What did we do in the network closet? We planted a rogue device that gave us access to their internal corporate network. A single misplaced cable, installed by us to connect our rogue device to their network, was hanging out of the rack. We left this cable as a clue, but as it turns out, that cable went overlooked during their investigation.
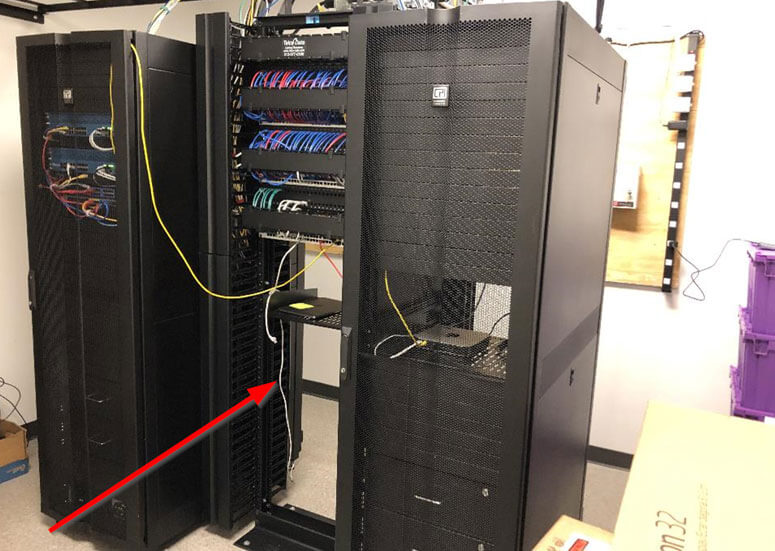
Due to this oversight, our team had access to their internal network for several weeks, uncovering a wide variety of insecure Jenkins deployments, AWS keys on open network shares, and weak credentials leading directly to customer PII corporate banking details. While the findings in the internal network are concerning, what is equally disturbing is how easily we gained access to the networking racks using nothing more than a hotel key card. While we broke in at night, any employee or member of the cleaning crew could have done the same thing and likely have never been caught.
Through the red teaming engagement, the client learned the importance of formalizing and thoroughly testing incident response plans to ensure the aftereffects of a breach are thoroughly addressed and managed as part of an exhaustive investigation. In addition, we helped them realize the inadequacy of their door locks and camera placement.
Red Teaming Engagement Shows Physical Attackers Use Tailgating, Badge Cloning, and Dust for Fingerprinting Keypads
In nearly every physical security assessment, we find a way to break in. In one red teaming engagement, the building our client occupied had security guards on staff 24/7. The client had a small office in the building, and the objectives were to gain access to the office, gain access to sensitive data on workstations, and plant a rogue device. During the day with employees in the small office, planting the device would be difficult, so we decided to perform the attack after-hours.
We tailgated employees to gain access to the building during the day, and then we walked around long enough for our badge cloner to clone badges. The cloned badges allowed us to enter the building not only during business hours but also after-hours. Unfortunately, while we could enter the building, the elevators were locked and would require an override by building security. Dealing with building security after-hours was risky, so we looked for alternatives. We did some online research and managed to find a detailed map of the building. We planned a route that would bypass the security desk and security cameras, leading us through a maze of hallways to a set of stairs that were unlocked. We managed to walk up ten flights of stairs to get to our client’s office door without being stopped or questioned.
At the client’s office door, we saw a keypad:
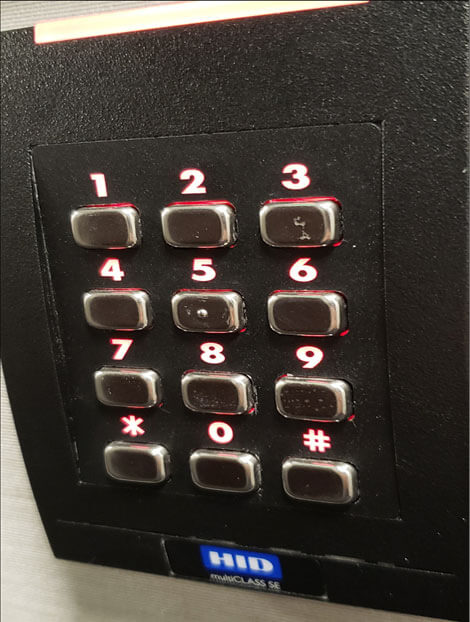
By taking photos at various angles, studying the marks, and noticing the food particles and dead skin cells jammed in the crevasses between buttons and the plastic panel, we could generate a list of possible numbers for a PIN. In this case, we figured that 2, 3, 5, 8, 9, and 0 were likely candidates. We generated all possible 4-digit combinations of these digits and compared this to public research on the probability of a given 4-digit PIN code being used. Taking from the top candidates, we found a code to unlock the door!
Once inside the office, we identified several concerning things about the office’s state of physical security. Aside from the usual array of clean-desk policy violations and insecure Request-To-Exit (REX) door sensors, we found other things that are typically overlooked.
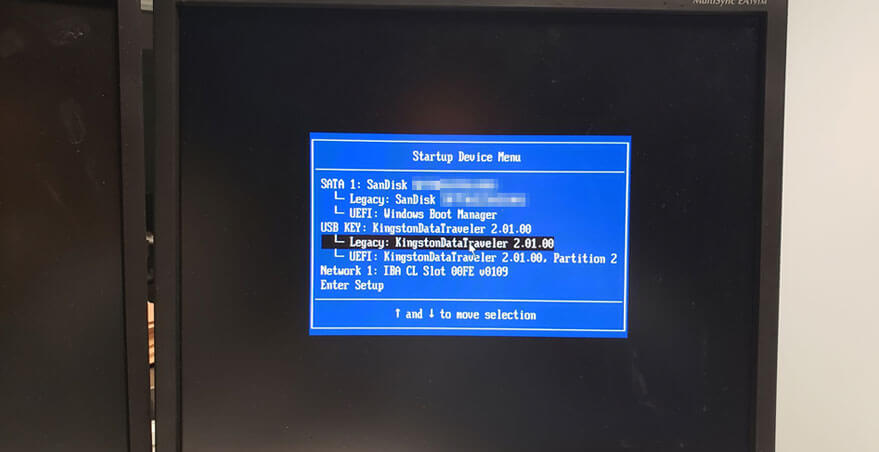
One issue was that USB ports were not disabled on the workstations, despite a policy about employees not being permitted to use USB devices. To exploit this, we used the BashBunney in combination with the QuickCreds script to trick Windows into installing a fake Ethernet adapter and performing NTLM authentication with our device, allowing us to obtain hashes that we could later crack to login to the workstations.

In cases where we could not crack the hashes to log in to a workstation, we were able to boot to a Live Kali operating system on a flash drive. This led us to realize the storage drives were not encrypted with BitLocker or any other full-disk encryption solution. So, booting to a Kali Live OS allowed us another way to gain access to business-critical data and place backdoors on the workstations.
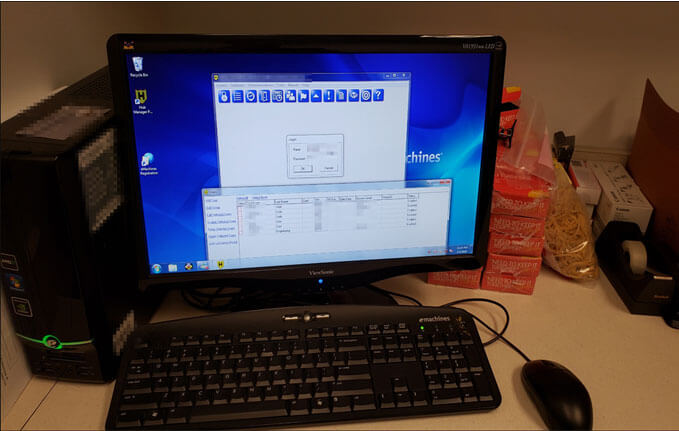
After continuing our search, we found that the computer responsible for mainlining physical access controls to the office, namely the HID card reader and keypad we saw out front, was in the break room. To make matters worse, this computer had no password for the administrative user. Hence, we could play the part of a malicious employee or unscrupulous visitor and copy all the existing PIN codes or even create our own. (We didn’t, of course, but the next person may not be as gracious!)
What Can Be Learned from a Red Teaming Engagement?
Red teaming assessments should allow your organization to identify systemic issues rather than finding just one way and calling it quits. In a real-world situation, a malicious infiltrator won’t stop after the first try. So, we always try different approaches to highlight systemic problems. It is not enough to say, “we broke in once, and here is how we did it.” Given all the different attack motives, it is essential to show all the different ways anyone could compromise an organization and highlight all the systemic issues missed by everyone else. So, it is with that we move on placing a rogue device on their network.
Weak Wireless Security Can Lead to Physical Breaches
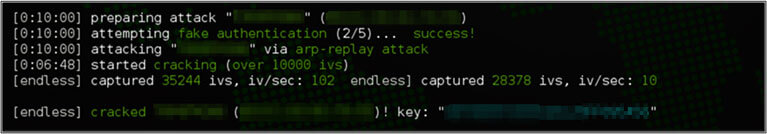
On one red teaming engagement, we found that the client had a forgotten wireless network that was “secured” with Wired Equivalent Privacy, or WEP. WEP is a predecessor to WPA wireless security and is considered severely broken. Any WEP password can be cracked in a matter of seconds, regardless of complexity.
In debriefing with the client, it was revealed that the wireless network was supposed to be taken down a long time ago. Still, the ticket got lost, staff changed, anyone that would have remembered it did not work there any longer, and it has been years since an inventory was done of wireless networks.
Within a few minutes of arriving on-site – while sitting in our car in the parking lot – we found this wireless network and cracked the password in seconds.
We connected to the WEP network, scanned their internal network, and discovered a Honeywell NetAXS keycard security system:
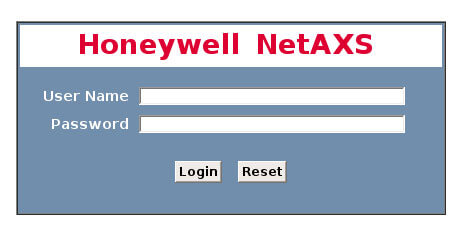
We were able to log in through brute-force to view live security camera feeds from inside their office:
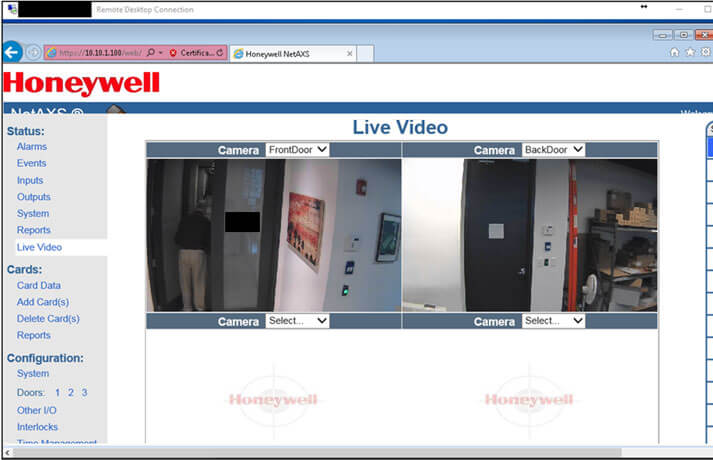
Further, we found that the web interface allowed us to disable the magnet locks on the doors manually. This allowed us to come back during after-hours to unlock the doors and have free reign of their offices. We use that after-hours access to plant voice recorders, locate business-critical data on their computers, and ultimately gained access to propriety source code by tapping into their network equipment.
The lesson here is clear and outlined very well in the 20 CIS Controls: continuously inventory hardware assets and software assets and ensure that assets are securely configured. If you do not know what you have, you will not know where your vulnerabilities can be.
Final Thoughts on Red Teaming Engagements
Of course, you can try to find these security gaps yourself, but first – recall the quote we mentioned in the first blog post in this series:
“One thing a person cannot do, no matter how rigorous his analysis or heroic his imagination, is to draw up a list of things that would never occur to him.”
– Thomas Schelling, Nobel Laureate
Here is where creative thinking from an unbiased outsider, that cultivates the hacker mindset, comes into play. A partner like this can see angles missed by others to expose overlooked weaknesses. Otherwise, you may knock one issue off the checklist while unintentionally leaving several other problems overlooked. These issues will only be spotted by unbiased, trained eyes, like those of myself and those on our Red Team, that has an innate interest in breaking past barriers, showing organization how it can be done, and offering a hand in helping you grow past them.
How Can You Test Your Physical and Cyber Security Controls?
In this last iteration of this series, security expert, James Sibley, broke down how VerSprite’s red team used physical security weaknesses to gain access into organizations. Follow the links below to read about other examples of cybersecurity weaknesses uncovered by VerSprite’s team in real-life:
- Attacking Your Assumptions: How Criminal Tactics Can Save Your Organization
- Security Awareness Training and Social Engineering Techniques
Contact VerSprite for a Red Teaming Engagement
Don’t become a real-life example of an organization that had physical security attacks against them. A red teaming engagement by VerSprite’s experienced cybersecurity team is your ultimate defense.
Contact VerSprite today to get started.
Put Your Physical and Cyber Security To The Test
VerSprite’s Offensive Security team focuses on emulating cybercrime and simulating test scenarios that reflect real-life attack patterns, taking in consideration threat actor’s motives and business objectives. Our team can perform risk-based penetration testing, vulnerability assessments, red teaming exercises, and custom organizational threat models to expose your security gaps before your attackers do.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /