Nordstream Pipelines Attacks
Geopolitical Risk Assessment
Russia – Ukraine Conflict and Its Impact on the Cyber Threat Landscape
Nordstream Pipelines Attacks | Bottom Line Up Front (BLUF)
Russia’s attempt to annex parts of Ukraine created a broader contention between nations and drew Western nations into the conflict. The sabotage of the Russian Nordstream 1 & 2 pipelines may be an act of further escalation and may lead to possible Russian retaliatory actions similar to Nordstream Pipelines Attacks. Petroleum revenues decrease, and so does Russia’s ability to fight a prolonged conflict. Therefore, analysts expect more violence and casualties in conflict zones, as well as increased cyber-attacks against western nations.
Summary
On September 26th, at 02:03 local time (CEST), an explosion was detected, registering a 2.3 magnitude originating from the Baltic Sea at the Nordstream 2 location. Shortly after, a second explosion was detected seventy-five miles away at Nordstream 1. The explosions consisted of several hundred kilos of explosives. Over the following day, four leaks were discovered, which impacted both pipelines. The leaks have stopped due to a lack of fuel supply to the pipes. When this report was produced, the pipelines remained damaged and inoperable.

Multiple countries have been blamed for the Nordstream Pipelines Attacks. The US and multiple NATO countries accused Russia of sabotage, claiming this was an attempt to unite the Russian people over a false flag attack. Russia accused the US of the attack, stating that US energy firms would gain an increase in revenue since the leaks were discovered. There has not been any evidence provided for these attributions.
In June, the US Central Intelligence Agency warned European nations, including Germany, that two Nordstream pipelines could be targeted in forthcoming attacks. The US President also discussed this, when he stated in a February 2nd joint announcement of the US and Germany pledge of unity and sanctions, which drove further speculation.
During that announcement, President Biden stated that Nordstream 2 could be shut down if Russia invades. “We will bring an end to it. … I promise you. We will be able to do it.”
This statement could be incendiary for the Russians, who could use it to make a case for further escalation. Additionally, Under Secretary of State for Political Affairs, Victoria Nuland, announced on January 26th “I want to be very clear: if Russia invades Ukraine one way or another, Nordstream 2 will not move forward… I am not going to get into the specifics. We will work with Germany to ensure it does not move forward.”
Since the leaks were discovered, there have been multiple unconfirmed reports regarding US, NATO, and Russian military presence in the area. NATO reported the presence of Russian unmanned submersibles in the area around the pipeline sabotage. Other sources reported that US helicopters were in the region on September 2nd, September 22nd-23rd, and September 25th-26th. This military presence does not indicate any responsibility.
NATO Secretary General Jens Stoltenberg responded with the following statement, “NATO is committed to deterring and defending against hybrid attacks. Any deliberate attack against Allies’ critical infrastructure would be met with a united and determined response.”
EU Foreign Policy Chief Josep Borrell, echoed that sentiment, saying, “Any deliberate disruption of European energy infrastructure is utterly unacceptable and will be met with a robust and united response.”
Prior to the incident, neither pipeline was in operational use. Nordstream 1 was shut down indefinitely by Gazprom on September 2nd over safety concerns. Nordstream 2 was completed but awaiting inspection and certification by Germany and NATO authorities.
Since the incident, Russia has reportedly responded by deploying a nuclear submarine (Belgorod) from its home port in the Kara Sea. This submarine is capable of delivering the Poseidon Drone. While untested, the Poseidon Drone (Intercontinental Nuclear-Powered Nuclear-Armed Autonomous Torpedo) can travel long distances underwater, delivering and detonating a power variable nuclear bomb. Experts estimate its power to be two megatons or more, which can create a “Nuclear Tsunami” and decimate coastal areas. There are no countermeasures developed for this weapon system.
Russia has also moved a Russian Military Nuclear Division in the region closer to the railway system, which carries tactical nuclear devices. It raised concerns as recent news broke that the executive responsible for that railway was killed by a gunshot on his balcony. The Russian government claimed that his death was a suicide. However, Russia’s claim is not credible, as many executives of Gazprom and other oil executives have died in the last few months in a similar manner.
There was a recent announcement of the construction of a Denmark-Poland Baltic Pipeline. Experts believe that this suggests NATO involvement in the Nordstream 1 & 2 pipeline sabotage. On September 27th, leaders from Poland, Norway, and Denmark announced they would begin transporting natural gas from the Norwegian shelf via Denmark and through the Baltic Sea to Poland. This pipeline runs nearly 30 miles west of the two Nordstream 1 & 2 explosions.
Russia has also increased propaganda campaigns focusing on the justification for utilizing nuclear weapons. A post on Twitter from the Russian Embassy claims the two atomic weapons that the US dropped on Japan in WW2 set a precedent.
2023 Update:
New information came out after two Substack articles about concerning behavior leading up to the time of the explosions:
– “How America Took Out the Nord Stream Pipeline” by Seymour Hersch
– “Blowing Holes in Seymour Hersh’s Pipe Dream” by Oliver Alexander
Both writers seem to have convincing arguments and insightful information, but both provide information that has gaps in analysis of the Nordstream Pipeline attacks.
- The evidence shows that from June 5-17, NATO ships operating during BALTOPS 22 were within the proximity of both blast sights but not directly above. It does not account for the possible use of personnel and unmanned underwater assets to place charges on the pipelines during and between the time of the sabotage.

- Evidence shows that on September 2nd, US Helicopter FFAB123 flew directly to the area, eight miles west of Nordstream 2, making several circles.

- Both authors do not detail the significant geopolitical efforts around the Baltic Pipeline opening ceremony, which was scheduled for the day after the explosion. Note that the Baltic Pipeline is co-financed by the Connecting Europe Facility of the European Union. The Baltic Pipeline is over thirty kilometers west of where the Nordstream pipelines were sabotaged.
The Nordstream Pipelines were Russia’s significant bargaining/ influencing effort in Europe. Germany held negotiations with Saudi Arabia around the same time as the previous activities. TIG does not mention these details to assign attribution, however, it’s crucial so that the reader has all the details of both sides of the situation.
Russia’s FSB—formerly the KGB–conducts a strategy called “Ideological Subversion,” which means to change the perception of reality to such a degree that despite the abundance of information, no one can come to a sensible conclusion to defend themselves or their country.
It means that despite a significant amount of information on the possibility of the European partnerships conducting the sabotage, Russia could have also done the sabotage to escalate the conflict further. This would put Russia in a position to gain support where it did not exist after invading Ukraine. Geo-political posturing could benefit Russia and provide them a reason for escalating their direct action and cyber activities.
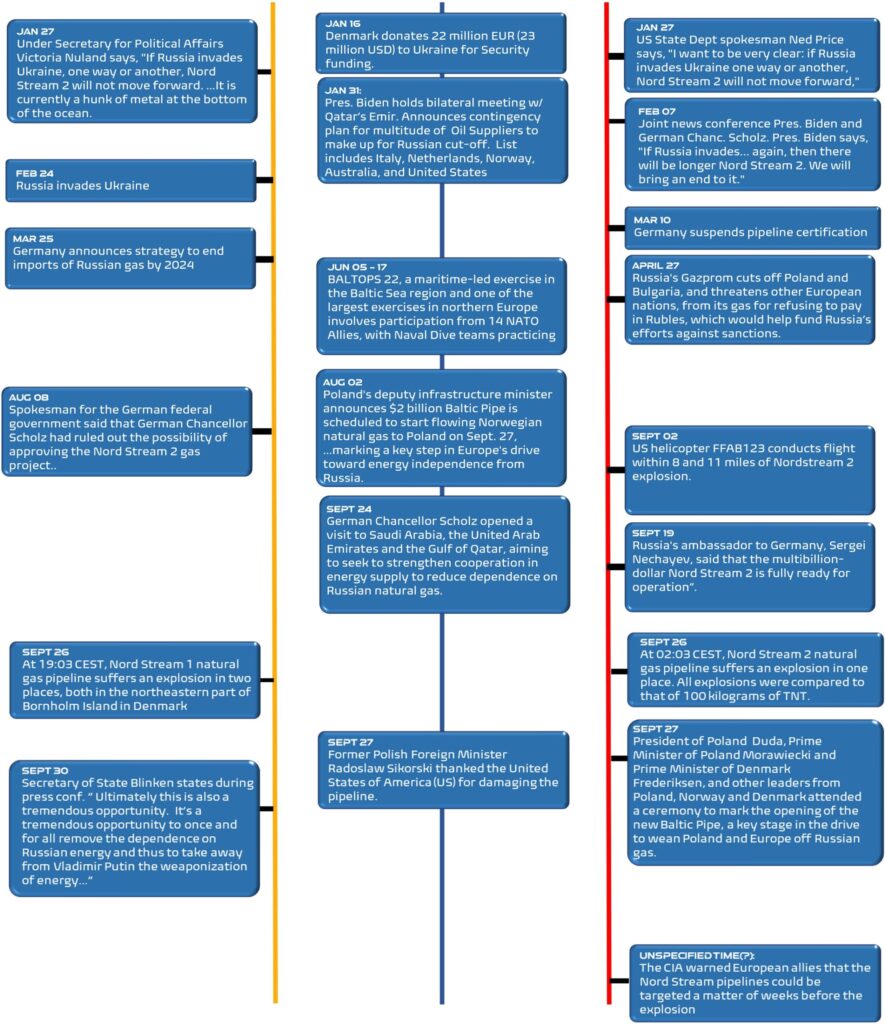
Timeline:
Assessment
Due to the inoperable pipelines, cyber-attacks by Russia could increase to make up for financial losses. Additionally, attempts at cyber disruption and sabotage against NATO, particularly the US, are likely to occur as reprisal since target countries are less likely to respond with a kinetic response to a cyber threat.
VerSprite Threat Intelligence Group (TIG) determined that there is room for continued escalation, resulting in both physical and cyber risk to assets, particularly any assets belonging to the energy industry. For example, in early 2022, an undersea cable linking the Norwegian archipelago of Svalbard to mainland Norway was suddenly cut. Undersea cables have been frequently damaged throughout recent years (150-200 disruptions a year) yet are typically damaged by commercial ships and natural disasters. This 2022 disruption, on the other hand, was considered to have human involvement. Experts are concerned because undersea fiber optics carry 95% of international data.
Russia is known for utilizing info-stealing malware against Ukrainian targets. Developing new malware is a time-consuming task. Threat actors need time to become familiar with the new malware and develop tactics for effective deployment. As a result, existing malware may be deployed to a broader range of targets as Russia escalates with a more significant number of countries.
The last impactful campaign attributed to Russian-associated threat actors was ransomware attacks on industry-leading organizations (JBS/Colonial Pipeline). Analysts believe that attack was an attempt to help fund their conflict against Ukraine. Although Russia claimed to arrest those responsible for those attacks, the Russian government is known for using similar deception techniques in the past.
As a part of its strategy, the Russian government deploys a Hybrid Threat model, using cybercrime gangs to commit these attacks. It takes a large portion of the funds from those attacks and then arrests the cybercrime gang and confiscates the money.
These campaigns exposed four different types of ransomware strategies:
- The first involves encrypting the victim’s data for ransom.
- The second involves encrypting the data for ransom and threatening to post that data on dark web marketplaces if the ransom is not paid.
- The third strategy is encrypting, posting in marketplaces, and taking the collected information, like business emails and vendor information so that they can pivot to a third party for the next attack.
- The fourth strategy attempts to skip reconnaissance and initial access stages by recruiting and grooming potential insider threats to deploy malware on internal systems.
This last strategy sought to exploit the contentious economic atmosphere during the pandemic when many employees were furloughed or at risk of termination due to the workforce reduction plans that companies implemented to stay in business. VerSprite TIG team predicts an increased probability of seeing Russian-associated threat actors reusing the previously mentioned strategies in their new ransomware campaigns because they will need to make up for the loss of funding after the sabotage of the Nordstream pipelines.
Organizations will likely see an increase in those ransomware attempts, as many organizations are again susceptible to the economic downturn, forcing many to lay off around the turn of the fiscal year.
Ukraine does not have the capability of the US and the greater EU community to mitigate and prevent cyber-attacks due to a persistent military offensive within the country. The use of commodity malware on less technically advanced countries, like Ukraine, encourages the targeting of less technically sophisticated targets. Other eastern EU members are more likely to be the victims of their subsequent attacks.
Because Ukrainian assets have fewer resources to maintain patches, tools leveraged against them have a greater chance to successfully exploit systems with outdated software patches. While this could prevent these tools from being successful against new victims in the US and EU, a strong security posture and patch management policy will be required to gain any advantage.
Resources:
DW.COM. 2022. Fact check: US helicopter flight no proof of sabotage of Nord Stream pipeline | DW | 30.09.2022. [online] Available at: <https://www.dw.com/en/fact-check-us-helicopter-flight-no-proof-of-sabotage-of-nord-stream-pipeline/a-63295189> [Accessed 6 October 2022].2022. [online] Available at: <https://www.euronews.com/2022/09/27/baltic-pipe-norway-poland-gas-pipeline-opens-in-key-move-to-cut-dependency-on-russia> [Accessed 5 October 2022].
Ahlander, J. and Solsvik, T., 2022. Sweden sends diving vessel to probe leaking Nord Stream pipelines. [online] Reuters.com. Available at: <https://www.reuters.com/business/energy/russias-gazprom-says-pressure-nord-stream-pipelines-has-stabilised-2022-10-03/> [Accessed 6 October 2022].Aljazeera.com. 2022. EU, NATO say Nord Stream gas pipelines were sabotaged. [online] Available at: <https://www.aljazeera.com/news/2022/9/28/nord-stream-pipeline-damage-not-a-concidence-says-eu> [Accessed 6 October 2022].
COLE, B., 2022. Russian Railway Executive Found Shot to Death on His Balcony. [online] Newsweek. Available at: <https://www.newsweek.com/russia-ukraine-death-pchelnikov-shot-war-1747535> [Accessed 6 October 2022].
Csis.org. 2022. Security Implications of Nord Stream Sabotage. [online] Available at: <https://www.csis.org/analysis/security-implications-nord-stream-sabotage> [Accessed 5 October 2022].
dma.dk. 2022. Nautical information. [online] Available at: <https://dma.dk/safety-at-sea/navigational information/nautical-information> [Accessed 6 October 2022].
DW.COM. 2022. Fact check: US helicopter flight no proof of sabotage of Nord Stream pipeline | DW | 30.09.2022. [online] Available at: <https://www.dw.com/en/fact-check-us-helicopter-flight-no-proof-of-sabotage-of-nord-stream-pipeline/a-63295189> [Accessed 6 October 2022].
English, A., 2022. US military aircraft circled Nord Stream incident site in September. [online] Al Mayadeen English. Available at: <https://english.almayadeen.net/news/politics/us-military-aircraft-circled-nord-stream-incident-site-in-se> [Accessed 5 October 2022].
Ensor, B., 2022. Nuclear weapons convoy sparks fears Putin could be preparing test to send ‘signal to the West’. [online] The Telegraph. Available at: <https://www.telegraph.co.uk/world-news/2022/10/03/nuclear-weapons-convoy-sparks-fears-putin-could-preparing-test/> [Accessed 6 October 2022].
Hogg, R., 2022. NATO threatens to retaliate against suspected Nord Stream sabotage, ratcheting up tension with Russia. [online] Business Insider. Available at: <https://www.businessinsider.com/fourth-leak-found-nord-stream-pipeline-after-acts-sabotage-nato-2022-9?r=US&IR=T> [Accessed 6 October 2022].
Ilascu, I., 2022. Russian hackers use new info stealer malware against Ukrainian orgs. [online] BleepingComputer. Available at: <https://www.bleepingcomputer.com/news/security/russian-hackers-use-new-info-stealer-malware-against-ukrainian-orgs/> [Accessed 6 October 2022].
Kochis, D., 2022. Russia’s Attack on Nord Stream Pipelines Means Putin Has Truly Weaponized Energy. [online] The Heritage Foundation. Available at: <https://www.heritage.org/global-politics/commentary/russias-attack-nord-stream-pipelines-means-putin-has-truly-weaponized> [Accessed 5 October 2022].
Krzysztoszek, A., 2022. Baltic Pipe gas pipeline opens, connects Norway and Poland. [online] www.euractiv.com. Available at: <https://www.euractiv.com/section/energy-environment/news/baltic-pipe-gas-pipeline-opens-connects-norway-and-poland/> [Accessed 6 October 2022].
McFall, C., 2022. State Dept vows Nord Stream 2 will be a ‘hunk of metal at bottom of the ocean’ if Russia invades Ukraine. [online] Fox News. Available at: <https://www.foxnews.com/politics/state-dept-vows-nord-stream-2-hunk-metal-bottom-ocean-russia-invades-ukraine> [Accessed 6 October 2022].
Nytimes.com. 2022. The C.I.A. had warned European governments of potential attacks on pipelines.. [online] Available at: <https://www.nytimes.com/2022/09/27/world/europe/cia-nord-stream-pipelines-attack.html> [Accessed 5 October 2022].
Plucinska, J., 2022. Who’s To Blame For The Nord-Stream Gas Pipeline Leak?. [online] gCaptain. Available at: <https://gcaptain.com/whos-to-blame-for-the-nord-stream-gas-pipeline-leak/> [Accessed 6 October 2022].
reuters.com. 2022. Nord Stream 1 gas leak expected to continue until Sunday. [online] Available at: <https://www.reuters.com/business/energy/nord-stream-1-gas-leak-expected-continue-until-sunday-2022-09-30/> [Accessed 6 October 2022].
Sandford, A., 2022. Baltic Pipe: Norway-Poland gas pipeline opens in key move to cut dependency on Russia. [online] euronews.com. Available at: <https://www.euronews.com/2022/09/27/baltic-pipe-norway-poland-gas-pipeline-opens-in-key-move-to-cut-dependency-on-russia> [Accessed 6 October 2022].
Stewart, W., 2022. NATO ‘warns Putin may test a NUKE on Ukraine’s borders’. [online] Mail Online. Available at: <https://www.dailymail.co.uk/news/article-11278341/Putin-preparing-make-decision-launching-tactical-nuclear-strike-say-Kremlin-insiders.html> [Accessed 6 October 2022].
Stewart, W., 2022. Putin ‘deploys Belgorod nuclear sub’ amid sabre-rattling over Ukraine. [online] Mail Online. Available at: <https://www.dailymail.co.uk/news/article-11274113/Putin-deploys-Belgorod-nuclear-submarine-amid-sabre-rattling-Ukraine.html?ito=social-twitter_mailonline.> [Accessed 6 October 2022].
The Guardian. 2022. Nord Stream 1: Gazprom announces indefinite shutdown of pipeline. [online] Available at: <https://www.theguardian.com/business/2022/sep/02/nord-stream-1-gazprom-announces-indefinite-shutdown-of-pipeline> [Accessed 6 October 2022].
Vakulenko, S., 2022. Shock and Awe: Who Attacked the Nord Stream Pipelines?. [online] Carnegie Endowment for International Peace. Available at: <https://carnegieendowment.org/politika/88062> [Accessed 5 October 2022].
Washingtonpost.com. 2022. Opinion Undersea pipeline sabotage demands the West prepare for more attacks. [online] Available at: <https://www.washingtonpost.com/opinions/2022/10/04/gas-pipeline-sabotage-russia-ukraine-response/> [Accessed 5 October 2022].
https://www.theglobeandmail.com/world/article-biden-designates-qatar-major-non-nato-ally-as-energy-crisis-looms/
https://www.bbc.com/news/world-europe-60151839
https://dgap.org/en/research/publications/nord-stream-2-dead-end-germanys-ostpolitik
https://www.foxnews.com/politics/state-dept-vows-nord-stream-2-hunk-metal-bottom-ocean-russia-invades-ukraine
https://www.promoteukraine.org/denmark-allocates-additional-eur-22m-for-ukraines-security-sector/
https://www.reuters.com/business/energy/gazprom-says-it-halts-gas-supplies-poland-bulgaria-payments-row-2022-04-27/
https://www.ccfgroup.com/newscenter/newsview.php?Class_ID=D00000&Info_ID=2022092930078
https://www.state.gov/secretary-antony-j-blinken-and-canadian-foreign-minister-melanie-joly-at-a-joint-press-availability/
https://de.flightaware.com/live/flight/FFAB123/history/20220902/0557Z
https://intellectualtakeout.org/2020/06/1984-interview-explains-the-ideological-subversion-of-america/?print=print
PASTA Threat Modeling: The Process for Attack Simulation and Threat Analysis
VerSprite leverages our PASTA (Process for Attack Simulation and Threat Analysis) methodology to apply a risk-based approach to threat modeling. This methodology integrates business impact, inherent application risk, trust boundaries among application components, correlated threats, and attack patterns that exploit identified weaknesses from the threat modeling exercises.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /