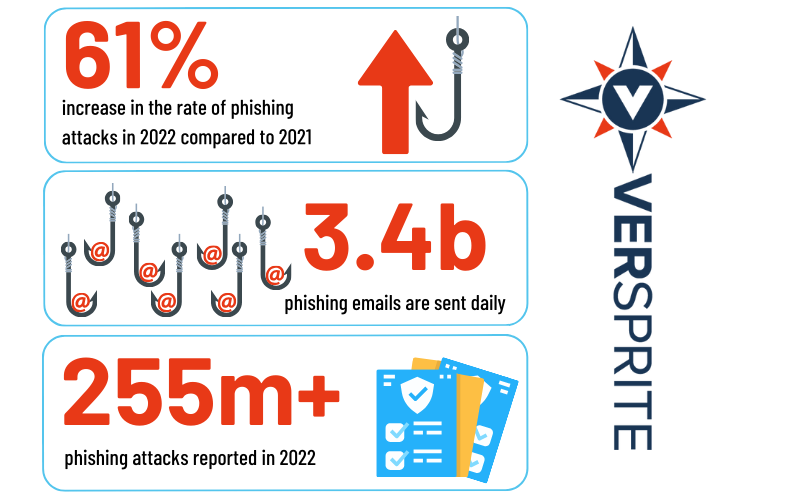
Domain Spoofing and Phishing Attacks
Minimize phishing cyberattacks and prevent domain spoofing with these three settings: SPF, DKIM, and DMARC
by Mike Charette, VerSprite Security Consultant
Email security is of utmost importance in today’s digital world, as cybercriminals increasingly use phishing scams and other malicious tactics to gain access to sensitive information. Domain spoofing, where the “From” field of an email is manipulated to appear as though it came from a trusted source, is a common technique used by attackers. To prevent domain spoofing, it is essential to set up SPF, DKIM, and DMARC. In this article, we’ll walk through the steps to set up these email security protocols.
SPF (Sender Policy Framework) is an email authentication method that allows domain owners to specify which mail servers are authorized to send an email on their behalf. This helps email servers determine whether the incoming email is genuine by checking the SPF record of the sending domain. Setting up an SPF record involves adding a TXT record to your domain’s DNS records that list the authorized mail servers for your domain.
DKIM (DomainKeys Identified Mail) is another email authentication protocol that uses digital signatures to verify that an email message has not been modified during transit. When an email is sent, the sender’s mail server signs the message using a private key and attaches a signature. When the recipient’s mail server receives the message, it uses the sender’s public key to verify the signature and determine whether it has been modified in transit.
DMARC (Domain-based Message Authentication, Reporting & Conformance) is an email authentication protocol that builds on the authentication methods provided by SPF and DKIM. DMARC allows domain owners to specify how receiving mail servers should handle incoming email that fails SPF or DKIM checks. For example, a domain owner can instruct receiving mail servers to reject, quarantine, or accept messages that fail the SPF or DKIM checks.
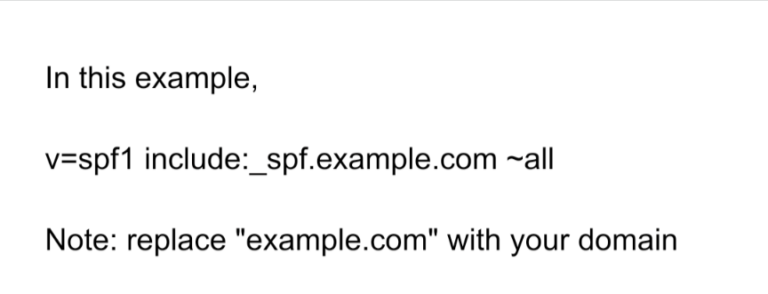
Steps to set up SPF:
- Determine the list of mail servers authorized to send an email on behalf of your domain.
- Log in to your domain’s DNS management service.
- Add a new TXT record to your domain’s DNS records.
- Enter the following SPF record, replacing “example.com” with your domain name and listing the authorized mail servers for your domain: “v=spf1 mx a ip4:<authorized mail server IP addresses> -all”
- Save the changes to your DNS records.
Steps to set up DKIM:
- Generate a public/private key pair using a DKIM key generator tool.
- Log in to your domain’s DNS management service.
- Add a new TXT record to your domain’s DNS records.
- Enter the following DKIM record, replacing “example.com” with your domain name and the values generated by the DKIM key generator: “k=rsa; p=<public key>” Save the changes to your DNS records.
Steps to set up DMARC:
- Determine the desired policy for handling incoming email that fails SPF or DKIM checks (e.g., reject, quarantine, or accept).
- Log in to your domain’s DNS management service.
- Add a new TXT record to your domain’s DNS records.
- Enter the following DMARC record, replacing “example.com” with your domain name and the desired policy for handling incoming email: “v=DMARC1; p=<desired policy>; pct=100; rua=mailto: [email protected]“
- Save the changes to your DNS records.
In conclusion, setting up SPF, DKIM, and DMARC is crucial in enhancing email security and preventing domain spoofing. By verifying the authenticity of incoming emails, these protocols help prevent phishing scams and other malicious attacks that use domain spoofing as a tactic. Implementing these protocols may require technical knowledge, so consulting an IT professional is advisable.
VerSprite Threat Intelligence Group can help your organization avoid BEC (business email compromise) and harden your email environment. Contact us today.
PASTA Threat Modeling: The Process for Attack Simulation and Threat Analysis
VerSprite leverages our PASTA (Process for Attack Simulation and Threat Analysis) methodology to apply a risk-based approach to threat modeling. This methodology integrates business impact, inherent application risk, trust boundaries among application components, correlated threats, and attack patterns that exploit identified weaknesses from the threat modeling exercises.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /