Automating Playbooks in D3
Author: Neeraj Kumar Sharma, VerSprite Threat Intelligence Group Analyst, X handle @NeerajK85400479
In this blog, I share some practical insights I’ve gained from working with automation in D3 over the past couple of years. We’ll dive into the nitty-gritty of automating your playbook deployment from A to Z. But before we get into the details of automating playbooks in D3, let’s ensure we’re all on the same page about what SOAR is.
Security Orchestration, Automation, and Response (SOAR) is a set of practices and technologies designed to improve the efficiency and effectiveness of an organization’s cybersecurity operations. It integrates and coordinates the activities of various security tools, streamlining incident detection, investigation, and response processes. SOAR is all about making your cybersecurity operations more efficient and effective.
So, what are the key components of SOAR?
- Orchestration: This involves the coordination and sequencing of automated security processes and workflows. It ensures that different security tools and systems work together synchronously. For example, if a suspicious activity is detected, the SOAR system can automatically trigger a series of actions, such as isolating the affected system, collecting additional data, and notifying relevant personnel.
- Automation: Automation involves the use of technology to perform tasks or actions without human intervention. In the context of cybersecurity, this can include tasks like threat detection, data enrichment, and response actions. Automation helps to reduce the manual effort required to respond to security incidents.
- Response: This component focuses on the actions taken to address and mitigate security incidents. It includes a range of activities such as containment, eradication of threats, recovery of systems, and communication with stakeholders.
Key benefits of implementing SOAR in a cybersecurity environment include:
- Improved Response Time: SOAR allows for near-instantaneous responses to security incidents, crucial in preventing or minimizing damage.
- Consistency: Automated workflows ensure that responses are consistent and follow predefined procedures, reducing the likelihood of human error.
- Scalability: SOAR platforms can handle a large volume of incidents simultaneously, making them suitable for organizations of various sizes.
- Enhanced Visibility and Reporting: SOAR systems provide centralized dashboards and reporting capabilities, offering insights into the overall security posture and the effectiveness of incident response efforts.
- Resource Optimization: By automating routine tasks, security teams can focus on more complex and strategic activities, maximizing the value they bring to the organization.
Now, let’s talk about how D3 and SOAR work together:
D3 has two components that together deliver the SOAR capabilities: Automation Rules and Playbooks.
Automation Rules:
Automation rules have a defined trigger, some if/and/or statements, and then proceed to perform an action. We can create two types of Automation Rules in D3, Dismissal and Escalation. Dismissal Rules are the simplest: we just dismiss known incidents for reducing the noise in D3. In Escalation, we are mainly changing the properties of incidents like owners, tags, tasks, severities, and statuses and escalating them as an incident.
Playbooks:
A Playbook is a Logic App with a defined D3 trigger (incident, alert, entity). Being a Logic App, playbooks are capable of complex logic and operations outside the capabilities of Automation Rules. Let’s consider a simple SOAR playbook example for a common use case: phishing attacks. When a potential phishing email is detected, the playbook can automatically extract indicators of compromise (IOCs) such as IP addresses and hashes, cross-verify these IOCs with threat intelligence platforms like VirusTotal, and triage the threat accordingly.
Creating Your First Playbook
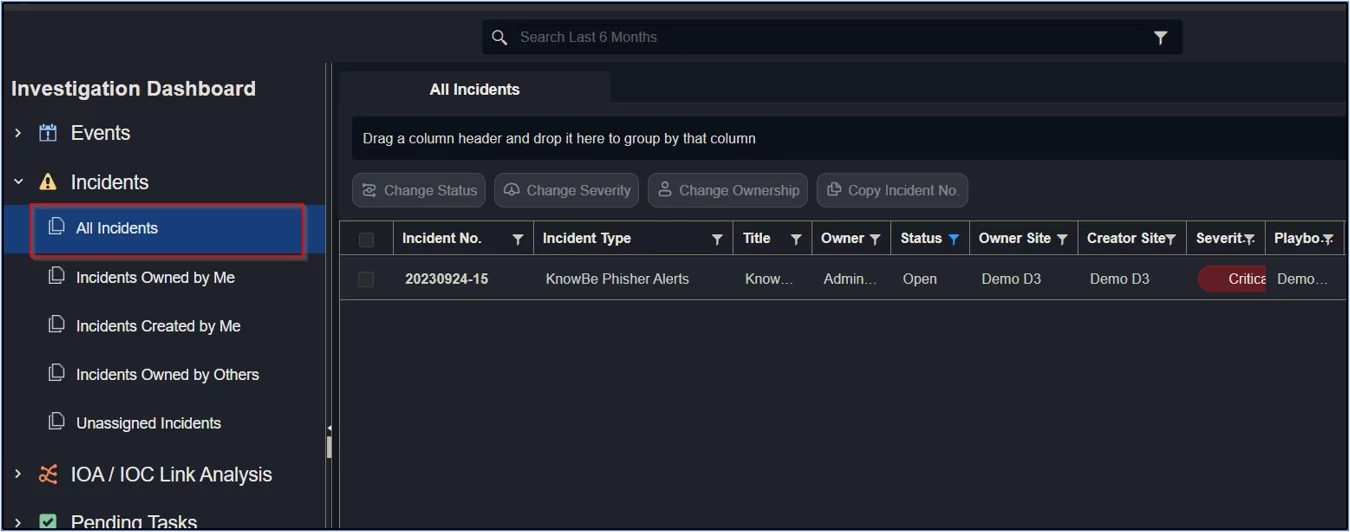
Since Playbooks require an incident as input to be run, they can’t be triggered using the standard Logic App UI. If you already have an incident, use it. Otherwise, escalate any events as an incident. You can set up an Escalation Rule for it also. We will go with manual escalation since we are doing it for a demo.
Now that we have an incident, we can start.
For this blog post, I am using a knowBe phisher alert of a Demo Organization, and I will use “DO” as an acronym.
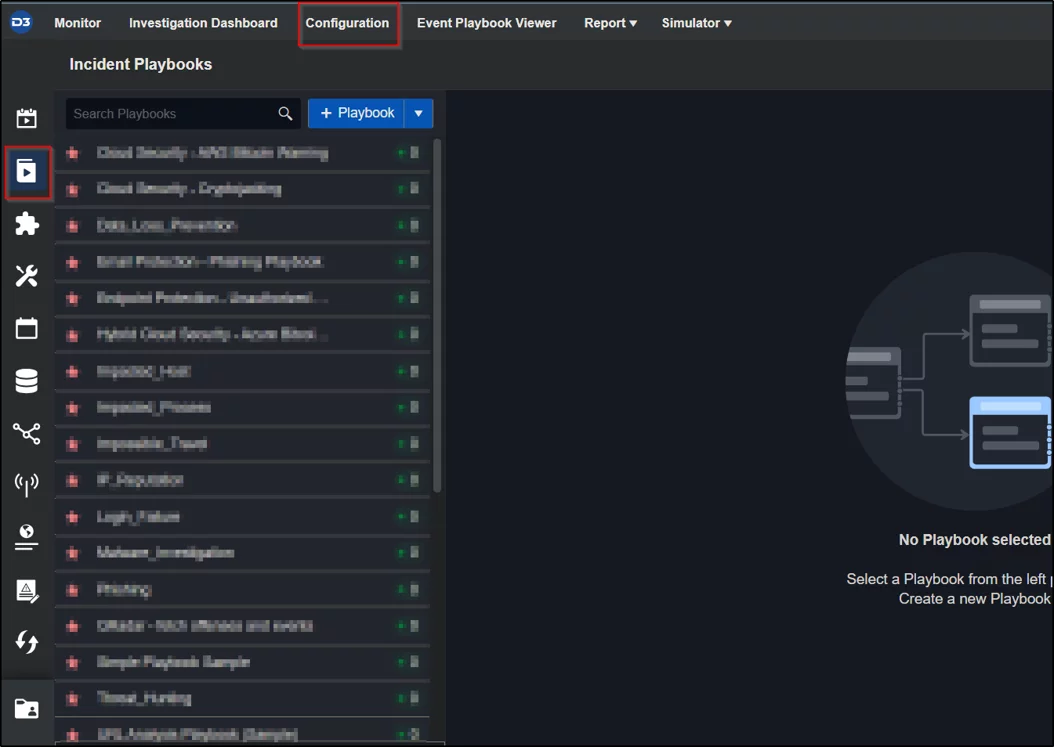
Go to Incident Playbooks under Configuration.
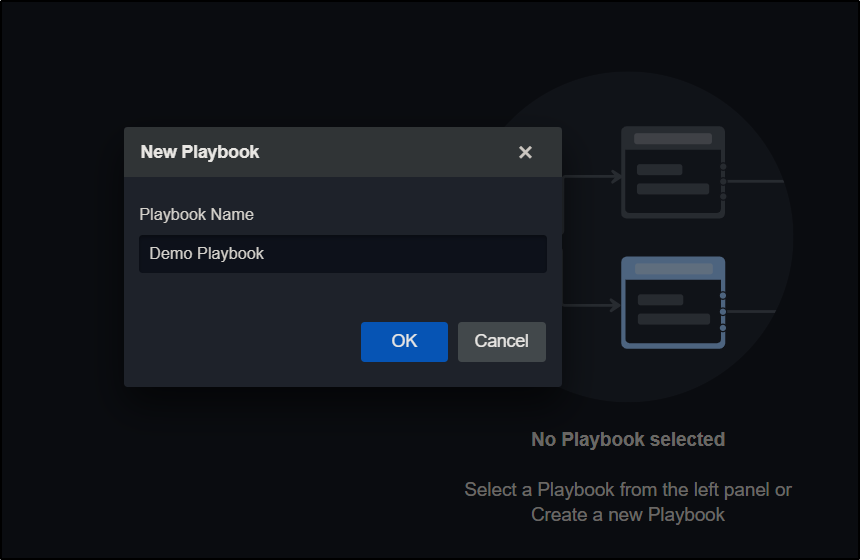
Click on +Playbook icon. You’ll see a prompt for entering the Playbook Name. I entered Demo Playbook as a Name and clicked OK.
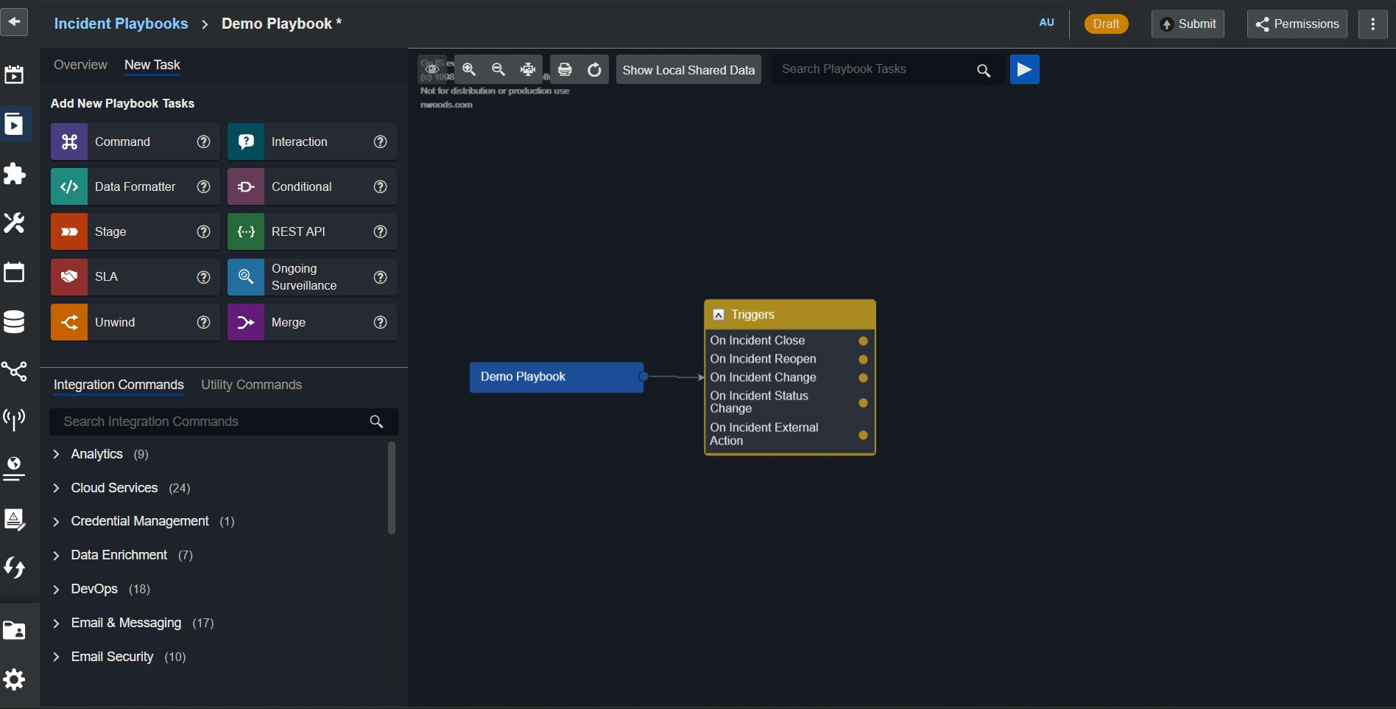
By default, we see something like this:
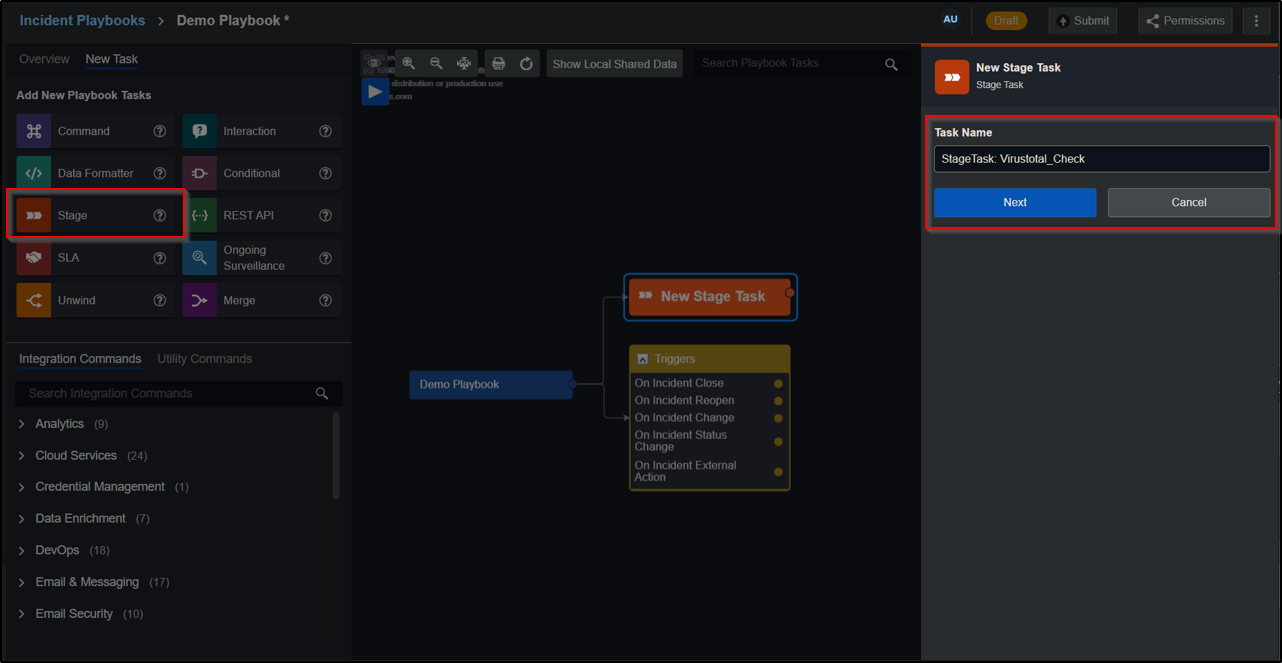
Select the stage task from the Task Panel. Once selected, it will come to the Main Editor, and the Task Detail window is open. Enter Stage Name like I added “StageTask: Virustotal_Check”. After that, click Correct.
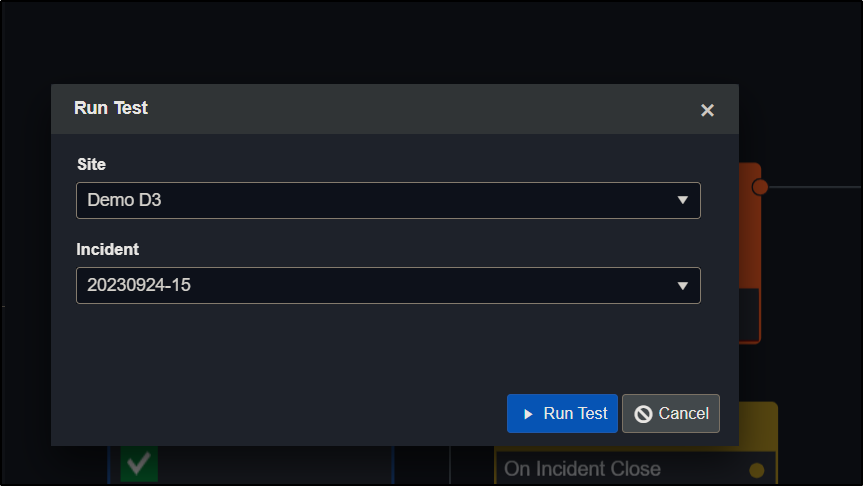
Now Select the stage task you just created and click the play button inside the Main editor window. Provide the site name and the incident we escalated manually or with the escalation rule. Here, I am using the KnowBe phishing alert for demo purposes. Once selected, click Run Test.
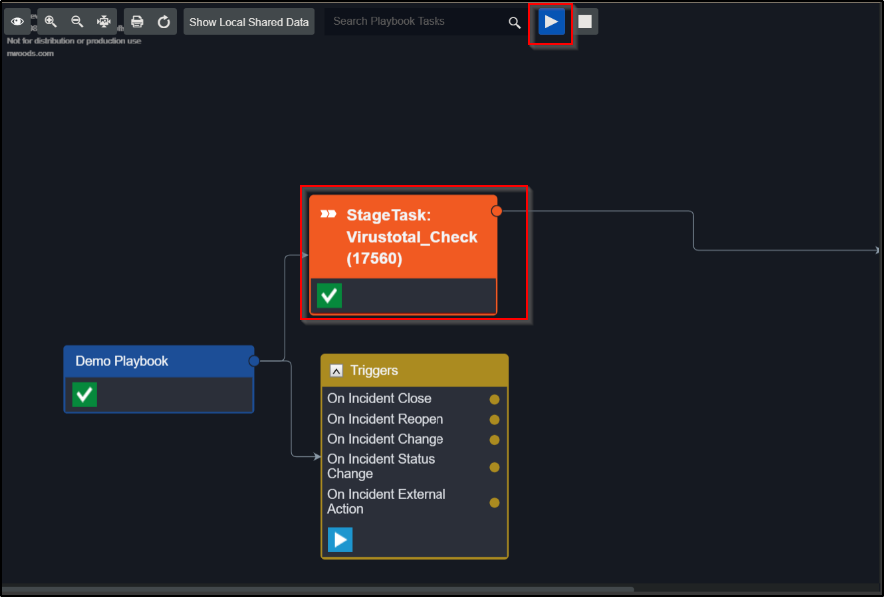
Once clicked, it asks for the Site Name and incident number. Choose accordingly. After that, click on Run Test.
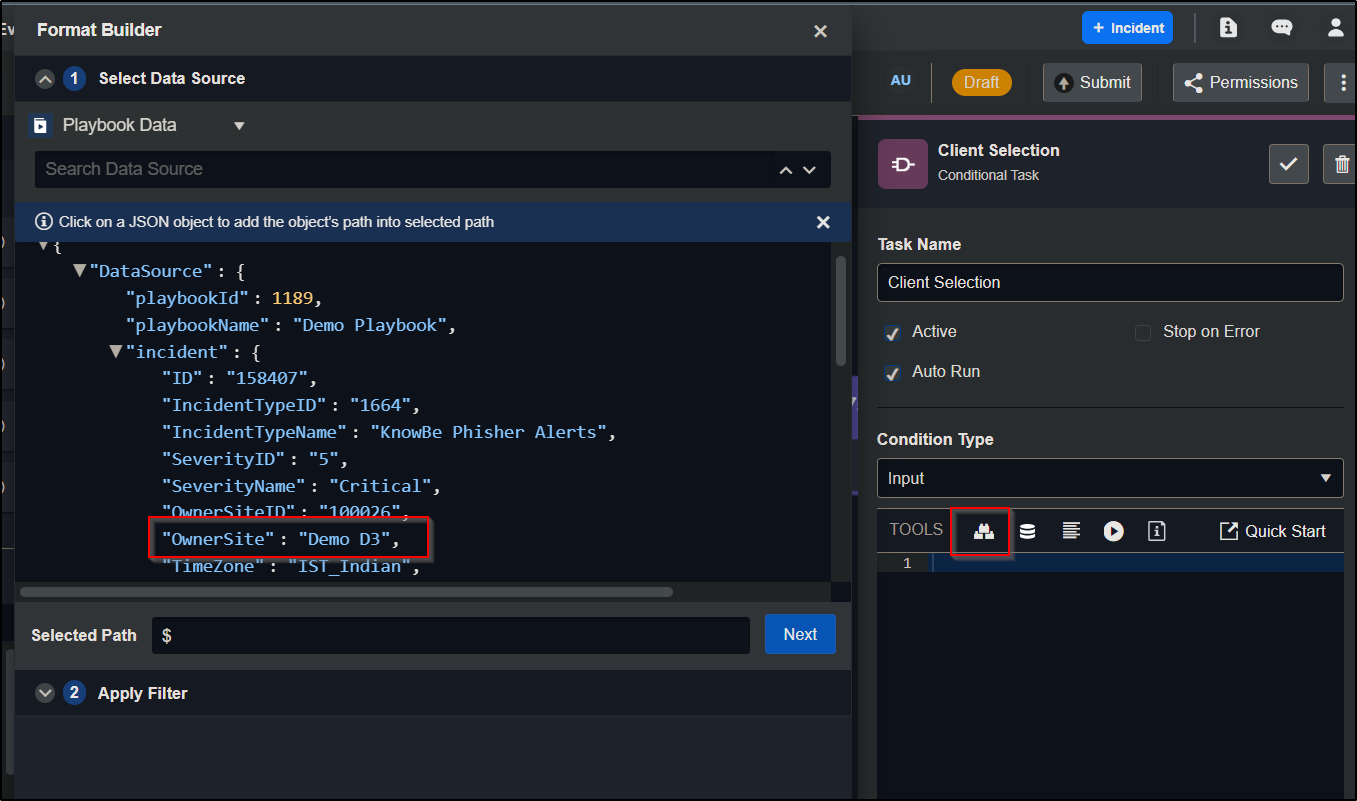
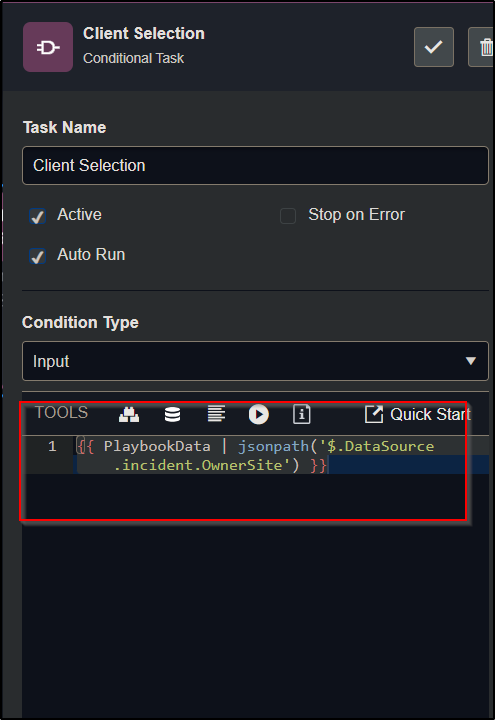
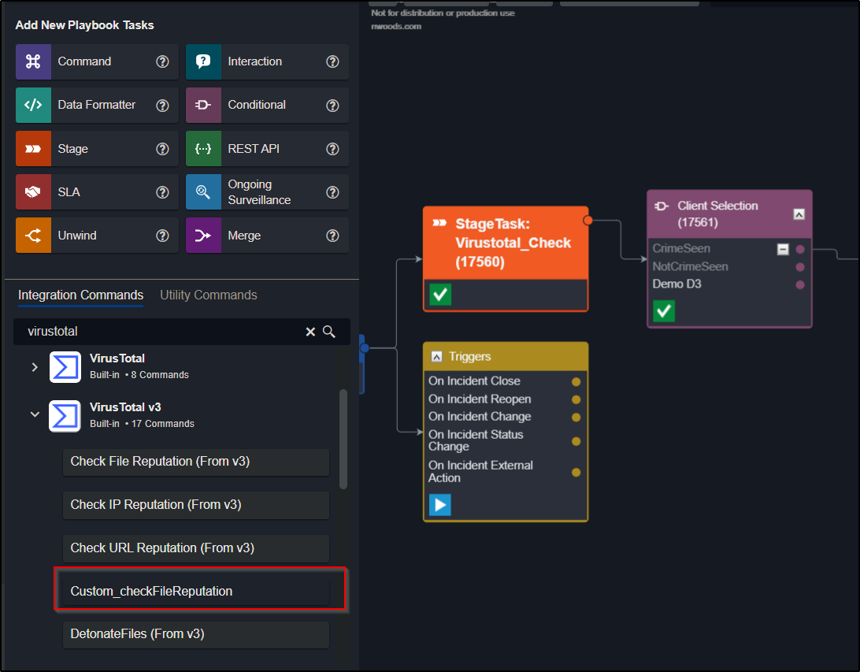
Now, we can directly create the check for virustotal. But I recommend making one conditional Task. It will help you to use the same playbook with different clients. So, I am creating a conditional task named Client Selection. For that, I choose the Conditional task and add data according to the need.
We also need the Client Selection. Under Condition Type, choose Input. In codeblock click FormatBuilder. After that, expand the DataSource and click on the data you want to use for the execution of the task. Right now, our goal is to select the Clients.
After selecting the Client, click on test, and once the test is passed, generate it.
You will see some code in the codeblock after generating.
After that, click Add Option, and add the client’s Name there.
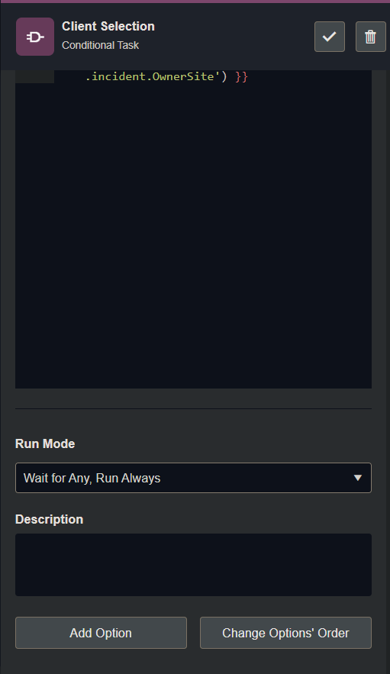
I added some clients for the blog purpose. Once the previous step is completed, click on the play button and repeat the process of checking. When the test is passed, you get this Green Tick Mark highlighting the Client.
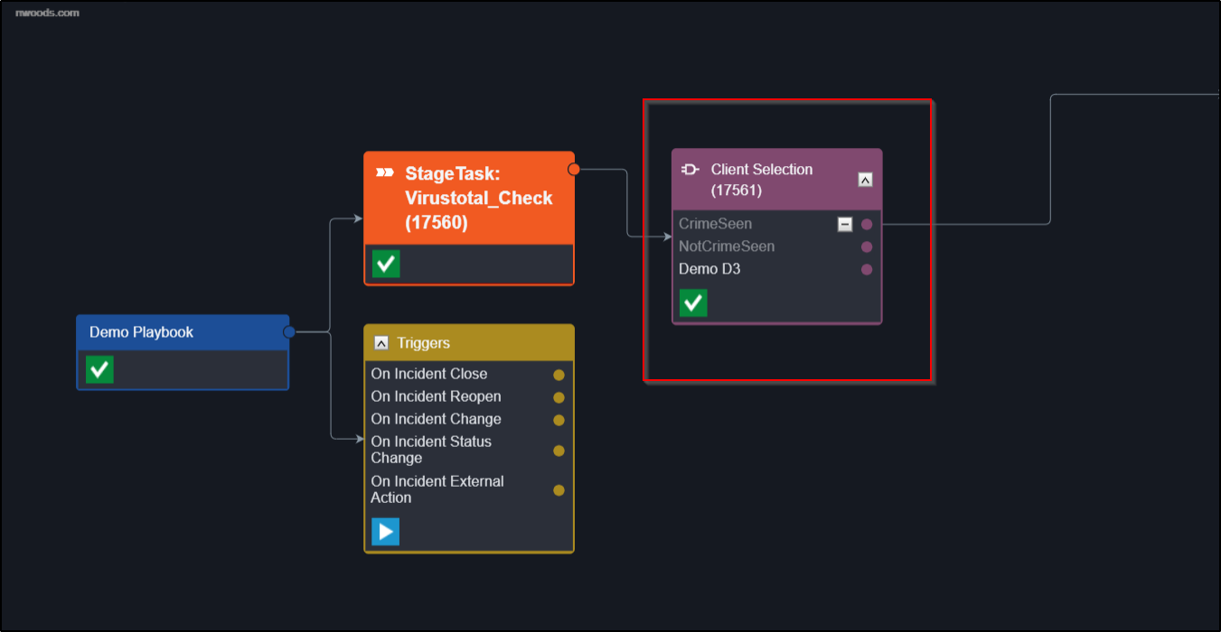
Click on the highlighted Client, and under Integration Commands, search for virustotal and drag and drop the Custom_checkFileReputation.
Add Task Name, and select the Auto Run option so it will automatically run the task.
Now, under Condition Type, choose Input. Under codeblock, click on FormatBuilder. After that, expand the DataSource and click on the data you want to use for the execution of the task. Right now, our goal is to check the File hash in virustotal.
After selecting the hash, click on test, and once the test is passed, generate it.
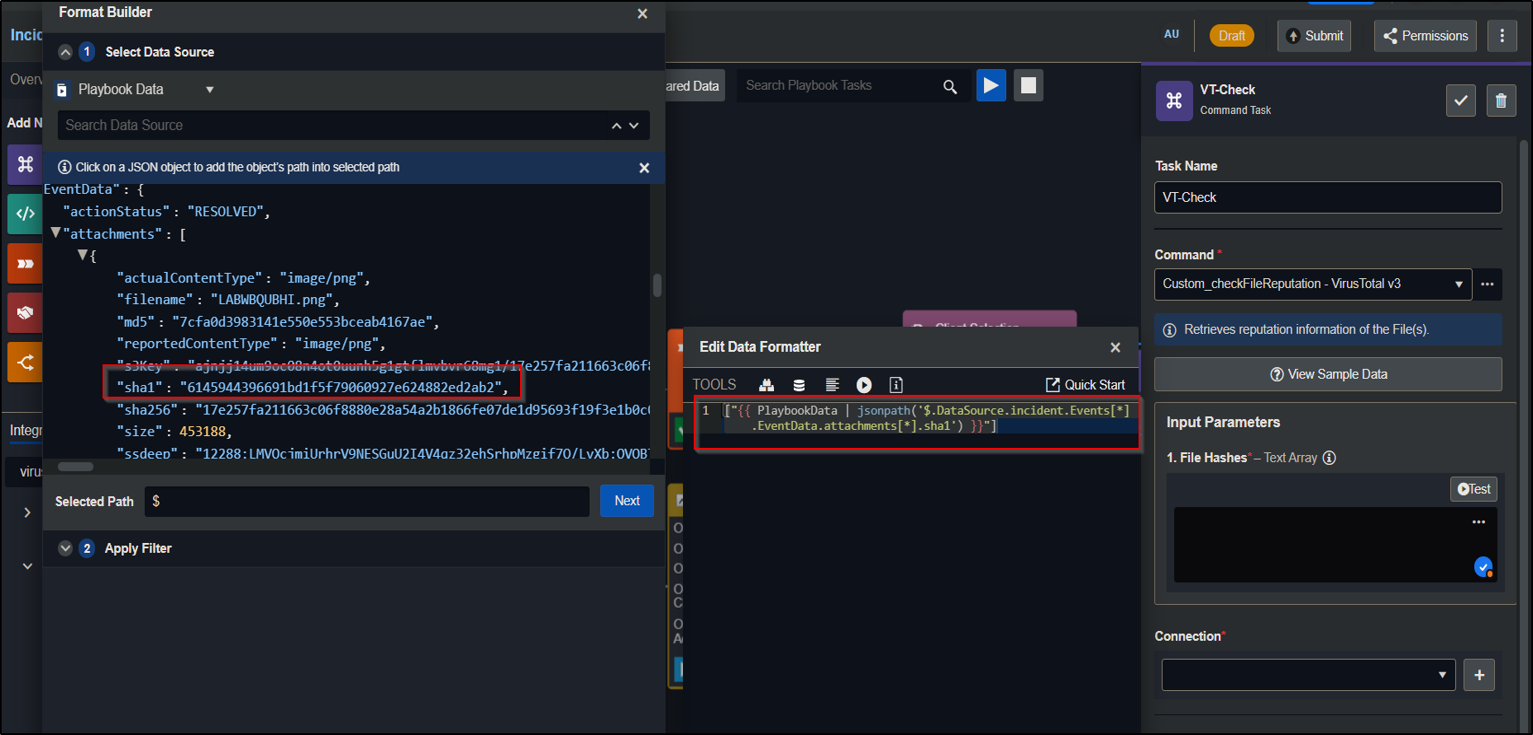
Once you have the code inside CodeBlocker, add the connection here.
I am creating a new connection with the name Demo D3. You can use an already-made one as well.
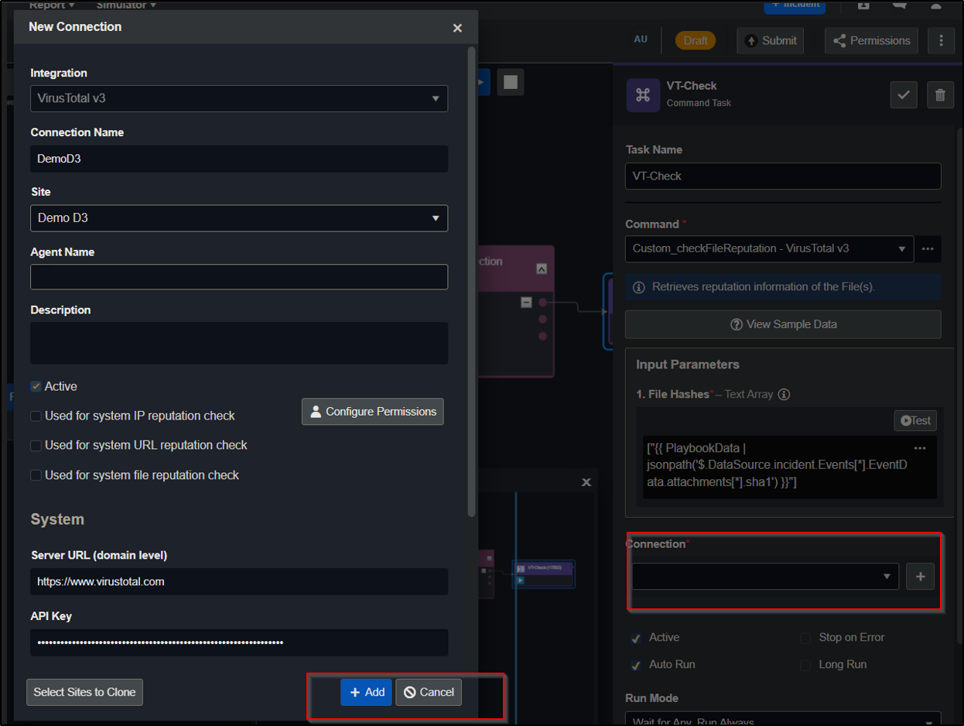
After adding the connection, click the Tick mark.
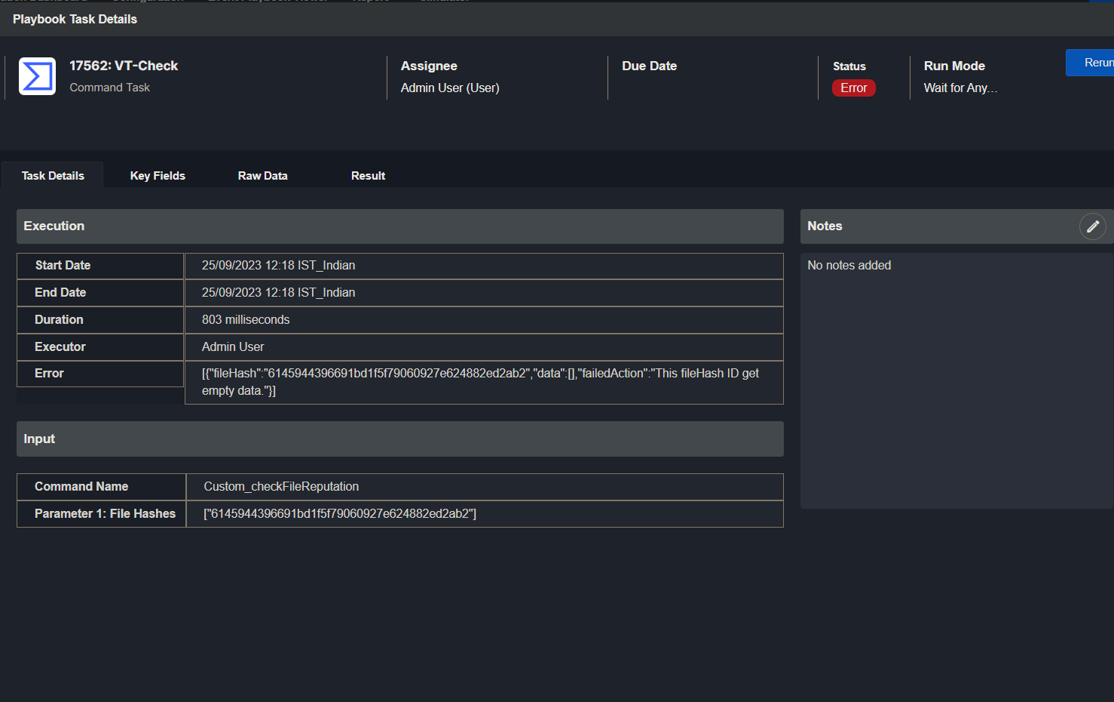
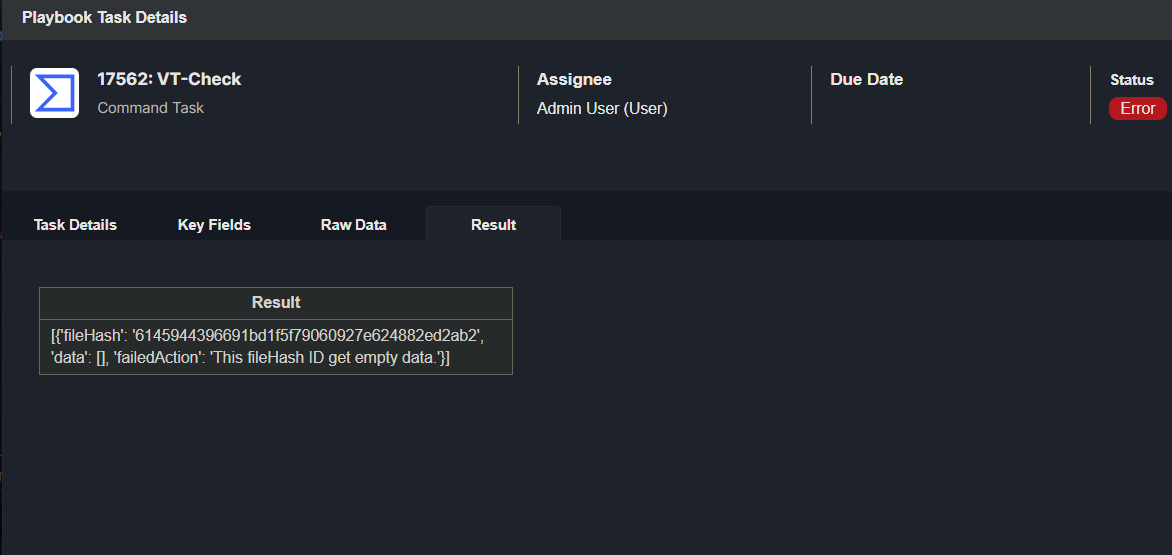
Run the task using the play button.
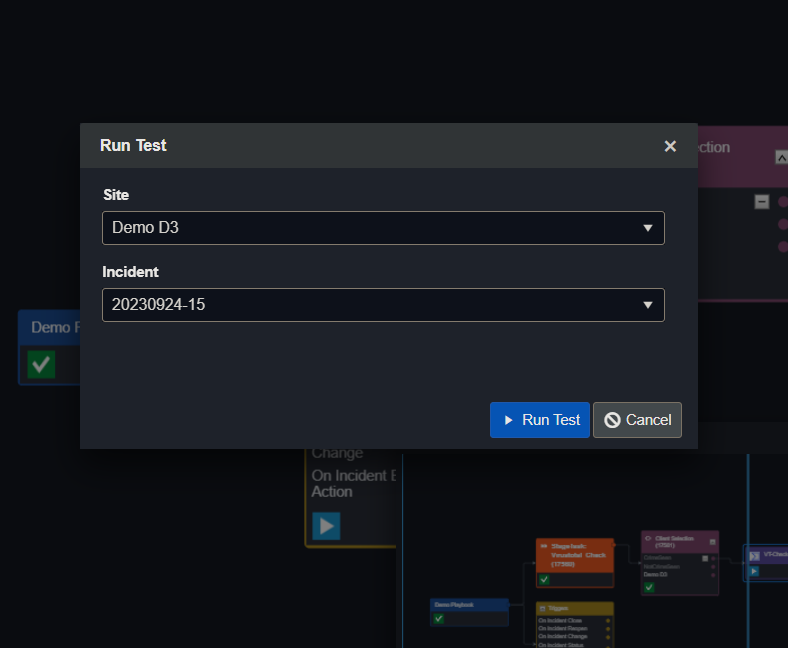
Click Run again.
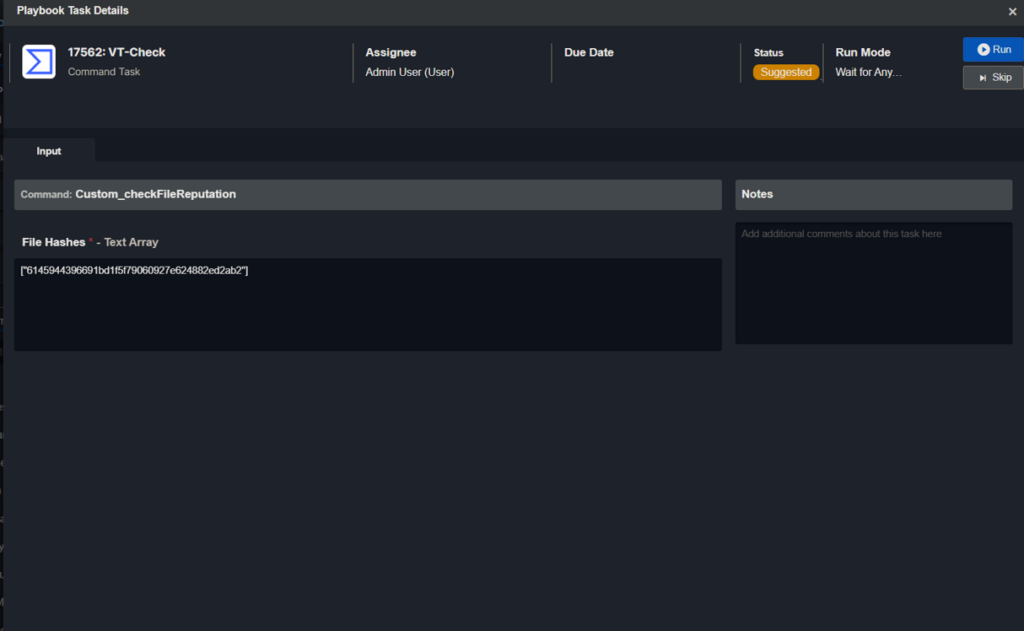
Once completed, it will show an error if the data returns empty. It will not produce an error if data is returned. Currently, with this incident, the file is not malicious; hence, we received an Error status code.
Now, you can add this playbook to the incidents and use it.
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /
- /